What are you looking for?
Out-of-Band Monitoring Solutions
Smarter network, application, and security monitoring tools
INTELLIGENT VISIBILITY
Visibility powered by a multi-layer security fabric improves enterprise network monitoring performance.
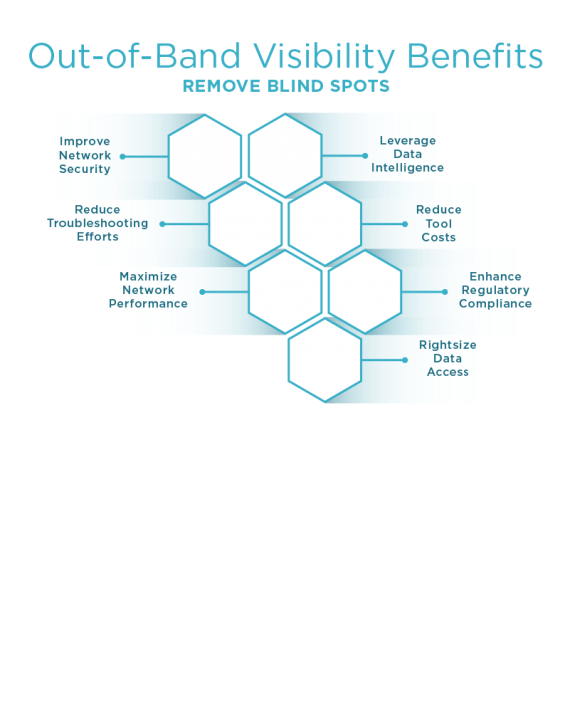
Intelligent network visibility allows IT to strengthen network security, reduce monitoring costs, increase return on investment (ROI), and optimize network performance. Keysight offers the widest range of network taps, virtual network taps, and intelligent network packet brokers (NPBs) that allow you to:
- Remove blind spots to improve network visibility and security
- Leverage application intelligence to improve security and reduce troubleshooting time
- Reduce the costs of monitoring tool investment
- Maximize network performance
- Enhance regulatory compliance
- Reduce downtime and mean time to repair
- Tap into your data from everywhere

REMOVE BLIND SPOTS AND IMPROVE NETWORK MONITORING
Blind spots occur when data is lost on its way to the monitoring and compliance tools or also when security incident data has become buried. Blind spots can occur because of overloaded SPAN ports, not using a Network Packet Broker (NPB) properly sized for your network, or lack of connectivity for tools like DLPs, SIEMs, logging tools, protocol analyzers, etc. It is very common for these blind spots to contribute to network outages, performance issues, security breaches, and compliance problems. The easiest and best answer to solving the problem is to implement a scalable visibility architecture with the industry’s most reliable Taps and highest performing NPBs.
Learn more about how Keysight Network Taps and NPB solutions eliminate blind spots in your network.
CONTEXT AWARENESS SUPERCHARGES NETWORK MONITORING PERFORMANCE
Context awareness is a powerful capability to improve network operations. Context-aware data processing allows the right data to be distributed the right tools through data deduplication, packet trimming, burst protection, and especially application level filtering. These combined features help expose indicators of compromise, identify geolocation of users and devices, and improve troubleshooting efforts.
EXTEND THE LIFE OF EXISTING MONITORING TOOL INVESTMENTS
Modern enterprise networks typically have several problems when it comes to getting the most value out of their monitoring tools. A visibility solution provides capabilities for clear cost reductions by eliminating various issues like:
- Access to the proper data
- Reducing the need to constantly add new monitoring tools
- Ensuring monitoring tool capabilities match the network security
An intelligent visibility framework helps every monitoring tool see more and focus in on the data that matters most to you.
Learn more about how Keysight can help you extend the life of your monitoring tools:


MAXIMIZE NETWORK PERFORMANCE TO SEE THE WHOLE PICTURE
IT security and analytics tools are only as good as the data they are seeing. Performance matters — don't settle for partial visibility due to dropped packets within your solution. Your tools need complete visibility to properly monitor the network.
In addition, proactive monitoring lets you perform real testing of your network to validate network/application performance and measure SLAs whenever you need to.
Learn more about how Keysight can help you see what you have been missing and maximize network performance:
Visibility Enhances Regulatory Compliance
Better network visibility and control of data allows enterprises to enhance regulatory compliance. This includes PCI DSS, HIPAA, lawful intercept, and various other compliance initiatives. The key is to capture the proper data, segment it out, and then deliver it to the proper location.
Learn more about how Keysight can help you enhance regulatory compliance:
Reduce Your Network Downtime And Mean Time To Repair
During breaches and outages, minutes matter. This is where a visibility architecture can reduce network downtime. Once a tap and network packet broker (NPB) are inserted into the network you can drastically reduce Change Board approvals and the use of Crash Carts for troubleshooting. Your processes and capabilities will be faster than before, especially when remote access capability is deployed.
Learn more about how Keysight delivers the solution you need to reduce downtime:


Tap Into Your Data Where And When You Need It
Network visibility starts with capturing the proper data from physical and virtual networks (both public and private) to enable a deeper, richer understanding of your network.
The data you may need can come from anywhere within your network. Deploy the physical and virtual taps you need, where you need to get that data. This gives your monitoring solution the right data so it can be delivered to the right tool when needed.
Keysight is the number one vendor in the network taps market. Learn more how Keysight can help you tap your network:
Related Products
Maximize the value of security and monitoring tools.
Find out more.