Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
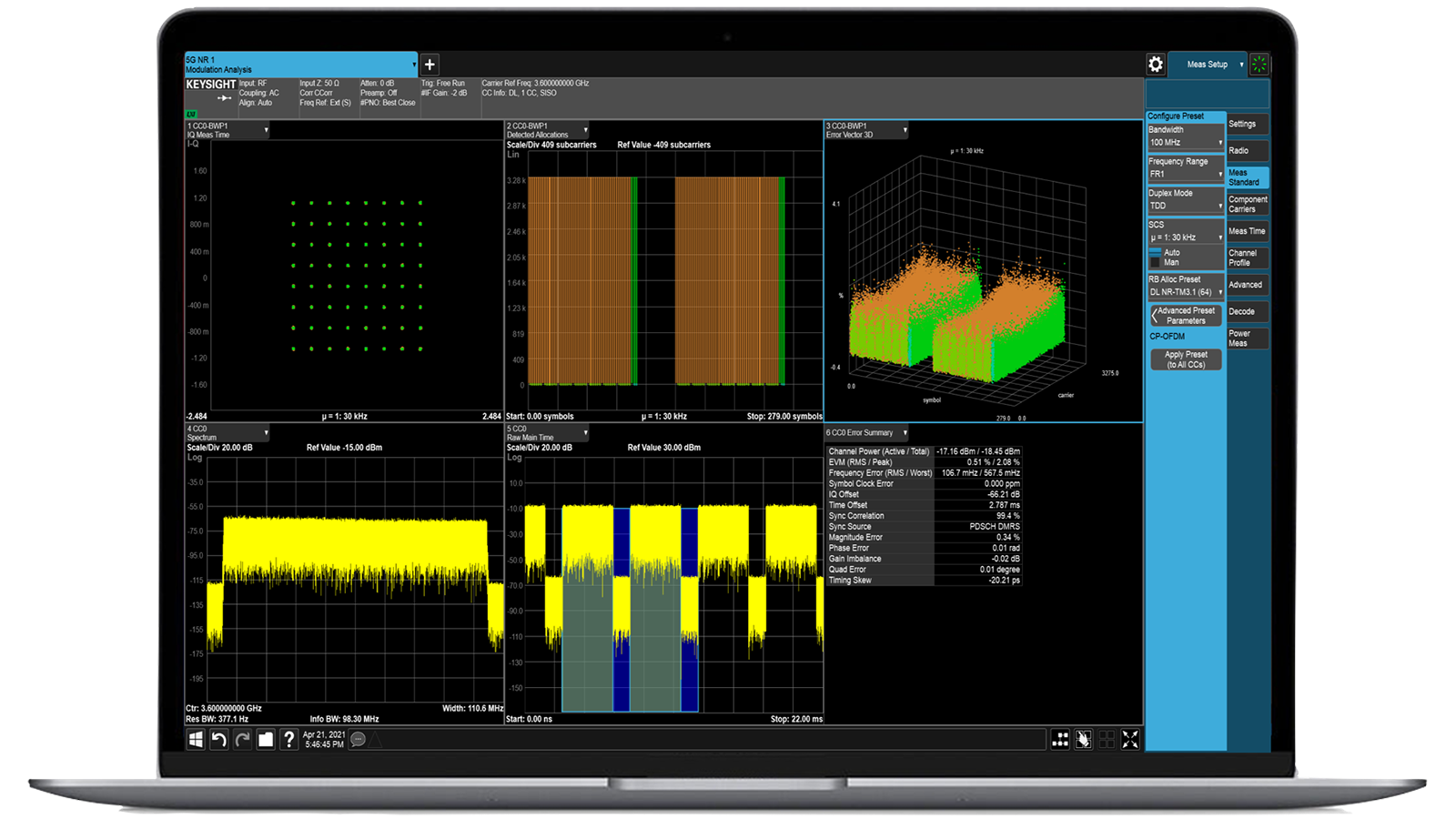
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
PerfectStorm ONE Enterprise-scale application and security testing

- Overview
- All Models
- Accessories
- Software
- Support
Emulate real-world traffic and security scenarios at scale
Keysight PerfectStorm ONE systems bring high-performance traffic generation into a compact, portable form factor. It delivers scalable and realistic application testing for network devices, SD-WAN solutions, and virtualized environments. With integrated traffic and threat emulation, it enables stateful Layer 2–7 flow generation and advanced security testing in a single appliance. PerfectStorm ONE systems support hundreds of application profiles, malware simulations, and protocol exploits. This makes it ideal for agile development workflows, CI/CD pipelines, and remote site validation without sacrificing fidelity or control. If custom port configurations are required, consider the XGS chassis paired with PerfectStorm modular generators, which allow for custom port configurations across multiple test modules. Request a quote for one of our popular configurations today. Need help selecting? Check out the resources below.
Integrated portable design
Portable chassis with a built-in controller and traffic engine, enabling quick setup in labs, branch offices, or remote sites.
High-throughput traffic generation
Emulates realistic application traffic and diverse attack scenarios at multi-gigabit speeds to stress test modern networks.
Flexible operation and scalability
Upgradeable licenses and adaptable port configurations let you expand coverage as performance and security needs grow.
Unified test ecosystem
Seamlessly integrates with Keysight security attack emulation software platforms, ensuring consistent workflows across environments.

-
Ports
2 to 8
-
Interface
SFP+, QSFP+
-
Interface speed modes
10GE, 1GE, 40GE
-
Software compatibility
IxLoad, BreakingPoint
-
Additional features
Hardware-based traffic capture (available in BreakingPoint)
Most popular configurations

PerfectStorm ONE Fusion, 10GE / 1GE 8-Port SFP+ Appliance (PS10GE8NG)
PerfectStorm ONE Fusion, 10GE / 1GE 8-Port SFP+ Appliance (PS10GE8NG)
941-0027
The Keysight PerfectStorm ONE Fusion includes a 10GE eight-port SFP+ appliance (PS10GE8NG).
- Establish a scalable and transportable POC lab for customer evaluations using custom traffic scenarios.
- Use the unified architecture to support Keysight BreakingPoint and IxLoad applications.
- Perform software licensing upgrades to enable affordable 4 Gbps performance with easy expansion for future needs of up to 80 Gbps.
- Achieve high performance levels using the compact form factor and reduced power requirements.
- Use hardware-based acceleration for Secure Sockets Layer and Internet Protocol security.

PerfectStorm ONE Fusion 10GE / 1GE 4-Port SFP+ Appliance (PS10GE4NG)
PerfectStorm ONE Fusion 10GE / 1GE 4-Port SFP+ Appliance (PS10GE4NG)
941-0031
The Keysight PerfectStorm ONE Fusion includes a 10GE four-port SFP+ appliance (PS10GE4NG).
- Establish a scalable and transportable POC lab for customer evaluations using custom traffic scenarios.
- Use the unified architecture to support Keysight BreakingPoint and IxLoad applications.
- Perform software licensing upgrades to enable affordable 4 Gbps performance with easy expansion for future needs of up to 80 Gbps.
- Achieve high performance levels using the compact form factor and reduced power requirements.
- Use hardware-based acceleration for Secure Sockets Layer and Internet Protocol security.

PerfectStorm ONE 10GE / 1GE 8-Port SFP+ Appliance (PS10GE8)
PerfectStorm ONE 10GE / 1GE 8-Port SFP+ Appliance (PS10GE8)
941-0037
The Keysight PerfectStorm ONE includes a 10GE eight-port SFP+ appliance (PS10GE8).
- Establish a scalable and transportable POC lab for customer evaluations using custom traffic scenarios.
- Use the unified architecture to support Keysight BreakingPoint and IxLoad applications.
- Perform software licensing upgrades to enable affordable 4 Gbps performance with easy expansion for future needs of up to 80 Gbps.
- Achieve high performance levels using the compact form factor and reduced power requirements.
- Use hardware-based acceleration for Secure Sockets Layer and Internet Protocol security.
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
A high-performance network traffic generator is a system purpose-built to create and transmit extremely realistic network traffic at large scale. Unlike software-only tools that depend on general-purpose servers, these systems use optimized hardware to deliver precise packet timing, deterministic throughput, and support for very high-speed interfaces such as 100 gigabit per second and beyond.
This capability is essential for evaluating firewalls, intrusion detection systems, secure web gateways, and other security appliances because it ensures that test conditions mirror real-world environments. By simulating millions of concurrent users, encrypted traffic flows, and diverse application protocols, organizations can uncover performance bottlenecks, validate reliability under load, and assess resilience against evolving cyberthreats.
In short, high-performance traffic generators make security testing both realistic and scalable, enabling accurate insights before systems are deployed in production.
Hardware acceleration refers to using dedicated processors such as field-programmable gate arrays (FPGAs) and specialized network interface controllers instead of relying solely on central processing units. These components are designed specifically for packet processing and high-throughput tasks.
In the context of network and security validation, hardware acceleration enables precise inter-packet timing, eliminates variability caused by operating systems or hypervisors, and allows for multi-terabit throughput without packet loss. This means that test scenarios can include encrypted traffic, complex application workloads, and simultaneous attack vectors without compromising accuracy.
For organizations, the benefit is clear: security and performance results are trustworthy, repeatable, and scalable to the same conditions that production networks experience.
Firewalls and intrusion prevention systems are designed to handle traffic that is complex, encrypted, and often unpredictable. Simply testing them with uniform or synthetic traffic is not enough, as it fails to expose weaknesses that attackers exploit in the real world. Realistic traffic simulation ensures that tests include common application behaviors such as streaming, file sharing, or web browsing alongside malicious traffic and encrypted sessions.
This mix helps evaluate how security devices balance throughput, latency, and detection accuracy under genuine conditions. For example, deep packet inspection or Transport Layer Security (TLS) decryption can place significant strain on firewalls, reducing performance if resources are not managed properly. By simulating realistic usage patterns, organizations gain visibility into whether their security systems maintain effectiveness and efficiency without creating blind spots or bottlenecks.
Modern enterprises increasingly rely on distributed architectures such as hybrid cloud, multi-cloud, and edge computing. These environments introduce new complexities, including varying latency, dynamic scaling, and multi-tenant workloads. Network traffic simulation helps organizations validate that their infrastructure can deliver consistent performance, secure data flows, and manage traffic spikes before deployment.
By emulating realistic workloads, such as encrypted communications, software-defined wide-area networking (SD-WAN) tunnels, and virtualized network functions, organizations can identify gaps in visibility, potential congestion points, and security policy enforcement challenges. This is particularly valuable in zero-trust environments where traffic inspection and segmentation must operate seamlessly across diverse platforms. Ultimately, traffic simulation helps ensure that cloud migration and distributed deployments are resilient, secure, and optimized for real-world use.
High-scale traffic and attack simulation provides a comprehensive view of how networks and security devices behave under extreme but realistic conditions. Organizations can measure throughput capacity, latency, and jitter to ensure quality of service, while also evaluating how systems respond to malicious traffic, distributed denial-of-service (DDoS) floods, or advanced persistent threats.
Insights go beyond simple pass-or-fail results; testing can reveal thresholds where performance degrades, identify vulnerabilities in configuration, and expose gaps in detection accuracy. By understanding these limits, enterprises, service providers, and government agencies can plan capacity upgrades, fine-tune policies, and strengthen defenses before adversaries exploit weaknesses. This proactive approach transforms security validation into a strategic advantage, reducing risk and improving confidence in mission-critical infrastructure.