What are you looking for?
Prepare for CMMC with Confidence
Secure Your Eligibility for DoD Contracts
The Cybersecurity Maturity Model Certification (CMMC) is the Department of Defense’s (DoD) framework for ensuring that Defense Industrial Base (DIB) contractors safeguard sensitive information critical to national security. Designed to strengthen cyber resilience and enforce accountability, CMMC certification is not optional. Without it, contractors will be ineligible for DoD contracts, making compliance essential to staying in the game. Keysight supports this effort by providing advanced testing, visibility, training, and automation solutions that help organizations achieve CMMC compliance. Join us on this journey as we work together to build stronger, more credible cybersecurity readiness across the DIB.
The Power of Proof: Turning CMMC Compliance into Competitive Credibility
Keysight commissioned primary research after recognizing a critical gap in how organizations approach CMMC readiness. While compliance requirements continue to evolve, many companies across the DIB still lack clear, evidence-based strategies to demonstrate and sustain compliance.
The Power of Proof explores these challenges through insights from cybersecurity, IT, and compliance leaders, uncovering where progress stalls and why. More importantly, it highlights the growing need to shift from checkbox compliance to credible, proof-driven readiness, turning CMMC from a regulatory burden into a competitive advantage.
Discover What It Takes to Meet CMMC Requirements at Every Level
Navigate your CMMC journey with confidence
This white paper demystifies the evolving CMMC framework, breaking down requirements for Levels 1, 2, and 3, and providing practical solutions to help you prepare with confidence.
Build Your CMMC Roadmap: Levels 1–3

Level 1 Checklist
Get a simple, easy-to-follow checklist of the 15 essential safeguarding practices outlined in the FAR Clause 52.204-21 for Level 1 compliance — ideal for handling Federal Contract Information (FCI) on unclassified systems.

Level 2 Checklist
Use this streamlined checklist to navigate the enhanced security requirements for achieving Level 2 compliance, including the 110+ controls aligned with NIST SP 800-171 to protect Controlled Unclassified Information (CUI).

Level 3 Checklist
Access a clear, organized list of advanced cybersecurity practices that builds on Level 2 compliance with 24 additional enhanced practices based on NIST SP 800-172, focusing on advanced threat protection and proactive cybersecurity.
Explore Cybersecurity Test Solutions to Accelerate Your Defenses
Dive Deeper into Proven Approaches to Prepare for Compliance
Find the Solutions You Need to Meet CMMC Requirements at Every Level
Domain |
Practice no. |
Requirement name |
Product |
|---|---|---|---|
| System and communications protection | SC.L1-b.1.x |
Boundary protection (FCI) |
Network packet brokers |
| System and information integrity | SI.L1-b.1.xii |
Flaw remediation (FCI) |
|
| System and information integrity | SI.L2-3.14.1 | Flaw remediation (CUI) | Threat Simulator |
Prove your network is secure with Keysight Threat Simulator
Domain |
Practice no. |
Requirement name |
Product |
|---|---|---|---|
| System and communications protection | SC.L2-3.13.1 |
Boundary protection (CUI) |
Network packet brokers |
| System and information integrity | SI.L2-3.14.6 |
Monitoring communications for attack |
|
| Security assessment | CA.L2-3.12.3 | Security control monitoring | Threat Simulator and Network packet brokers |
| Security assessment | CA.L2-3.12.1 | Security control assessment |
Threat Simulator and Cyperf |
| Risk assessment | RA.L3-3.11.1 | Vulnerability scan | IoT Security Assessment |
| Incident response | IR.L2-3.6.3 | Incident response testing | Threat Simulator and Cyber Range |
| Incident response | IR.L2-3.6.1 | Incident handling | Threat Simulator, Cyber Range, and our Flyaway Kit |
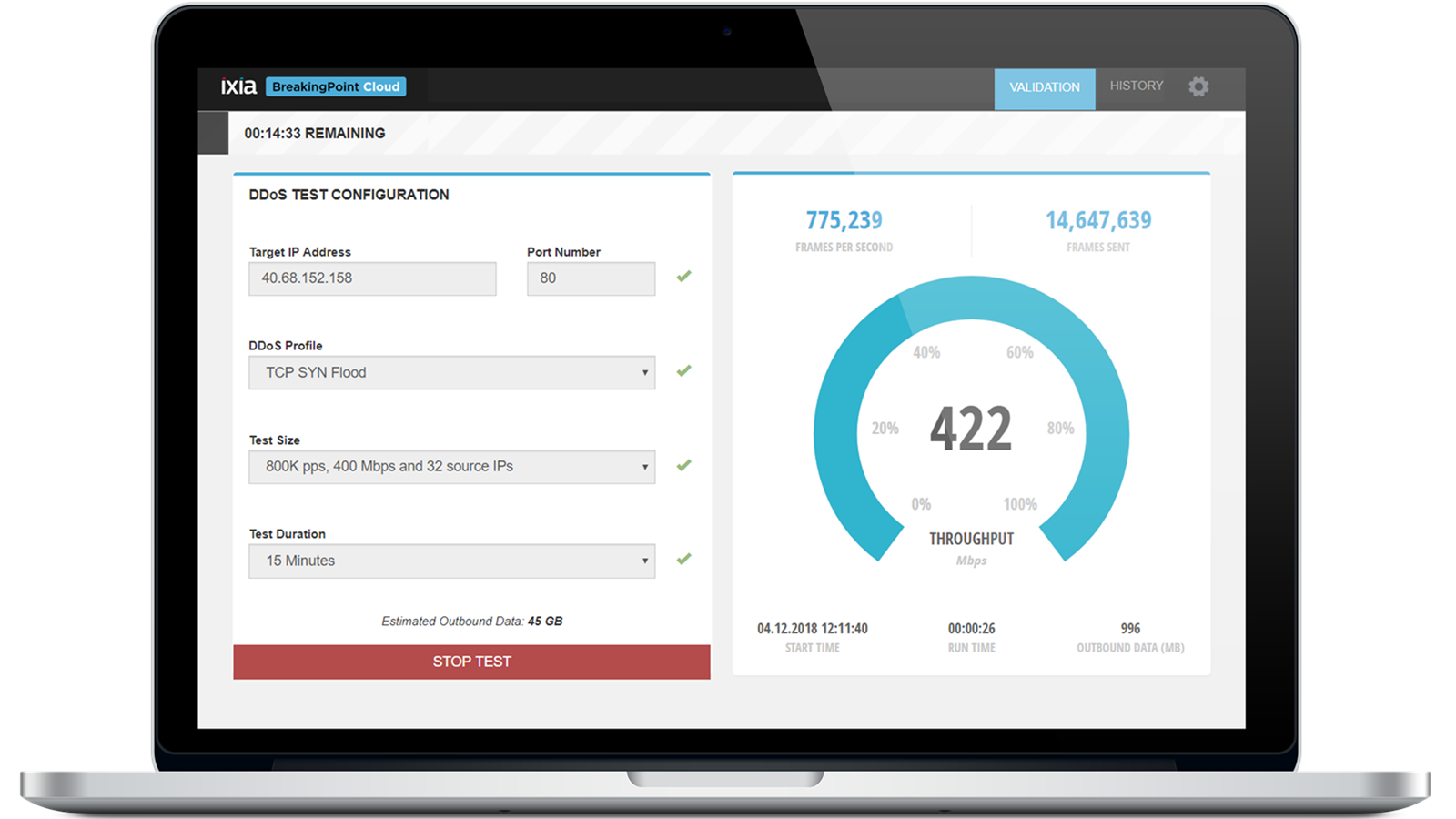
| Configuration management | CM.L2-3.4.4 | Security impact analysis | BreakingPoint, Threat Simulator, and Cyperf |
| Audit and accountability | AU.L2-3.3.7 | Authoritative time source | TimeKeeper |
| Audit and accountability | AU.L2-3.3.1 | System auditing | Network packet brokers |
| Awareness and training | AT.L2-3.2.2 | Role-based training | Cyber Range |
| Access control | AC.L2-3.1.3 | Control CUI flow | Cyperf |
Domain |
Practice no. |
Requirement name |
Product |
|---|---|---|---|
| System and information integrity | SI.L3-3.14.3 |
Threat information related to specific threats |
Threat Simulator and Application Threat Intelligence |
| System and information integrity | SI.L3-3.14.3 |
Specialized asset security |
|
| Security assessment | CA.L3-3.12.1 | Automated penetration testing | Threat Simulator |
| Risk assessment | RA.L3-3.11.5 | Security solution effectiveness | Threat Simulator, Cyperf, and BreakingPoint |
| Risk assessment | RA.L3-3.11.2 | Threat Hunting |
Threat Simulator and Network packet brokers |
| Risk assessment | RA.L3-3.11.6 | Supply-chain risk response | IoT Security Assessment |
| Risk assessment | RA.L3-3.11.1 | Threat-informed risk assessment |
Threat Simulator |
| Incident response | IR.L3-3.6.2 | Cyber incident response team | Threat Simulator and Network packet brokers |
| Incident response | IR.L3-3.6.1 | Security operations center | Threat Simulator, Cyber Range, and Network packet brokers |
| Identification and authentication | CM.L3-3.5.1 | Bidirectional authentication | Cyperf and Keysight Eggplant |
| Configuration management | CM.L3-3.4.3 | Automated inventory | Network packet brokers |
| Configuration management | CM.L3-3.4.2 | Automated mechanisms to detect misconfigured or unauthorized components | Threat Simulator |
| Configuration management | CM.L3-3.4.1 | Authoritative repository |
Threat Simulator |
| Awareness and training | AT.L3-3.2.2 | Practical training exercises | Cyber Range |
| Awareness and training | AT.L3-3.2.1 | Advanced threat awareness | Cyber Range |
Get the Essential CMMC Guide
If you handle controlled unclassified information (CUI) or work within the DoD supply chain, CMMC readiness is critical. Our latest guide walks you through what you need to know about getting certification and reducing delays.
Want help or have questions?