What are you looking for?
Accelerate Grid Modernization
Streamline grid and energy transformation and modernization. Plan, validate, and monitor complex utility networks. Develop, certify, and integrate new distributed energy resources (DER) and smart inverter technology. Test performance of battery storage, solar power, and network security systems.
Find Your Grid and Energy Test Solution
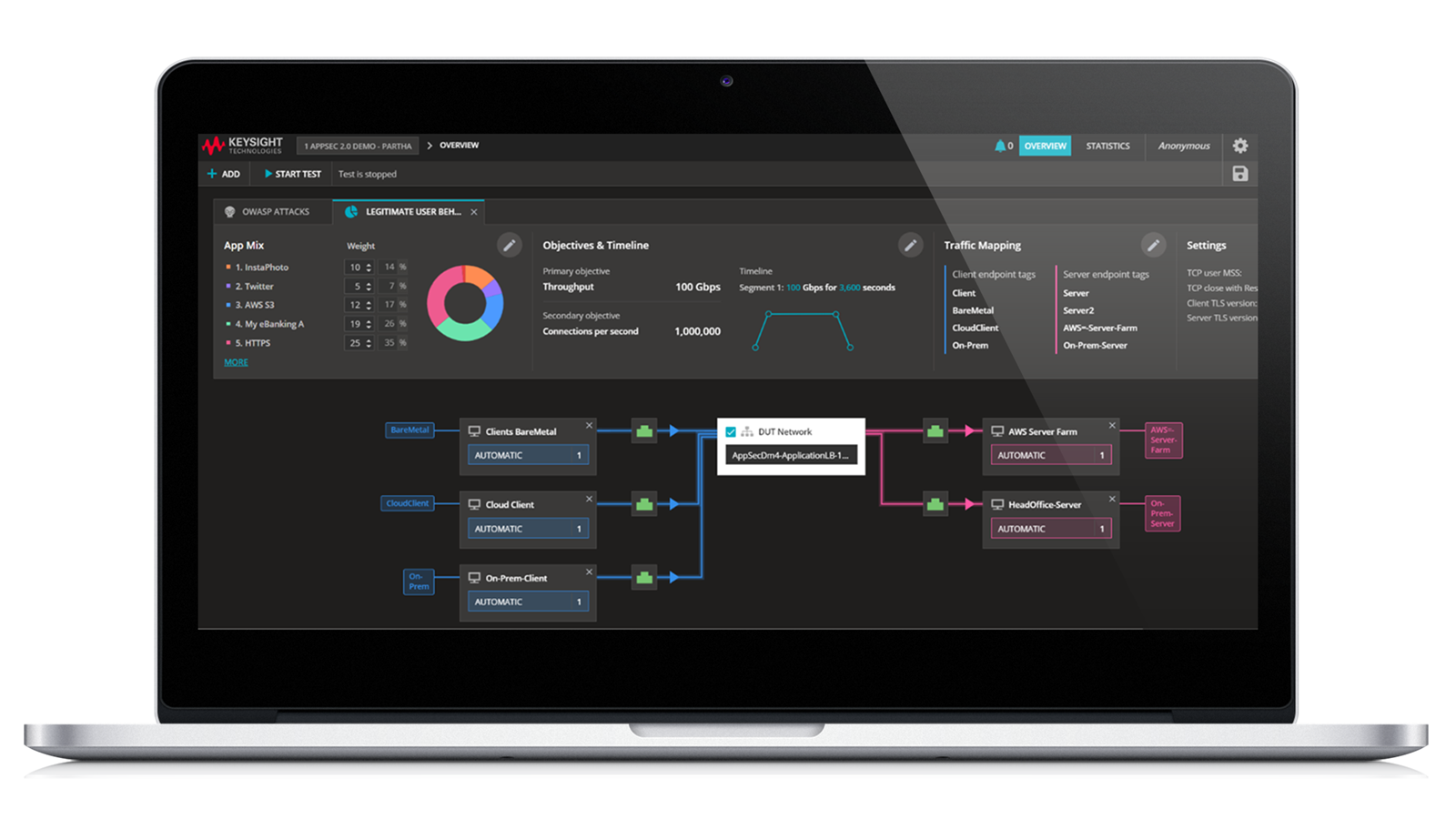
Grid Cybersecurity: Accelerate CIP-015-1 with Strong Network Visibility
The increasingly interconnected electric grid risks cybersecurity attacks from bad actors who can infiltrate firewalls. Once inside, they move quietly, blending into normal network traffic and often going undetected until it’s too late. The NERC standard CIP-015-1: Internal Network Security Monitoring aims to help utility companies modernize their grid cybersecurity. Instead of relying solely on keeping adversaries out, this standard requires companies to see and continuously monitor what’s happening inside their networks. Learn how Keysight Network Visibility solutions play a critical role in supporting electric utility companies as they work toward achieving their CIP-015-1 compliance objectives.
Key Drivers of Grid Modernization
Grid modernization is a fundamental shift incorporating technologies like telecommunications, distributed energy resources (DER), battery storage, solar power, and cybersecurity that will reshape how the world generates, distributes, and consumes electricity. This transformation strives to tackle concerns about aging infrastructure, increasing blackouts, and increasing environmental impacts to ensure a more sustainable, reliable, and secure energy system moving forward.
Visualize Grid Modernization
The energy grid is more complex than ever before. Grid modernization is connecting the energy, communications, and operations areas into a singular ecosystem. While grid modernization presents a complex challenge, the potential benefits are significant. Simplify this new shift in how the grid functions.
Find the Solution to Your Use Case
Learn how to do the following:
- Measure battery cell discharge.
- Analyze current drain using battery profiling and emulation.
- Predict battery performance.
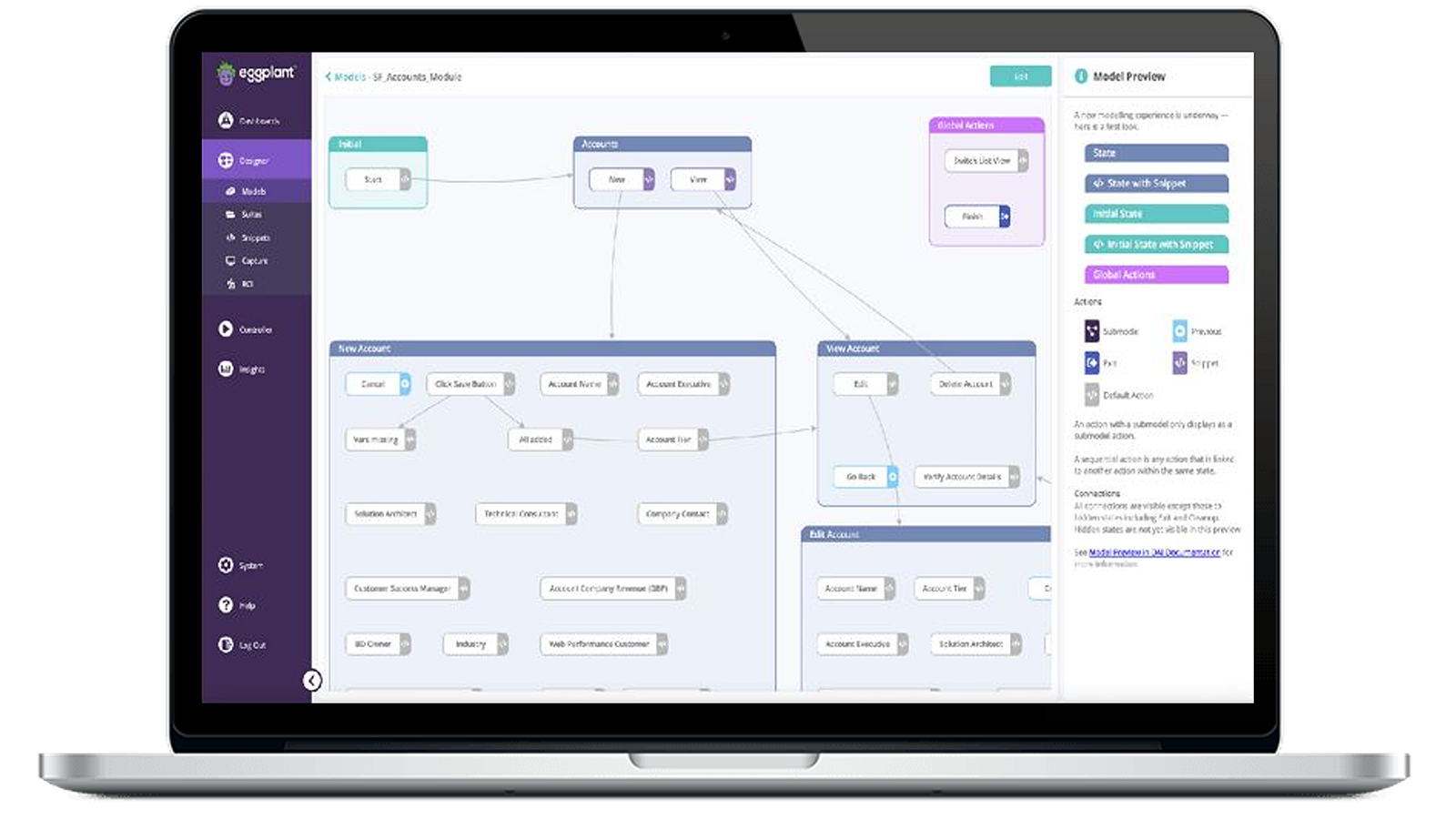
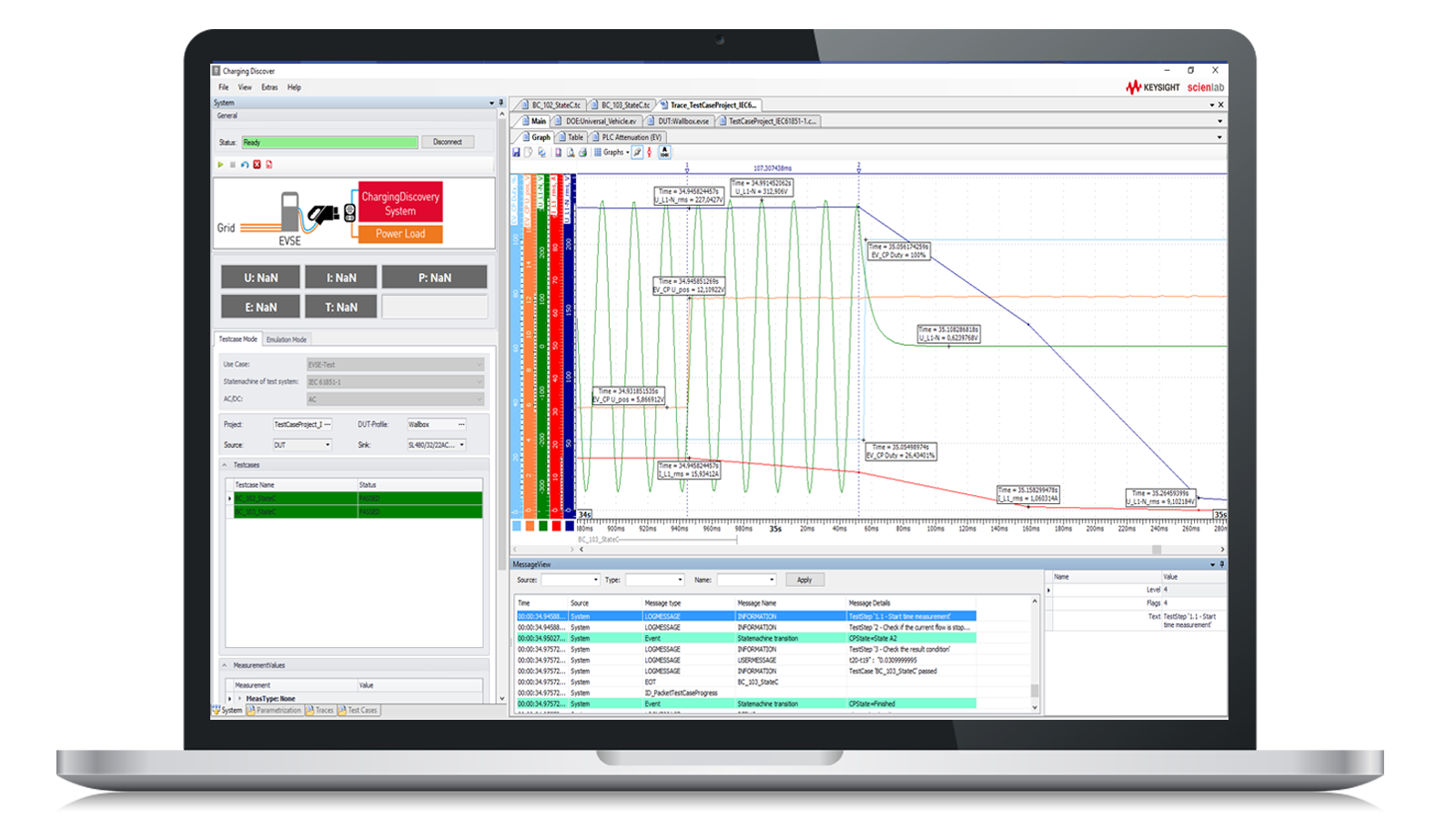
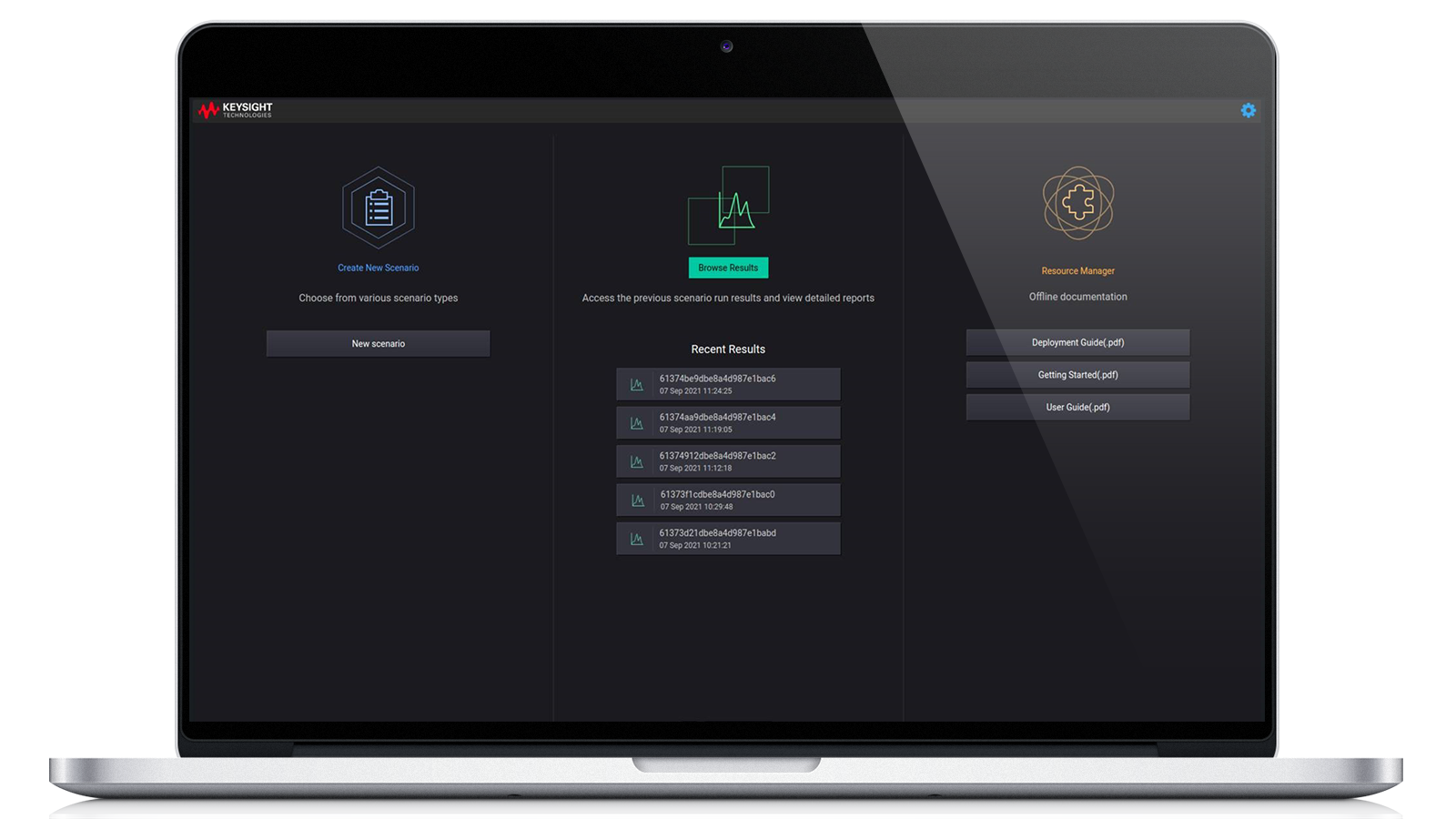
Accelerate Development with Keysight Software
Access More Insights & Resources
Want help or have questions?