- PXI
- AXI
- 메인프레임
- 모듈
- 시스템
- XGS
PXIe 정밀 IV 테스트 시스템
정밀 측정을 빠르게 시작하십시오.
컴팩트하고 고밀도 모듈에 빠른 데이터 처리 속도를 갖춘 벤치탑급 성능 제공

AXIe 모듈형 시스템
섀시 및 측정 모듈을 포함한 AXIe 모듈형 시스템
확장 가능한 데이터 수집 시스템을 위한 고채널 밀도 및 높은 처리량.

메인프레임 개요
메인프레임
안정적인 통합. 안정적인 스위칭. 안정적인 측정.

모듈 개요
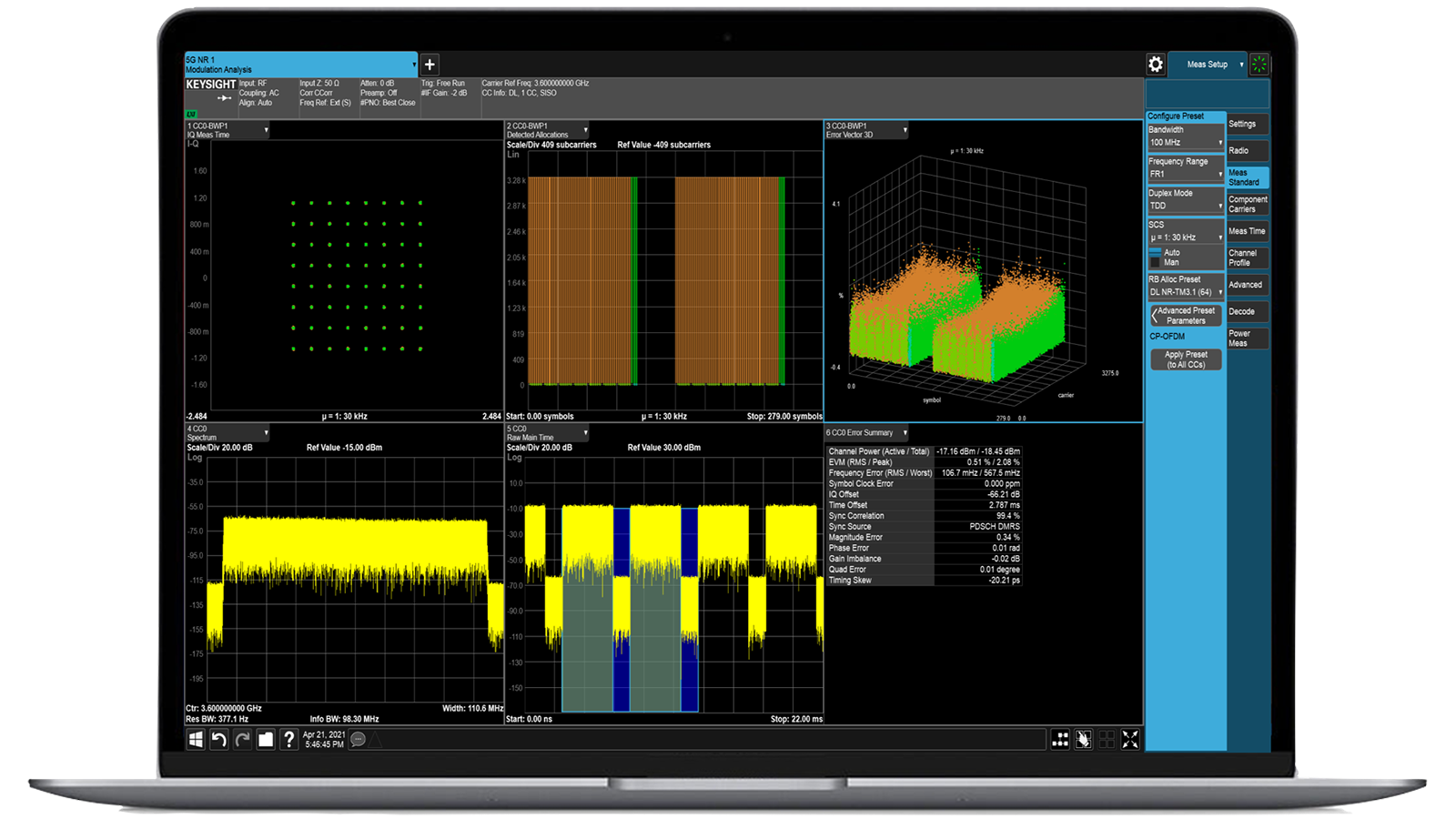
키사이트 모듈형 시스템: 탁월한 성능. 통찰력 확보 시간 절반 단축.
키사이트의 모듈형 시스템은 탁월한 PXI 및 AXIe 성능을 제공하여 가장 까다로운 RF, 마이크로웨이브 및 디지털 과제를 해결하는 데 도움을 줍니다.

모듈형 시스템
카드, 섀시 및 측정 모듈을 포함한 모듈형 시스템
PXI/AXI 카드, 섀시, 메인프레임 등 다양한 모듈형 구성 요소의 조합

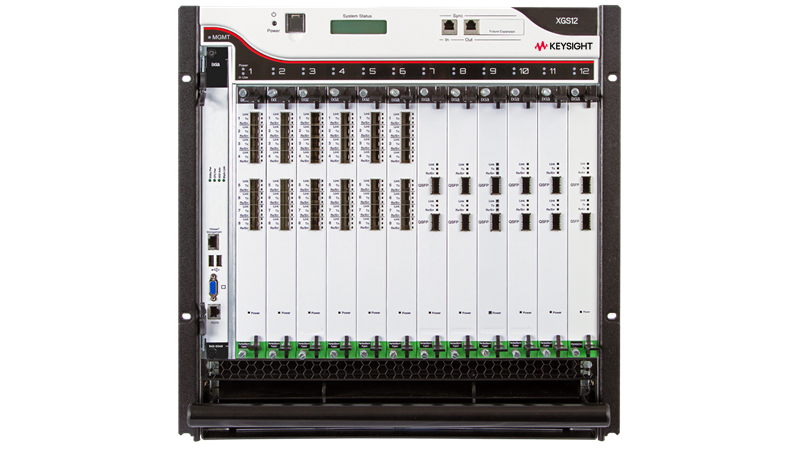
XGS 모듈형 네트워크
모듈형 네트워크 및 보안 테스트 시스템
효율적인 전력 및 냉각 기능을 갖춘 키사이트 네트워크 및 보안 테스트 로드 모듈용 고밀도 포트 섀시.
21개 중 12개 표시
필터 및 정렬
-
21
사용 가능한 필터 없음
-
4
-
7
-
10
사용 가능한 필터 없음
-
6
-
16
-
7
-
5
-
7
-
4
사용 가능한 필터 없음
-
13
-
2
-
6
사용 가능한 필터 없음
-
21
사용 가능한 필터 없음
-
1
-
1
사용 가능한 필터 없음
-
1
사용 가능한 필터 없음
-
1
-
1
-
1
-
1
-
1
-
1
-
1
사용 가능한 필터 없음
사용 가능한 필터 없음
사용 가능한 필터 없음
사용 가능한 필터 없음

PerfectStorm 10GE 8포트 퓨전 (PS10GE8NG)
모델
944-1200
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
8

PerfectStorm 40GE 2포트 로드 모듈
모델
944-1201
폼 팩터
로드 모듈
인터페이스
QSFP28
인터페이스 속도 모드
40GE, 10GE
License types
-
모델
-
포트
2

PerfectStorm 1GE 8포트 퓨전 (PS1GE8NG)
모델
944-1203
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
1GE
License types
-
모델
-
포트
8

PerfectStorm 10GE 8포트 (PS10GE8)
모델
944-1204
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
8

PerfectStorm 40GE 2포트 로드 모듈
모델
944-1205
폼 팩터
로드 모듈
인터페이스
QSFP28
인터페이스 속도 모드
40GE, 10GE
License types
-
모델
-
포트
2

PerfectStorm 10GE 4포트 (PS10GE4)
모델
944-1207
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
4

PerfectStorm 10GE 2포트 (PS10GE2)
모델
944-1208
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
2

PerfectStorm 10GE 4포트 퓨전(PS10GE4NG)
모델
944-1209
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
4

PerfectStorm 10GE 2포트 퓨전(PS10GE2NG)
모델
944-1210
폼 팩터
로드 모듈
인터페이스
SFP+
인터페이스 속도 모드
10GE, 1GE
License types
-
모델
-
포트
2

CloudStorm 100GE 2포트 퓨전 로드 모듈
모델
944-1231
폼 팩터
로드 모듈
인터페이스
QSFP28
인터페이스 속도 모드
100GE
License types
-
모델
-
포트
2

CloudStorm 2포트 로드 모듈
모델
944-1232
폼 팩터
로드 모듈
인터페이스
QSFP28
인터페이스 속도 모드
100GE
License types
-
모델
-
포트
2

CloudStorm-XP 100GE 2포트, 모든 속도 지원 로드 모듈
모델
944-1252
폼 팩터
로드 모듈
인터페이스
QSFP28
인터페이스 속도 모드
100GE, 50GE, 40GE, 25GE, 10GE
License types
-
모델
-
포트
2