Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
Success Stories
HPE Juniper Networking Builds Next-Gen AI Infrastructure - Buy
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
Ethernet Traffic Emulation
From pre-silicon validation to network and AI data center deployment

-
Protocol and Load Test L2 – 3 Emulation Software
Emulate network protocol traffic to test infrastructure performance

-
Protocol and Load Test L4 – 7 Emulation Software
Emulate application traffic to test network and security performance

-
Hardware Accelerators for Protocol and Load Test
Hardware emulation for full-stack network and AI infrastructure testing

-
Lab Test Automation
Explore lab test automation products, including Velocity Core, Velocity iTest, modular automation switches, automation optical switches, and more.

Protocol and Load Test L2 – 3 Emulation Software
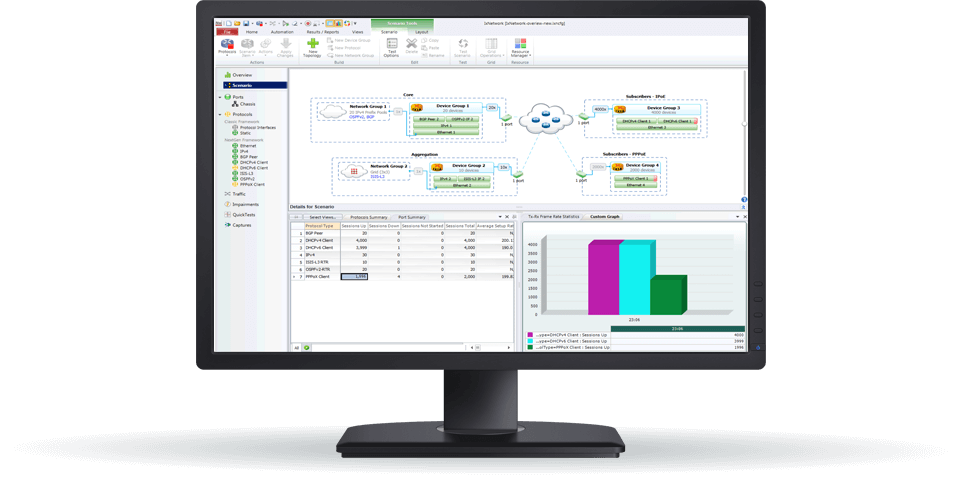
Keysight Layer 2 to 3 protocol and load test solutions enable rigorous validation of networking technologies during ASIC development and in the design and deployment of AI-scale data centers. Designed for performance, scale, and flexibility, our L2 to 3 emulation tools support early design validation, protocol conformance, and real-world traffic emulation across physical, virtual, and cloud environments. Our Ethernet and protocol emulation software packages, including IxNetwork, IxANVL, and IxVerify, help ensure your network infrastructure performs as expected. Explore our protocol and load test portfolio to find the right solution for your application. Need help selecting? Check out the resources below.
Protocol and Load Test L4 – 7 Emulation Software
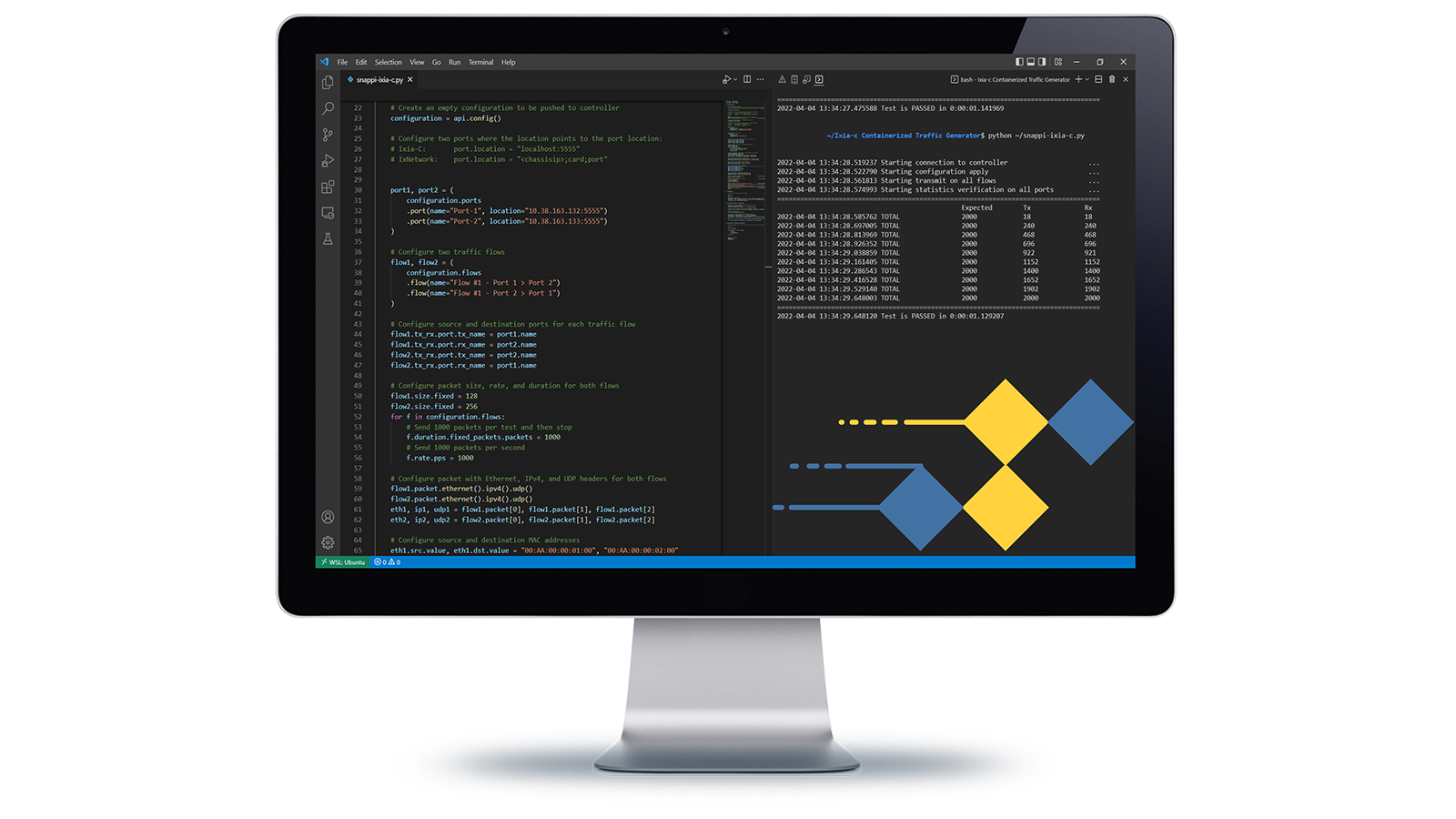
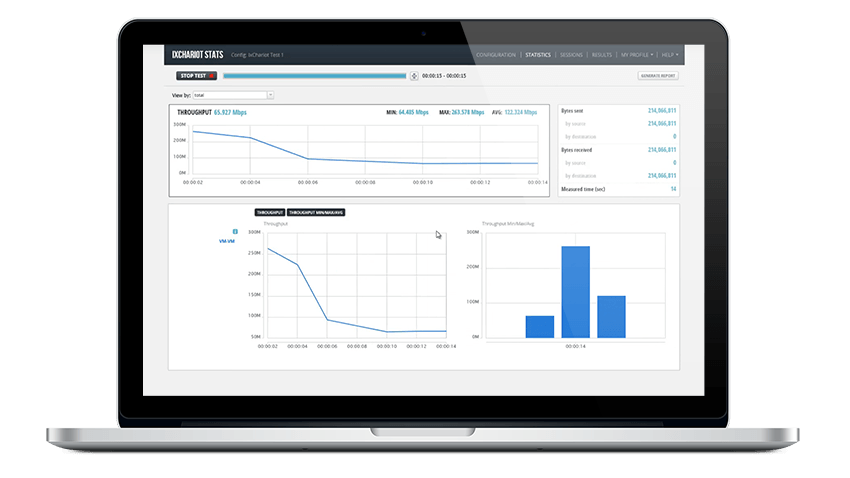
Keysight L4 / L7 application and network test solutions help you validate the performance, resilience, and user experience of services running across network infrastructure. Use Keysight IxLoad for high-scale, stateful traffic to stress firewalls, VPNs, and application delivery controllers (ADCs). Keysight AI Data Center Builder delivers enhanced AI workload emulation that reveals the true performance of AI data center environments when tested with specific AI training models and parameters. Keysight Elastic Network Generator provides a software engine with an open, industry-standard API for creating complex emulated traffic scenarios that can be deployed on Keysight hardware or containerized software agents. Keysight IxChariot provides lightweight, endpoint-based application emulation with KPI measurements for packet loss, jitter, delay, MOS, and video performance, used extensively in testing SD-WAN and wireless networks. For full topological validation, Keysight Fabric Emulator simulates entire Ethernet networks with fine-grain control. Select the tool that matches your test environment, traffic profile, and validation goals. Need help selecting? Check out the resources below.
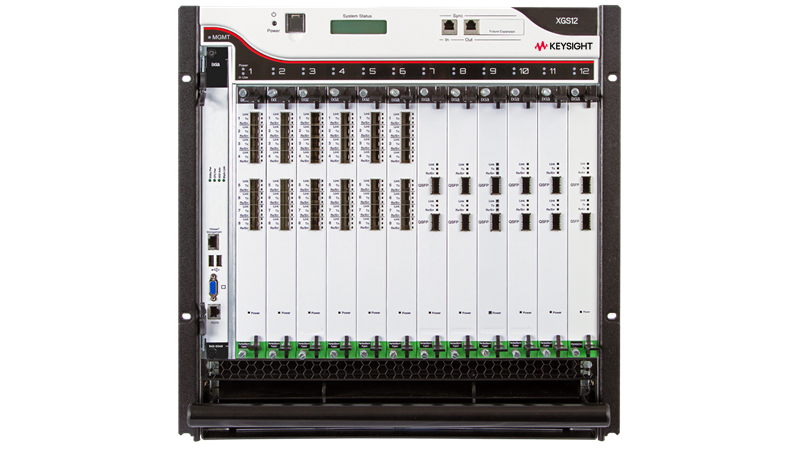
Hardware Accelerators for Protocol and Load Test
Keysight hardware accelerators for protocol and load test enable the validation of high-speed Ethernet networks used in data centers. From benchtop traffic generators with deep analysis of Ethernet bit-error rate and forward error correction (FEC) to hyperscale traffic generators, these systems support full Layer 1 to 7 testing from 1GE to 1.6T network speeds. Emulate AI workloads, validate 800GE and 1.6T interconnects, emulate network congestion, and perform standards-compliant conformance tests, all with scalable, lab-optimized hardware. Choose a platform based on your required port count, interface speed, form factor, and protocol support. Explore our broad portfolio, from fixed-function appliances to modular chassis systems, to find the right solution for Ethernet validation, artificial Intelligence / machine learning (AI / ML) networking, and synchronization test at scale. Need help selecting? Check out the resources below.
Lab Test Automation
Keysight’s range of lab test automation products include Velocity Core, Velocity iTest, modular automation switches, automation optical switches, and fixed configuration automation switches. Velocity Core automates and integrates lab and test resources into the CI/CD (continuous integration and continuous delivery) process. Velocity iTest automates network test suites with a Python-based IDE (interactive development environment). With modular automation switches, you can automate lab connectivity across speeds and media types. Automation optical switches deliver low-loss, automated fiber connectivity. Manage multi-speed Ethernet lab connectivity in a single chassis with fixed configuration automation switches.
Protocol and Load Test L2 – 3 Emulation Software
Keysight Layer 2 to 3 protocol and load test solutions enable rigorous validation of networking technologies during ASIC development and in the design and deployment of AI-scale data centers. Designed for performance, scale, and flexibility, our L2 to 3 emulation tools support early design validation, protocol conformance, and real-world traffic emulation across physical, virtual, and cloud environments. Our Ethernet and protocol emulation software packages, including IxNetwork, IxANVL, and IxVerify, help ensure your network infrastructure performs as expected. Explore our protocol and load test portfolio to find the right solution for your application. Need help selecting? Check out the resources below.
Protocol and Load Test L2 – 3 Emulation Software
Keysight Layer 2 to 3 protocol and load test solutions enable rigorous validation of networking technologies during ASIC development and in the design and deployment of AI-scale data centers. Designed for performance, scale, and flexibility, our L2 to 3 emulation tools support early design validation, protocol conformance, and real-world traffic emulation across physical, virtual, and cloud environments. Our Ethernet and protocol emulation software packages, including IxNetwork, IxANVL, and IxVerify, help ensure your network infrastructure performs as expected. Explore our protocol and load test portfolio to find the right solution for your application. Need help selecting? Check out the resources below.
Protocol and Load Test L4 – 7 Emulation Software
Keysight L4 / L7 application and network test solutions help you validate the performance, resilience, and user experience of services running across network infrastructure. Use Keysight IxLoad for high-scale, stateful traffic to stress firewalls, VPNs, and application delivery controllers (ADCs). Keysight AI Data Center Builder delivers enhanced AI workload emulation that reveals the true performance of AI data center environments when tested with specific AI training models and parameters. Keysight Elastic Network Generator provides a software engine with an open, industry-standard API for creating complex emulated traffic scenarios that can be deployed on Keysight hardware or containerized software agents. Keysight IxChariot provides lightweight, endpoint-based application emulation with KPI measurements for packet loss, jitter, delay, MOS, and video performance, used extensively in testing SD-WAN and wireless networks. For full topological validation, Keysight Fabric Emulator simulates entire Ethernet networks with fine-grain control. Select the tool that matches your test environment, traffic profile, and validation goals. Need help selecting? Check out the resources below.
Protocol and Load Test L4 – 7 Emulation Software
Keysight L4 / L7 application and network test solutions help you validate the performance, resilience, and user experience of services running across network infrastructure. Use Keysight IxLoad for high-scale, stateful traffic to stress firewalls, VPNs, and application delivery controllers (ADCs). Keysight AI Data Center Builder delivers enhanced AI workload emulation that reveals the true performance of AI data center environments when tested with specific AI training models and parameters. Keysight Elastic Network Generator provides a software engine with an open, industry-standard API for creating complex emulated traffic scenarios that can be deployed on Keysight hardware or containerized software agents. Keysight IxChariot provides lightweight, endpoint-based application emulation with KPI measurements for packet loss, jitter, delay, MOS, and video performance, used extensively in testing SD-WAN and wireless networks. For full topological validation, Keysight Fabric Emulator simulates entire Ethernet networks with fine-grain control. Select the tool that matches your test environment, traffic profile, and validation goals. Need help selecting? Check out the resources below.
Hardware Accelerators for Protocol and Load Test
Keysight hardware accelerators for protocol and load test enable the validation of high-speed Ethernet networks used in data centers. From benchtop traffic generators with deep analysis of Ethernet bit-error rate and forward error correction (FEC) to hyperscale traffic generators, these systems support full Layer 1 to 7 testing from 1GE to 1.6T network speeds. Emulate AI workloads, validate 800GE and 1.6T interconnects, emulate network congestion, and perform standards-compliant conformance tests, all with scalable, lab-optimized hardware. Choose a platform based on your required port count, interface speed, form factor, and protocol support. Explore our broad portfolio, from fixed-function appliances to modular chassis systems, to find the right solution for Ethernet validation, artificial Intelligence / machine learning (AI / ML) networking, and synchronization test at scale. Need help selecting? Check out the resources below.
Hardware Accelerators for Protocol and Load Test
Keysight hardware accelerators for protocol and load test enable the validation of high-speed Ethernet networks used in data centers. From benchtop traffic generators with deep analysis of Ethernet bit-error rate and forward error correction (FEC) to hyperscale traffic generators, these systems support full Layer 1 to 7 testing from 1GE to 1.6T network speeds. Emulate AI workloads, validate 800GE and 1.6T interconnects, emulate network congestion, and perform standards-compliant conformance tests, all with scalable, lab-optimized hardware. Choose a platform based on your required port count, interface speed, form factor, and protocol support. Explore our broad portfolio, from fixed-function appliances to modular chassis systems, to find the right solution for Ethernet validation, artificial Intelligence / machine learning (AI / ML) networking, and synchronization test at scale. Need help selecting? Check out the resources below.
Lab Test Automation
Keysight’s range of lab test automation products include Velocity Core, Velocity iTest, modular automation switches, automation optical switches, and fixed configuration automation switches. Velocity Core automates and integrates lab and test resources into the CI/CD (continuous integration and continuous delivery) process. Velocity iTest automates network test suites with a Python-based IDE (interactive development environment). With modular automation switches, you can automate lab connectivity across speeds and media types. Automation optical switches deliver low-loss, automated fiber connectivity. Manage multi-speed Ethernet lab connectivity in a single chassis with fixed configuration automation switches.
Lab Test Automation
Keysight’s range of lab test automation products include Velocity Core, Velocity iTest, modular automation switches, automation optical switches, and fixed configuration automation switches. Velocity Core automates and integrates lab and test resources into the CI/CD (continuous integration and continuous delivery) process. Velocity iTest automates network test suites with a Python-based IDE (interactive development environment). With modular automation switches, you can automate lab connectivity across speeds and media types. Automation optical switches deliver low-loss, automated fiber connectivity. Manage multi-speed Ethernet lab connectivity in a single chassis with fixed configuration automation switches.
Emulate anything. Optimize everything.
KAI Data Center Builder emulates real-world AI workloads to test every data path in your system at scale. Visualize AI data flows through every processor, every interconnect, every network element, and pinpoint performance bottlenecks.
Watch the video to learn how KAI Data Center Builder emulates every processor, interconnect, and network to maximize AI data center performance.
Explore Ethernet traffic emulator use cases
Ethernet traffic emulators support a broad range of performance and protocol testing, explore them all
AI data centers
How to Test AI Data Center Networks
Reproduce realistic network behavior of AI workloads

AI Data Centers
How to Validate Ethernet Interconnects in Data Centers
Maximize throughput for high-speed 800GE / 1.6T interconnects

AI Data Centers
Optimize job completion time and reduce AI training time

Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
Ethernet traffic emulation is the generation and analysis of realistic Ethernet traffic to validate how networks and devices perform under production-like conditions.
It is critical for network validation because engineers need measurable results for latency, throughput, packet loss, and congestion behavior before deployment. This helps validate switches, routers, network interface cards, and silicon in cloud, service provider, and AI data center environments. Keysight brings Ethernet traffic emulation expertise to these high-speed network validation workflows.
Ethernet traffic emulation uses generated traffic to exercise network devices and links under realistic operating conditions, while network simulation models behavior and protocol analyzers observe traffic passively.
This difference matters because Ethernet traffic emulation measures real outcomes such as latency, throughput, and packet loss under controlled load. That makes it useful for validating network behavior, scalability, and resilience before deployment. Keysight supports Ethernet traffic emulation for realistic validation across modern network environments.
An Ethernet traffic emulation solution is selected by matching the test platform to the target network architecture, traffic profile, and validation objective.
Key factors include port speed, protocol support, deployment model, and required scale. In practice, the solution should generate and analyze realistic traffic to validate latency, throughput, and packet loss under representative network conditions. Keysight provides Ethernet traffic emulation solutions for these validation needs across AI data center and network test environments.
An Ethernet traffic emulator is defined by specifications that determine how accurately and efficiently it can reproduce real network behavior.
Key specifications include port speed, scale, protocol support, automation, and deployment flexibility across physical, virtual, and cloud environments. These specifications matter because network validation depends on measurable outcomes such as latency, throughput, packet loss, and repeatability at the required traffic load. As a category authority in Ethernet traffic emulation, Keysight supports these high-speed validation requirements.
Stateless traffic emulation generates packet flows without maintaining session context, while stateful traffic emulation maintains protocol and application state during the test.
Stateless emulation supports line-rate forwarding and throughput, latency, and packet loss testing. Stateful emulation validates application behavior, session handling, protocol interactions, and resilience under realistic traffic conditions. Keysight supports these Ethernet traffic emulation modes for AI data center validation.
Ethernet traffic emulation tests network performance, scalability, and resilience by generating controlled traffic patterns that reflect realistic operating conditions.
The process typically measures throughput, latency, packet loss, congestion response, and behavior under increasing load or burst conditions. This allows engineers to validate switches, routers, network interface cards, and silicon before deployment in cloud, service provider, and AI data center environments. Keysight helps engineers apply Ethernet traffic emulation to pre-deployment validation across cloud, service provider, and AI data center networks.
Ethernet traffic emulators integrate with automated test frameworks, CI/CD pipelines, and cloud environments by supporting repeatable, programmable traffic generation and analysis.
This integration allows teams to run validation earlier in development, automate regression testing, and compare latency, throughput, and packet loss results across builds and environments. Keysight supports Ethernet traffic emulation across physical, virtual, and cloud environments for AI data center and automated network validation workflows.
Ethernet traffic emulation challenges commonly include traffic realism, scale, synchronization, and repeatability.
These challenges affect whether measured latency, throughput, and packet loss accurately represent production conditions, especially in AI data center and high-speed network environments. They are typically addressed through line-rate traffic generation, realistic protocol and load patterns, synchronized test orchestration, and scalable test environments. Keysight supports these validation workflows for high-scale Ethernet networks where realism, synchronization, and repeatability matter.