What are you looking for?
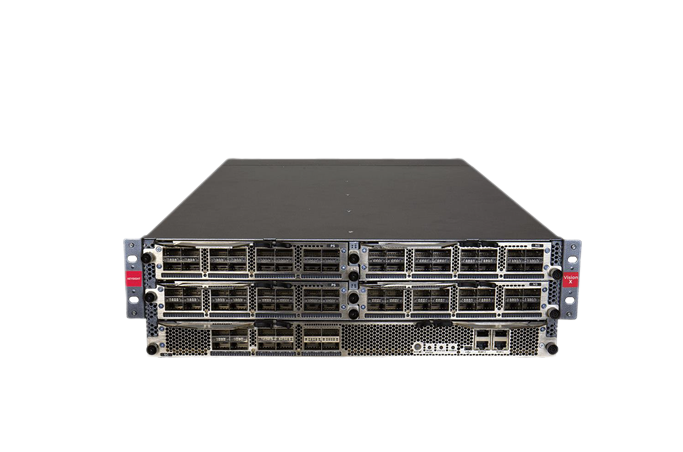
Network Packet Brokers
Twice the performance. No dropped packets.

2024 Frost & Sullivan New Product Innovation Award Winner

The Vision 400 Series Network Packet Brokers received the prestigious 2024 Global New Product Innovation Award from Frost & Sullivan. This innovative product line delivers unmatched performance, modularity, scalability, future-proof design, automation, intelligence, and an exceptional end-user experience.
Highlights
- Dedicated hardware acceleration provides a Zero packet loss architecture.
- Filtering of traffic so that each monitoring or inline security tool receives exactly the right data.
- SSL decryption to quickly detect emerging threats encrypting exploits within application traffic.
- Dynamic filter compiler handles all filter rule complexities automatically — no overlapping filter rule headaches.
- Aggregation of traffic from multiple TAPs or SPAN ports.
- Load-balancing of traffic to multiple analysis tools.
- L7 application awareness efficiently allows for packet processing based on unique applications.
Select the Network Packet Broker That's Right for You
Most Deployed Network Packet Brokers
Network Packet Broker Features
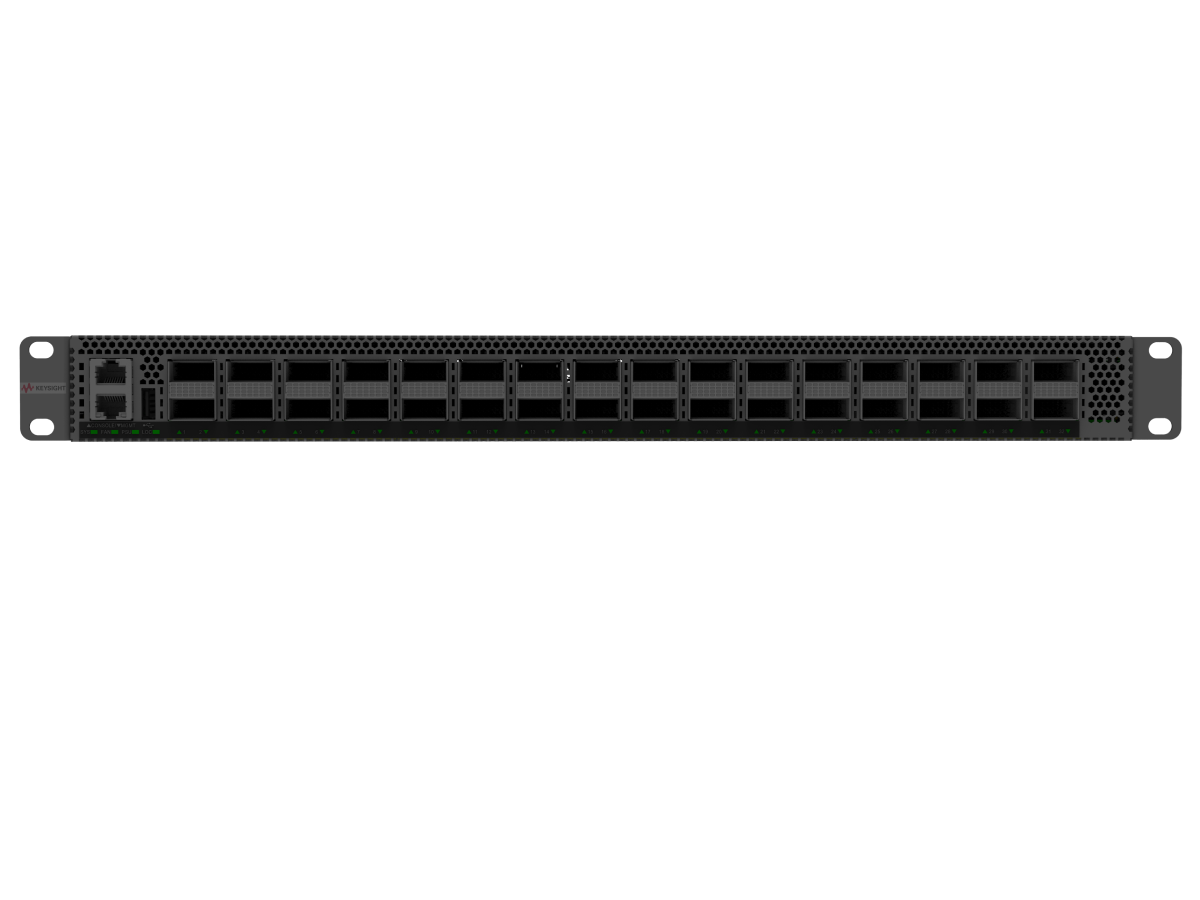
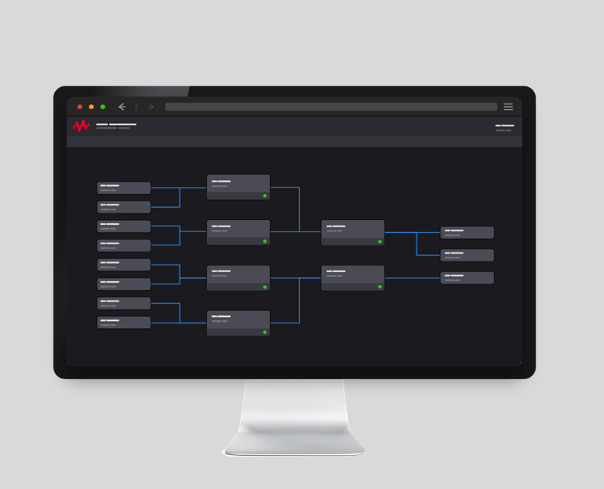
Ease of Use Matters
With Keysight's intuitive drag-and-drop GUI, it has never been easier to get the right traffic to the right tools. Quickly and easily connect taps and SPANs, apply filters, deduplicate, decrypt and forward traffic to the right tools. Our patented dynamic filter compiler makes quick work of the complexity of overlapping filters.
Other solutions often require complex and hard-to-manage REGEX and other command-line exercises. While powerful, command line expressions can be intricate and hard to confirm, greatly increasing the risk of human error and misconfiguration. The Keysight GUI helps speed operations and eliminate errors.
Packet Loss Matters
You deploy network packet brokers to provide visibility into network traffic, not create blind spots. If your packet broker drops packets, you are creating blind spots that can interfere with network analytics, or, even worse, impact security.
Keysight network packet brokers are built with a system architecture that enables line-rate performance with no dropped traffic or packet loss. This means that your visibility infrastructure can deliver the 100% visibility that you need. Remember, partial visibility isn't good enough.
Performance Matters
Hardware Accelerated Performance Matters
"Do what you can in hardware. Do what you must in software." The old adage about system design remains true today. While we are in the era of software-defined networks and software-defined everything else, in the end when performance matters you build the right system with the right hardware.
Like some of the most advanced high-performance cloud and network infrastructure, Keysight network packet brokers use FPGA-based hardware acceleration to ensure line-rate performance and no dropped packets, even with features and filters turned on — an area where the competition struggles.
Feature Compatibility Matters
When you select a network visibility solution, you might not pay much attention to feature compatibility — after all, it is only reasonable to expect that the features you read about on the datasheet can be used together on a single system.
With Keysight, they can. Our unique hardware architecture ensures that multiple features can run on the same packet broker at the same time. Other packet brokers on the market require you to buy and manage more modules and daisy chain everything together — a solution that quickly becomes costly and unscalable.

Customize your Network Packet Broker Deployment
Featured Resources
Want help or have questions?