Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
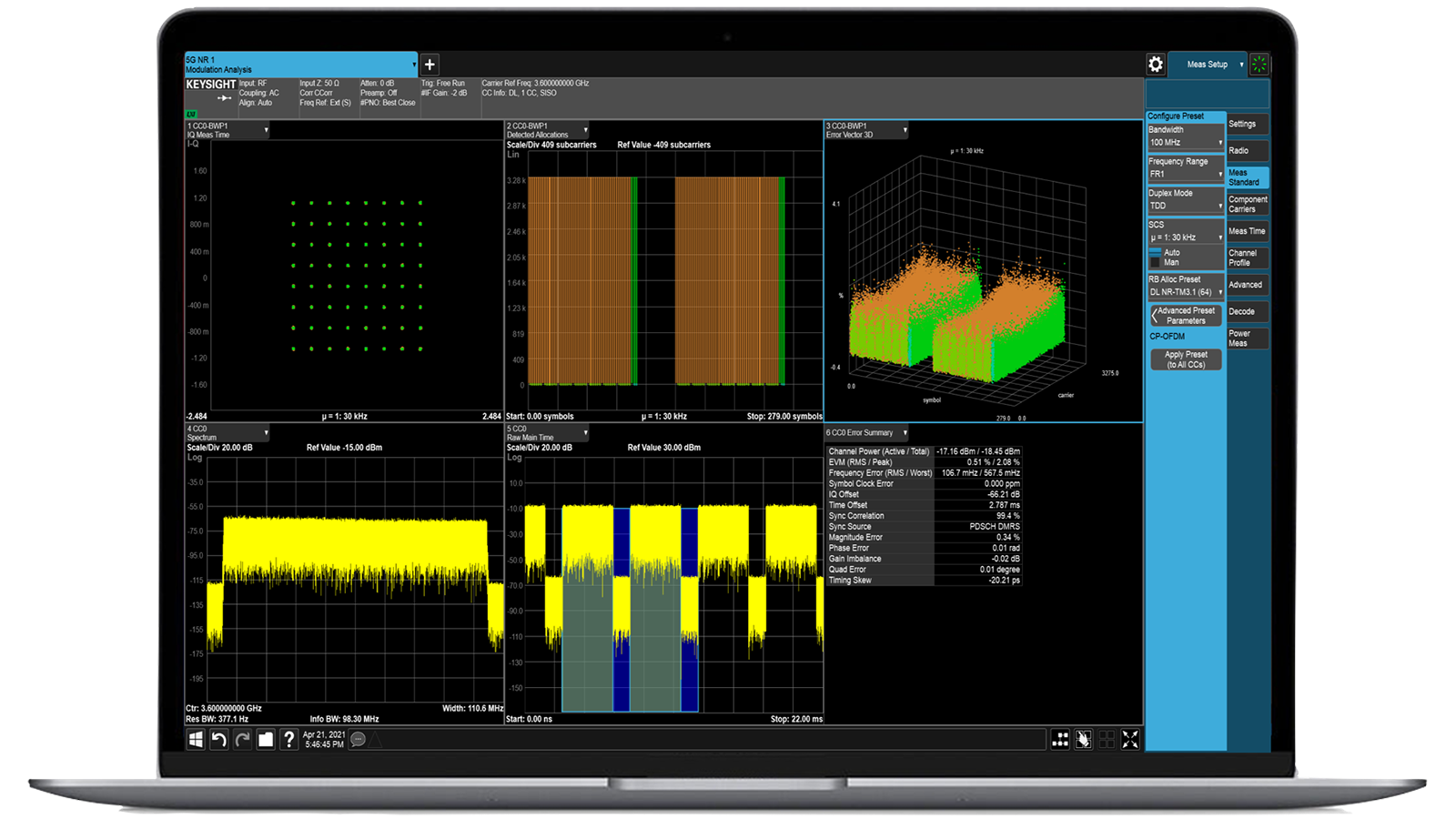
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
IoT Security Testing Real-world IoT threat simulation for enhanced security validation
- Overview
- All Models
- Accessories
- Software
- Support
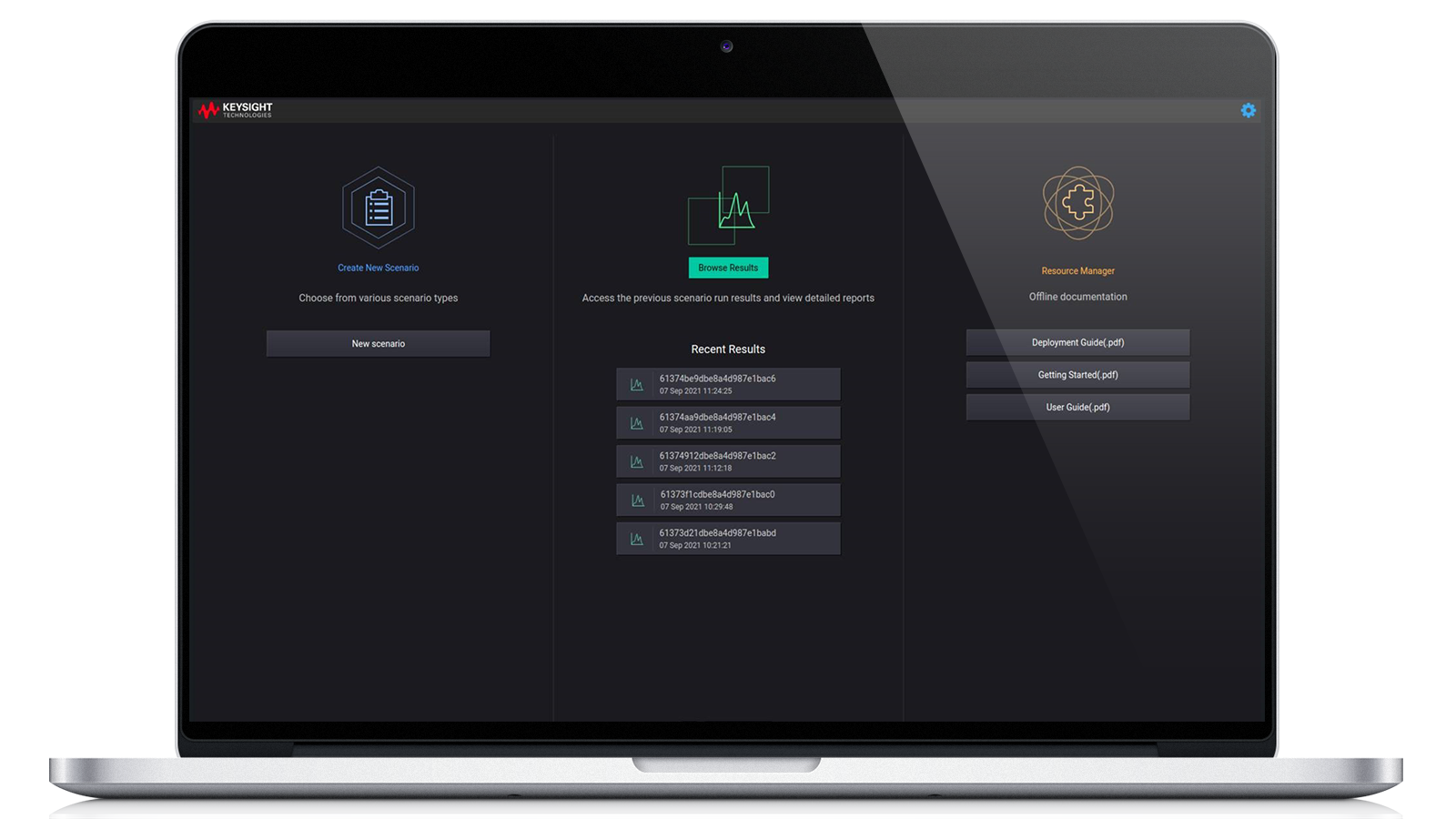
Robust security validation solutions for connected devices
Keysight IoT security testing solutions combine intelligent automation, real-time analysis, and evolving threat coverage to validate connected device security at every stage of development. Built to simulate real-world cyberattacks, they enable high-confidence testing of embedded systems, communication protocols, and firmware security for consumer and industrial IoT applications. The platform automates validation through a point-and-click user interface (UI) or automation API. It’s a turnkey tool that helps identify IoT security gaps related to compliance and labeling requirements. Request a quote for one of our popular configurations today. Need help selecting? Check out the resources below.
Secure communication
Tests the implementation of encryption protocols, certificate handling, and authentication mechanisms. Verifying secure communication ensures data confidentiality, integrity, and authenticity.
Threat simulation
Real-world attack emulation allows developers to assess how IoT devices respond to threat vectors, including denial-of-service (DoS), spoofing, and replay attacks, strengthening device resilience.
Standards and compliance
Automated test cases align with key security standards, including ETSI EN 303 645, ANSI / CTA 2088-A, and OWASP, ensuring regulatory approval and customer trust.
Device behavior analysis
Monitors device responses, performance, and stability under stress and attack conditions, helping engineers identify abnormal patterns and harden system robustness.

-
Bundles
Base Controller Software Subscription, IPv4 Attack, WLAN Attack, Bluetooth Attack, IPv6 Attack, Base Controller Software SubscriptionIPv6 AttackIPv4 AttackBluetooth AttackWLAN Attack
-
Type
Software
Most popular configurations
IoT Security, Base Controller Software Subscription
License for the core system module through a web user interface and RESTful API, offering a framework for automation, integration, extensible architecture, and reporting.
License for the core system module through a web user interface and RESTful API, offering a framework for automation, integration, extensible architecture, and reporting.
IoT Security, Base Controller Software Subscription
983-1104
License for the core system module through a web user interface and RESTful API, offering a framework for automation, integration, extensible architecture, and reporting.
- Protocol Fuzzing
- Vulnerability assessment
- Compliance testing
- Behavioral baselining
Keysight's IoT Security Assessment (IoT SA) offers a swift and straightforward verification process for IoT devices, ensuring compliance with standards and addressing common vulnerabilities. It employs a patented protocol fuzzer to provide a comprehensive assessment. IoT SA conducts tests across various protocols, including TCP/IP, Bluetooth® Classic, Bluetooth® Low Energy (BLE), CAN, and O-RAN mobile networks via IP. The software receives monthly updates, incorporating new audits and features to assess current vulnerabilities. The modular nature of updates allows for separate updates to the core system and additional modules.
IoT Security, Bluetooth® Attack Module with ATI Updates
Optional add-on license for 983-1104 to activate the module for Bluetooth® security assessments.
Optional add-on license for 983-1104 to activate the module for Bluetooth® security assessments.
IoT Security, Bluetooth® Attack Module with ATI Updates
983-1107
Optional add-on license for 983-1104 to activate the module for Bluetooth® security assessments.
- Empowers WLAN-Based Tools for Security Assessment over Bluetooth®.
- Incorporates new tools developed through Keysight’s ATI security research throughout the subscription-based updates.
- Provides tools for fuzzing the radio stack, system/service discovery, vulnerability management, and assessment against known weaknesses.
- Facilitates the discovery of new weaknesses or vulnerabilities.
- Requires an IoT Security Base Controller License (983-1104).
Keysight's IoT Security Assessment (IoT SA) offers a swift and straightforward verification process for IoT devices, ensuring compliance with standards and addressing common vulnerabilities. It employs a patented protocol fuzzer to provide a comprehensive assessment. The software receives monthly updates, incorporating new audits and features to assess current vulnerabilities. The modular nature of updates allows for separate updates to the core system and additional modules.
IoT Security Bundle with ATI Updates
IoT Security Assessment bundle including core controller license: 983-1104, IPv4 module: 983-1105, WLAN module: 983-1106, and Bluetooth® module: 983-1107.
IoT Security Assessment bundle including core controller license: 983-1104, IPv4 module: 983-1105, WLAN module: 983-1106, and Bluetooth® module: 983-1107.
IoT Security Bundle with ATI Updates
983-1110
IoT Security Assessment bundle including core controller license: 983-1104, IPv4 module: 983-1105, WLAN module: 983-1106, and Bluetooth® module: 983-1107.
- Includes IoT Security Base Controller (983-1104)
- Includes IoT IPv4 Attack Module (983-1105)
- Includes IoT WLAN Attack Module (983-1106)
- Includes IoT Bluetooth Attack Module (983-1107)
- Incorporates new tools developed through Keysight’s ATI security research throughout the subscription-based updates.
Keysight's IoT Security Assessment (IoT SA) offers a swift and straightforward verification process for IoT devices, ensuring compliance with standards and addressing common vulnerabilities. It employs a patented protocol fuzzer to provide a comprehensive assessment. The software receives monthly updates, incorporating new audits and features to assess current vulnerabilities. The modular nature of updates allows for separate updates to the core system and additional modules.
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
An IoT security assessment is a multi-layered evaluation of the security posture of a connected device, covering its hardware, software, firmware, and communication protocols. It typically begins with threat modeling to understand what assets need protection and what potential attackers might target. From there, the assessment moves into hands-on testing, starting with the device’s physical interfaces such as UART, JTAG, or USB ports, which are checked for debug access, data leakage, or unauthorized control. Firmware analysis is a major component, involving the extraction and reverse engineering of the binary image to identify embedded secrets, insecure configurations, or vulnerable components.
Network communication is closely examined to determine if encryption is implemented correctly and whether protocols are susceptible to replay, spoofing, or injection attacks. If the device communicates through cloud APIs or mobile apps, those components are also analyzed for issues such as poor authentication, insecure token handling, or exposed endpoints. The assessment often includes protocol fuzzing to test the robustness of communication stacks by sending malformed or unexpected packets. Finally, the device is compared against known security frameworks such as ETSI EN 303 645 or NIST 8259 to identify compliance gaps. Tools used during this process may include static code analyzers, debuggers, intercept proxies, RF sniffers, and hardware exploit kits.
Protocol-level testing is critical for IoT devices because they frequently use lightweight or proprietary communication protocols that are more vulnerable to security flaws than mature standards like HTTPS. Unlike general IT infrastructure, where protocols have been hardened over decades, IoT ecosystems rely on stacks such as CoAP, MQTT, Zigbee, BLE, or custom serial protocols that are often poorly documented or inconsistently implemented. As a result, many devices process malformed or unexpected data in unsafe ways, leading to crashes, buffer overflows, or unintended behavior. Protocol-level testing involves both passive monitoring and active injection of malformed, out-of-sequence, or malicious packets to observe how the device reacts.
This is especially important in environments where devices make autonomous decisions based on network commands—for example, smart locks, sensors, or medical equipment. Without proper bounds checking or authentication, such devices may accept spoofed commands or become unstable. Furthermore, many IoT stacks assume trusted environments and do not enforce rigorous cryptographic standards, leaving them open to session hijacking or replay attacks. By performing protocol-aware fuzzing and interaction testing, engineers can uncover these subtle but critical vulnerabilities that static code reviews or general penetration tests often miss.
IoT security testing should be an ongoing process integrated into every phase of the device lifecycle, not just a one-time validation before product launch. In the design phase, it is crucial to conduct threat modeling and establish security requirements early, when architectural decisions have the greatest influence on long-term security. During development, testing efforts should focus on identifying code-level vulnerabilities, verifying the security of third-party libraries, and performing early-stage static and dynamic analyses. Prior to release, a comprehensive assessment—including firmware validation, communication protocol analysis, hardware interface testing, and backend security evaluation—is essential to ensure the device is hardened against known threats.
However, security testing must continue after the device enters the market. Post-deployment assessments are critical, especially when firmware updates are issued, new features are integrated, or newly discovered vulnerabilities affect the software stack or external services. Given the long operational life and often unattended deployment environments of IoT devices, they are perpetually exposed to evolving cyber threats. Periodic reassessments—ideally conducted annually or following any significant change—help maintain compliance with industry security standards and protect the device from emerging risks. Strengthening security through continuous monitoring, remote test automation, and secure over-the-air (OTA) update frameworks ensures long-term resilience across the entire device lifecycle.