Choose a country or area to see content specific to your location
O que você está procurando?
-
-
Designer de interconexões 3D
O 3D Interconnect Designer oferece um ambiente flexível de modelagem e otimização para qualquer estrutura avançada de interconexão, incluindo chiplets, chips empilhados, pacotes e placas de circuito impresso (PCBs).

-
Economize até 50% na compra de um osciloscópio XR8
Obtenha uma validação digital mais rápida e por um preço menor com a troca de aparelhos.

-
Descubra o Keysight AI Data Center Builder
Emule todas as partes da infraestrutura do seu centro de dados. Emule tudo. Otimize tudo.

-
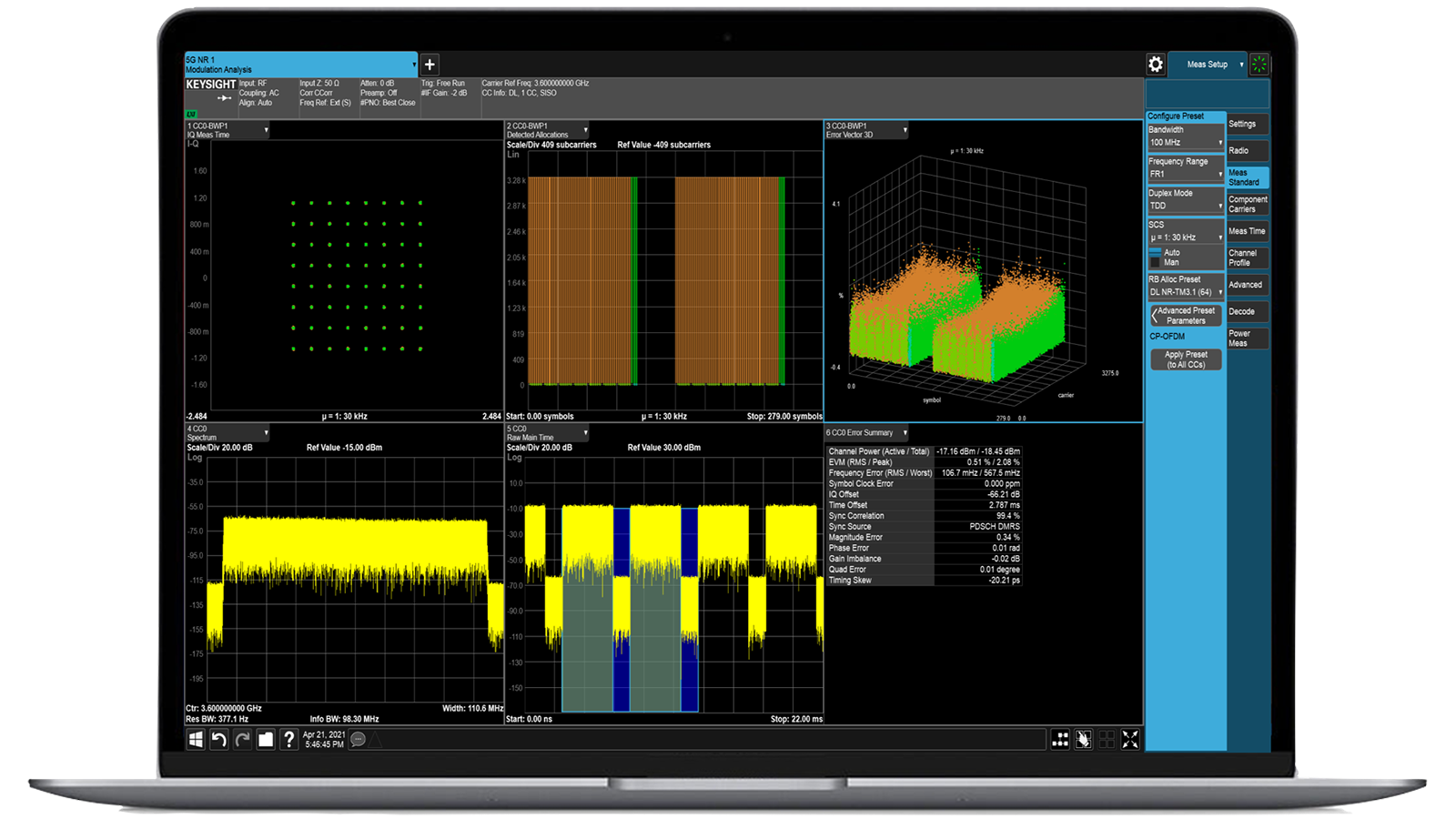
Acelere a análise de sinais com as aplicações de medição da Série X
Utilize mais de 25 aplicativos da Série X para analisar, demodular e solucionar problemas em sinais nas áreas de comunicações sem fio, aeroespacial/defesa, interferência eletromagnética (EMI) e ruído de fase.

-
Apresentando os corretores de pacotes aprimorados por IA
Com memória e armazenamento extras, esses NPBs aprimorados executam o software de segurança e monitoramento de desempenho de IA da Keysight e a pilha de IA.

-
Teste preciso em circuito para produção
Realize testes rápidos e precisos em nível de placa com ICT robusto em linha e fora de linha, projetado para a fabricação moderna.

-
Acelere seu mecanismo de inovação
Explore planos de suporte com curadoria, priorizados para mantê-lo inovando com velocidade.
-
-
Transmita dados I/Q de 120 MHz para o seu laptop em campoIdentifique interferências com software de gerenciamento de espectro pós-processamento em laboratório.
 Encontre a solução de alimentação ATE ideal
Encontre a solução de alimentação ATE idealUse esta ferramenta de seleção para identificar rapidamente a melhor fonte de alimentação para suas necessidades de ATE (Equipamentos de Teste Automático) nas áreas aeroespacial e de defesa.

-
- Soluções
-
Explore o conteúdo de autoria de engenheiros e uma vasta base de conhecimento com milhares de oportunidades de aprendizado.
O Keysight Learn oferece conteúdo imersivo sobre tópicos de interesse, incluindo soluções, blogs, eventos e muito mais.
-
Acesso rápido às tarefas de autoajuda mais frequentes relacionadas ao suporte.
Conteúdo adicional para atender às necessidades de seu produto.
Faça mais com os serviços da KeysightExplore os serviços para acelerar cada etapa de sua jornada de inovação.
Testes de segurança da IoT Simulação de ameaças reais à IoT para validação de segurança aprimorada
- Visão geral
- Todos os modelos
- Acessórios
- Software
- Suporte
Soluções robustas de validação de segurança para dispositivos conectados
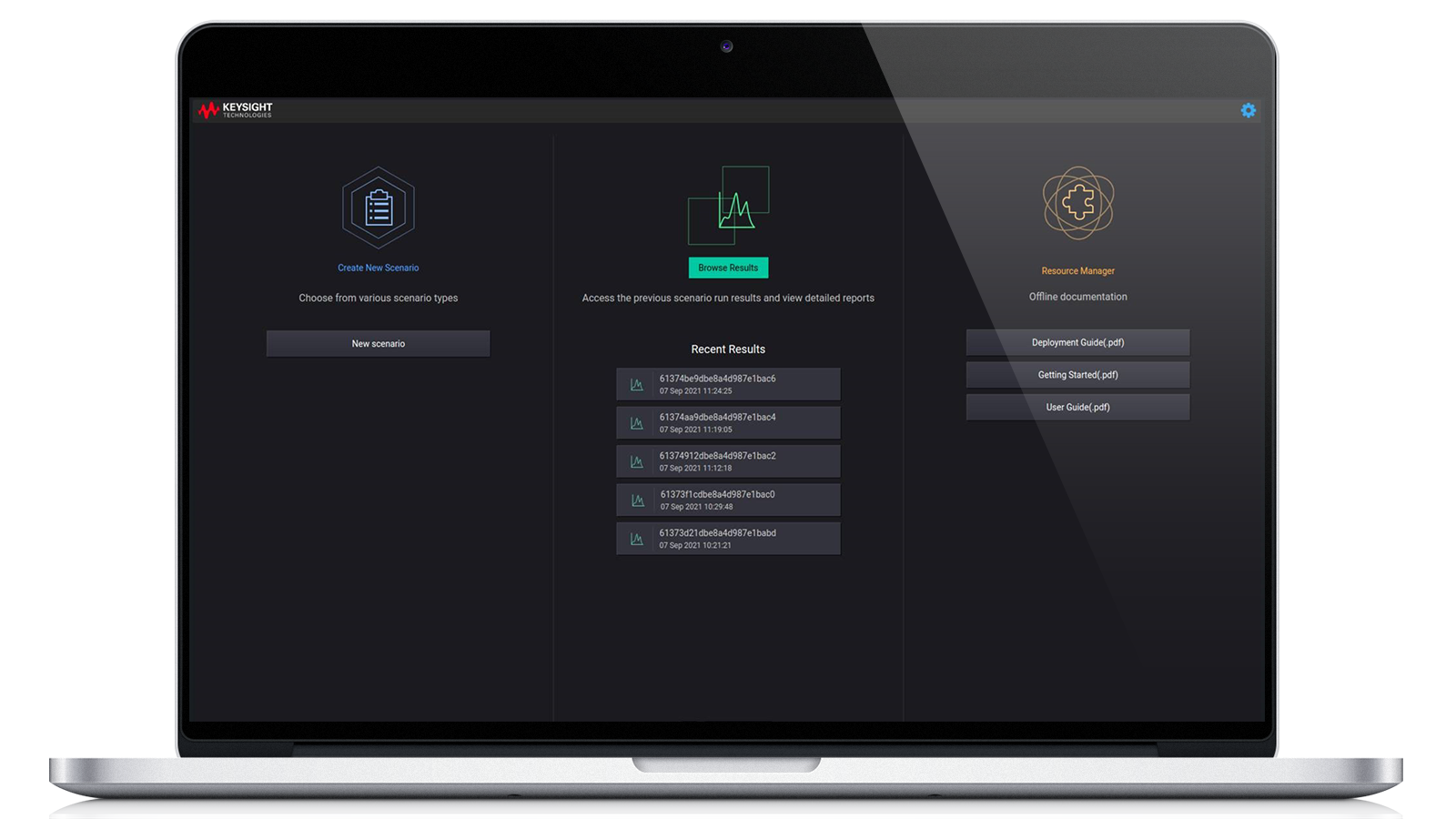
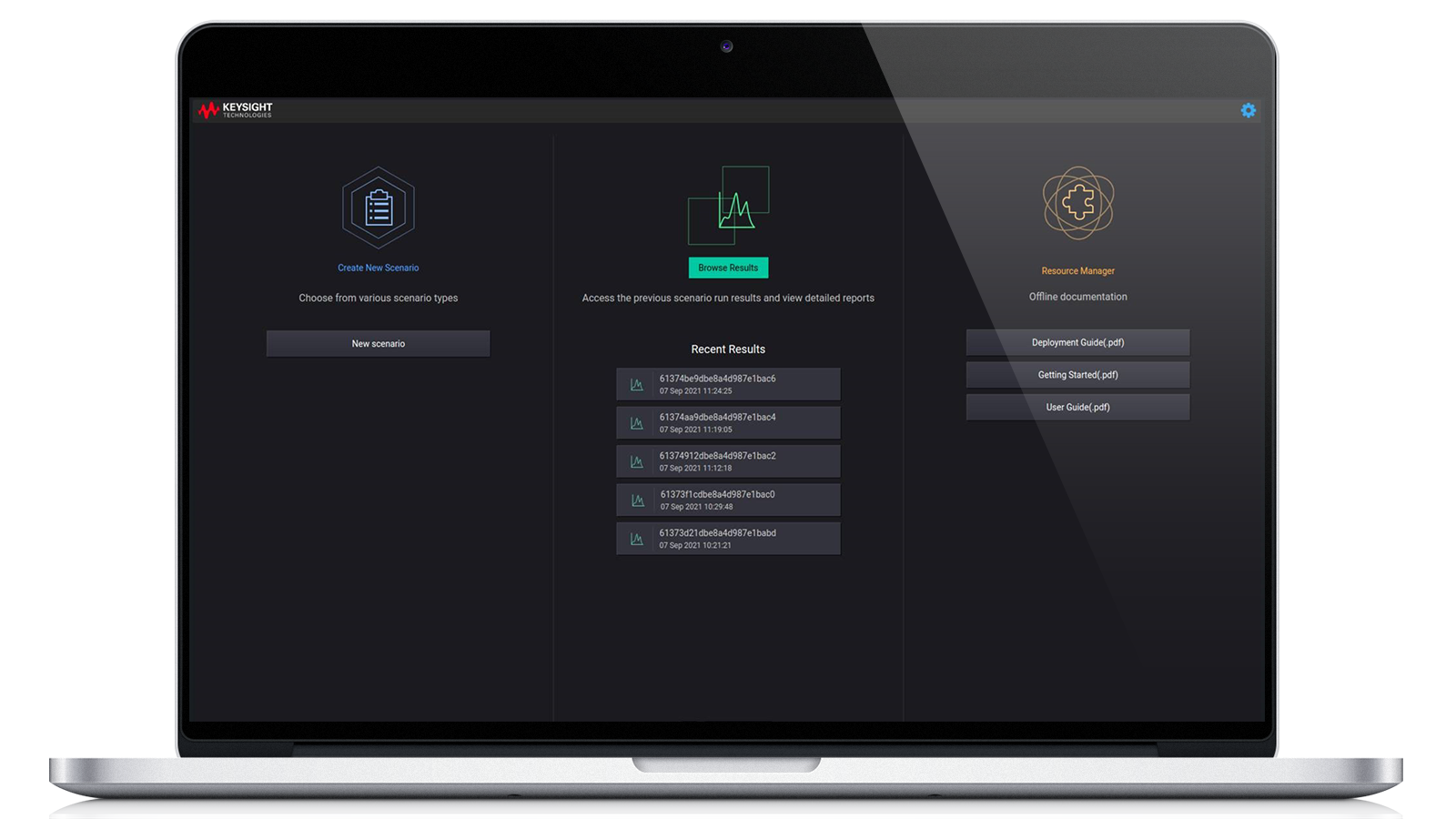
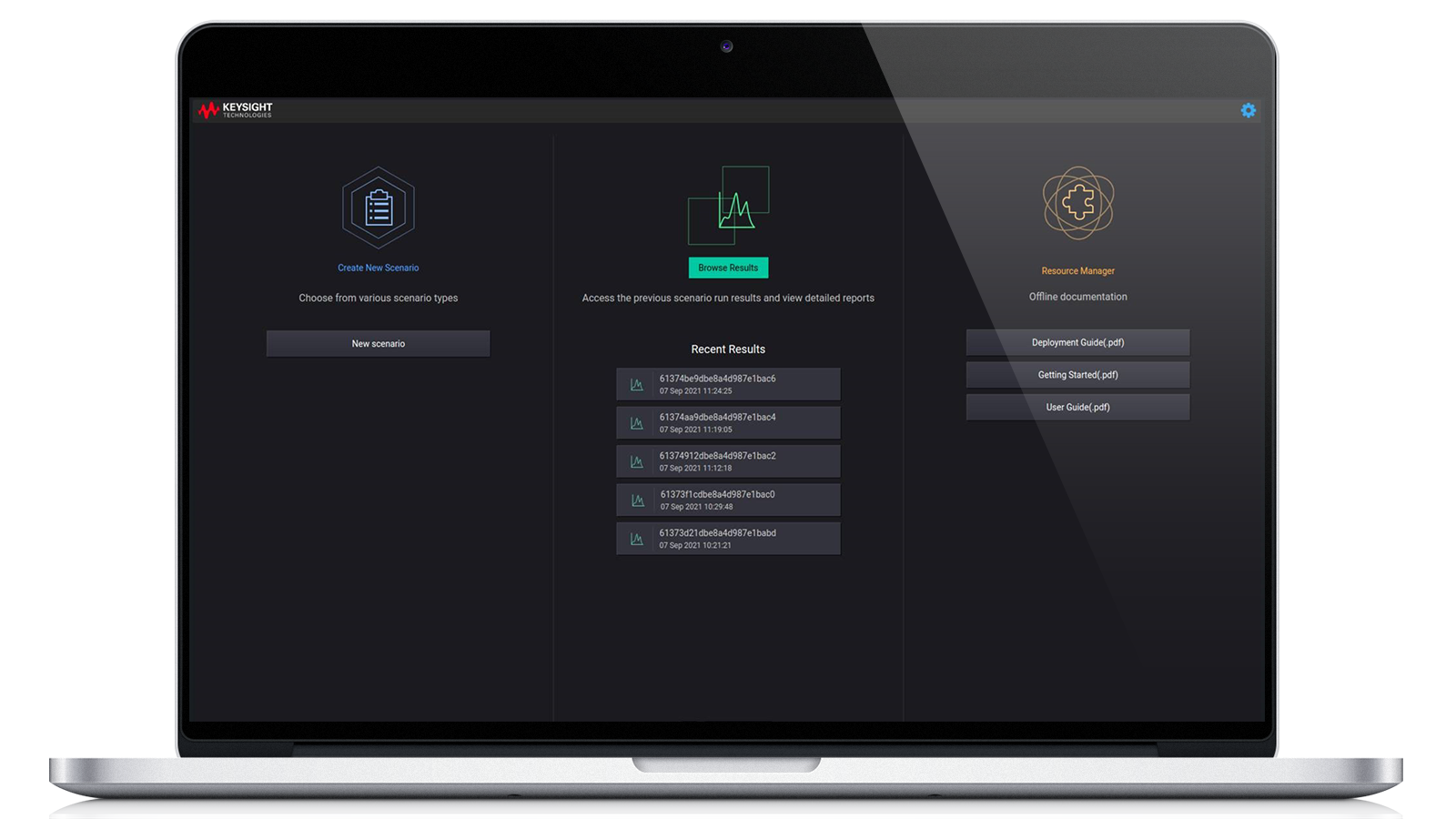
As soluções de teste de segurança IoT da Keysight combinam automação inteligente, análise em tempo real e cobertura de ameaças em evolução para validar a segurança dos dispositivos conectados em todas as fases do desenvolvimento. Concebidas para simular ciberataques reais, permitem testes de alta confiabilidade de sistemas incorporados, protocolos de comunicação e segurança de firmware para aplicações IoT industriais e de consumo. A plataforma automatiza a validação por meio de uma interface de usuário (UI) do tipo apontar e clicar ou API de automação. É uma ferramenta pronta para uso que ajuda a identificar lacunas de segurança de IoT relacionadas a requisitos de conformidade e rotulagem. Solicite hoje mesmo um orçamento para uma de nossas configurações populares. Precisa de ajuda para selecionar? Confira os recursos abaixo.
Comunicação segura
Testa a implementação de protocolos de criptografia, gerenciamento de certificados e mecanismos de autenticação. A verificação da comunicação segura garante a confidencialidade, integridade e autenticidade dos dados.
Simulação de ameaças
A emulação de ataques reais permite que os desenvolvedores avaliem como os dispositivos IoT respondem a vetores de ameaças, incluindo ataques de negação de serviço (DoS), spoofing e replay, fortalecendo a resiliência dos dispositivos.
Normas e conformidade
Os casos de teste automatizados estão em conformidade com as principais normas de segurança, incluindo ETSI EN 303 645, ANSI/CTA 2088-A e OWASP, garantindo a aprovação regulamentar e a confiança do cliente.
Análise do comportamento do dispositivo
Monitora as respostas, o desempenho e a estabilidade dos dispositivos sob condições de estresse e ataque, ajudando os engenheiros a identificar padrões anormais e fortalecer a robustez do sistema.

-
Bundles
Base Controller Software Subscription, IPv4 Attack, WLAN Attack, Bluetooth Attack, IPv6 Attack, Base Controller Software SubscriptionIPv6 AttackIPv4 AttackBluetooth AttackWLAN Attack
-
Type
Software
Configurações mais populares
Segurança da IoT, assinatura do software do controlador base
Licença para o módulo do sistema central através de uma interface de usuário web e API RESTful, oferecendo uma estrutura para automação, integração, arquitetura extensível e relatórios.
Licença para o módulo do sistema central através de uma interface de usuário web e API RESTful, oferecendo uma estrutura para automação, integração, arquitetura extensível e relatórios.
Segurança da IoT, assinatura do software do controlador base
983-1104
Licença para o módulo do sistema central através de uma interface de usuário web e API RESTful, oferecendo uma estrutura para automação, integração, arquitetura extensível e relatórios.
- Fuzzing de protocolo
- Avaliação de vulnerabilidade
- Testes de conformidade
- Estabelecimento de padrões comportamentais
A Avaliação de Segurança da IoT (IoT SA) da Keysight oferece um processo de verificação rápido e direto para dispositivos IoT, garantindo a conformidade com as normas e abordando vulnerabilidades comuns. Ela emprega um fuzzer de protocolo patenteado para fornecer uma avaliação abrangente. A IoT SA realiza testes em vários protocolos, incluindo TCP/IP, Bluetooth® Classic, Bluetooth® Low Energy (BLE), CAN e redes móveis O-RAN via IP. O software recebe atualizações mensais, incorporando novas auditorias e recursos para avaliar as vulnerabilidades atuais. A natureza modular das atualizações permite atualizações separadas para o sistema central e módulos adicionais.
Segurança IoT, módulo de ataque Bluetooth® com atualizações ATI
Licença complementar opcional para 983-1104 para ativar o módulo para avaliações de segurança Bluetooth®.
Licença complementar opcional para 983-1104 para ativar o módulo para avaliações de segurança Bluetooth®.
Segurança IoT, módulo de ataque Bluetooth® com atualizações ATI
983-1107
Licença complementar opcional para 983-1104 para ativar o módulo para avaliações de segurança Bluetooth®.
- Capacita ferramentas baseadas em WLAN para avaliação de segurança via Bluetooth®.
- Incorpora novas ferramentas desenvolvidas pela pesquisa de segurança ATI da Keysight em todas as atualizações baseadas em assinatura.
- Fornece ferramentas para fuzzing da pilha de rádio, descoberta de sistemas/serviços, gerenciamento de vulnerabilidades e avaliação contra pontos fracos conhecidos.
- Facilita a descoberta de novas fraquezas ou vulnerabilidades.
- Requer uma licença do Controlador de Segurança IoT Base (983-1104).
A Avaliação de Segurança da IoT (IoT SA) da Keysight oferece um processo de verificação rápido e direto para dispositivos IoT, garantindo a conformidade com as normas e abordando vulnerabilidades comuns. Ela emprega um fuzzer de protocolo patenteado para fornecer uma avaliação abrangente. O software recebe atualizações mensais, incorporando novas auditorias e recursos para avaliar as vulnerabilidades atuais. A natureza modular das atualizações permite atualizações separadas para o sistema central e módulos adicionais.
Pacote de segurança IoT com atualizações ATI
Pacote de avaliação de segurança IoT incluindo licença do controlador central: 983-1104, módulo IPv4: 983-1105, módulo WLAN: 983-1106 e módulo Bluetooth®: 983-1107.
Pacote de avaliação de segurança IoT incluindo licença do controlador central: 983-1104, módulo IPv4: 983-1105, módulo WLAN: 983-1106 e módulo Bluetooth®: 983-1107.
Pacote de segurança IoT com atualizações ATI
983-1110
Pacote de avaliação de segurança IoT incluindo licença do controlador central: 983-1104, módulo IPv4: 983-1105, módulo WLAN: 983-1106 e módulo Bluetooth®: 983-1107.
- Inclui Controlador de Base de Segurança IoT (983-1104)
- Inclui Módulo de Ataque IoT IPv4 (983-1105)
- Inclui módulo de ataque WLAN IoT (983-1106)
- Inclui módulo de ataque Bluetooth IoT (983-1107)
- Incorpora novas ferramentas desenvolvidas pela pesquisa de segurança ATI da Keysight em todas as atualizações baseadas em assinatura.
A Avaliação de Segurança da IoT (IoT SA) da Keysight oferece um processo de verificação rápido e direto para dispositivos IoT, garantindo a conformidade com as normas e abordando vulnerabilidades comuns. Ela emprega um fuzzer de protocolo patenteado para fornecer uma avaliação abrangente. O software recebe atualizações mensais, incorporando novas auditorias e recursos para avaliar as vulnerabilidades atuais. A natureza modular das atualizações permite atualizações separadas para o sistema central e módulos adicionais.
Serviços e suporte
Inove rapidamente com planos de suporte personalizados e tempos de resposta e resolução priorizados.
Obtenha assinaturas previsíveis baseadas em locação e soluções completas de gerenciamento do ciclo de vida para atingir suas metas de negócios mais rapidamente.
Experimente um serviço diferenciado como assinante do KeysightCare para obter respostas técnicas comprometidas e muito mais.
Garanta que seu sistema de teste funcione de acordo com as especificações e atenda às normas locais e globais.
Faça medições rapidamente com treinamento interno ministrado por instrutor e eLearning.
Faça o download do software Keysight ou atualize seu software para a versão mais recente.
Perguntas frequentes
Uma avaliação de segurança da IoT é uma avaliação em várias camadas da postura de segurança de um dispositivo conectado, abrangendo seu hardware, software, firmware e protocolos de comunicação. Normalmente, ela começa com a modelagem de ameaças para entender quais ativos precisam de proteção e quais alvos potenciais os invasores podem ter. A partir daí, a avaliação passa para testes práticos, começando pelas interfaces físicas do dispositivo, como portas UART, JTAG ou USB, que são verificadas quanto a acesso de depuração, vazamento de dados ou controle não autorizado. A análise do firmware é um componente importante, envolvendo a extração e a engenharia reversa da imagem binária para identificar segredos incorporados, configurações inseguras ou componentes vulneráveis.
A comunicação de rede é examinada minuciosamente para determinar se a criptografia está implementada corretamente e se os protocolos são suscetíveis a ataques de repetição, falsificação ou injeção. Se o dispositivo se comunica por meio de APIs em nuvem ou aplicativos móveis, esses componentes também são analisados em busca de problemas como autenticação deficiente, manuseio inseguro de tokens ou pontos de extremidade expostos. A avaliação geralmente inclui fuzzing de protocolo para testar a robustez das pilhas de comunicação, enviando pacotes malformados ou inesperados. Por fim, o dispositivo é comparado a estruturas de segurança conhecidas, como ETSI EN 303 645 ou NIST 8259, para identificar lacunas de conformidade. As ferramentas utilizadas durante esse processo podem incluir analisadores de código estático, depuradores, proxies de interceptação, sniffers de RF e kits de exploração de hardware.
Os testes em nível de protocolo são essenciais para dispositivos IoT, pois eles frequentemente utilizam protocolos de comunicação leves ou proprietários que são mais vulneráveis a falhas de segurança do que padrões maduros, como HTTPS. Ao contrário da infraestrutura geral de TI, onde os protocolos foram reforçados ao longo de décadas, os ecossistemas IoT dependem de pilhas como CoAP, MQTT, Zigbee, BLE ou protocolos seriais personalizados que muitas vezes são mal documentados ou implementados de forma inconsistente. Como resultado, muitos dispositivos processam dados malformados ou inesperados de maneiras inseguras, levando a falhas, estouros de buffer ou comportamentos indesejados. Os testes em nível de protocolo envolvem tanto o monitoramento passivo quanto a injeção ativa de pacotes malformados, fora de sequência ou maliciosos para observar como o dispositivo reage.
Isso é especialmente importante em ambientes onde os dispositivos tomam decisões autônomas com base em comandos de rede — por exemplo, fechaduras inteligentes, sensores ou equipamentos médicos. Sem uma verificação de limites ou autenticação adequada, esses dispositivos podem aceitar comandos falsificados ou se tornar instáveis. Além disso, muitas pilhas de IoT pressupõem ambientes confiáveis e não aplicam padrões criptográficos rigorosos, deixando-as vulneráveis a sequestros de sessão ou ataques de repetição. Ao realizar testes de fuzzing e interação com reconhecimento de protocolo, os engenheiros podem descobrir essas vulnerabilidades sutis, mas críticas, que as revisões de código estáticas ou os testes de penetração gerais muitas vezes não detectam.
Os testes de segurança da IoT devem ser um processo contínuo integrado em todas as fases do ciclo de vida do dispositivo, e não apenas uma validação única antes do lançamento do produto. Na fase de projeto, é fundamental realizar a modelagem de ameaças e estabelecer requisitos de segurança desde o início, quando as decisões arquitetônicas têm maior influência na segurança a longo prazo. Durante o desenvolvimento, os esforços de teste devem se concentrar na identificação de vulnerabilidades no nível do código, na verificação da segurança de bibliotecas de terceiros e na realização de análises estáticas e dinâmicas em estágio inicial. Antes do lançamento, uma avaliação abrangente — incluindo validação de firmware, análise de protocolo de comunicação, teste de interface de hardware e avaliação de segurança de back-end — é essencial para garantir que o dispositivo esteja protegido contra ameaças conhecidas.
No entanto, os testes de segurança devem continuar após o dispositivo entrar no mercado. As avaliações pós-implantação são essenciais, especialmente quando são lançadas atualizações de firmware, novos recursos são integrados ou vulnerabilidades recém-descobertas afetam a pilha de software ou serviços externos. Dada a longa vida útil e os ambientes de implantação frequentemente sem supervisão dos dispositivos IoT, eles estão perpetuamente expostos a ameaças cibernéticas em constante evolução. Reavaliações periódicas — idealmente realizadas anualmente ou após qualquer mudança significativa — ajudam a manter a conformidade com os padrões de segurança do setor e protegem o dispositivo contra riscos emergentes. O fortalecimento da segurança por meio de monitoramento contínuo, automação de testes remotos e estruturas de atualização seguras over-the-air (OTA) garante resiliência de longo prazo em todo o ciclo de vida do dispositivo.