Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
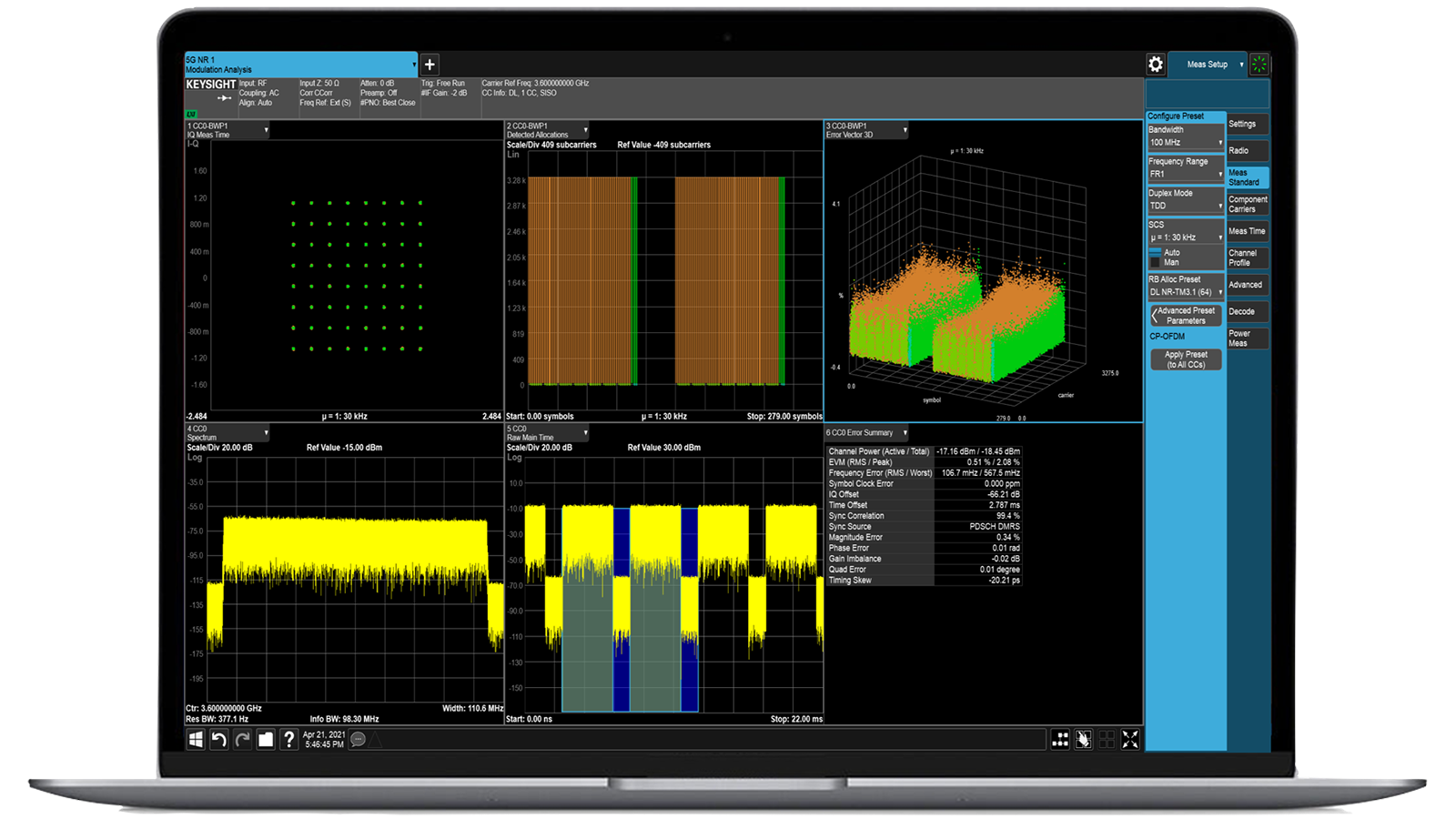
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
BreakingPoint VE Virtual emulator for traffic and threat resilience testing
- Overview
- All Models
- Support
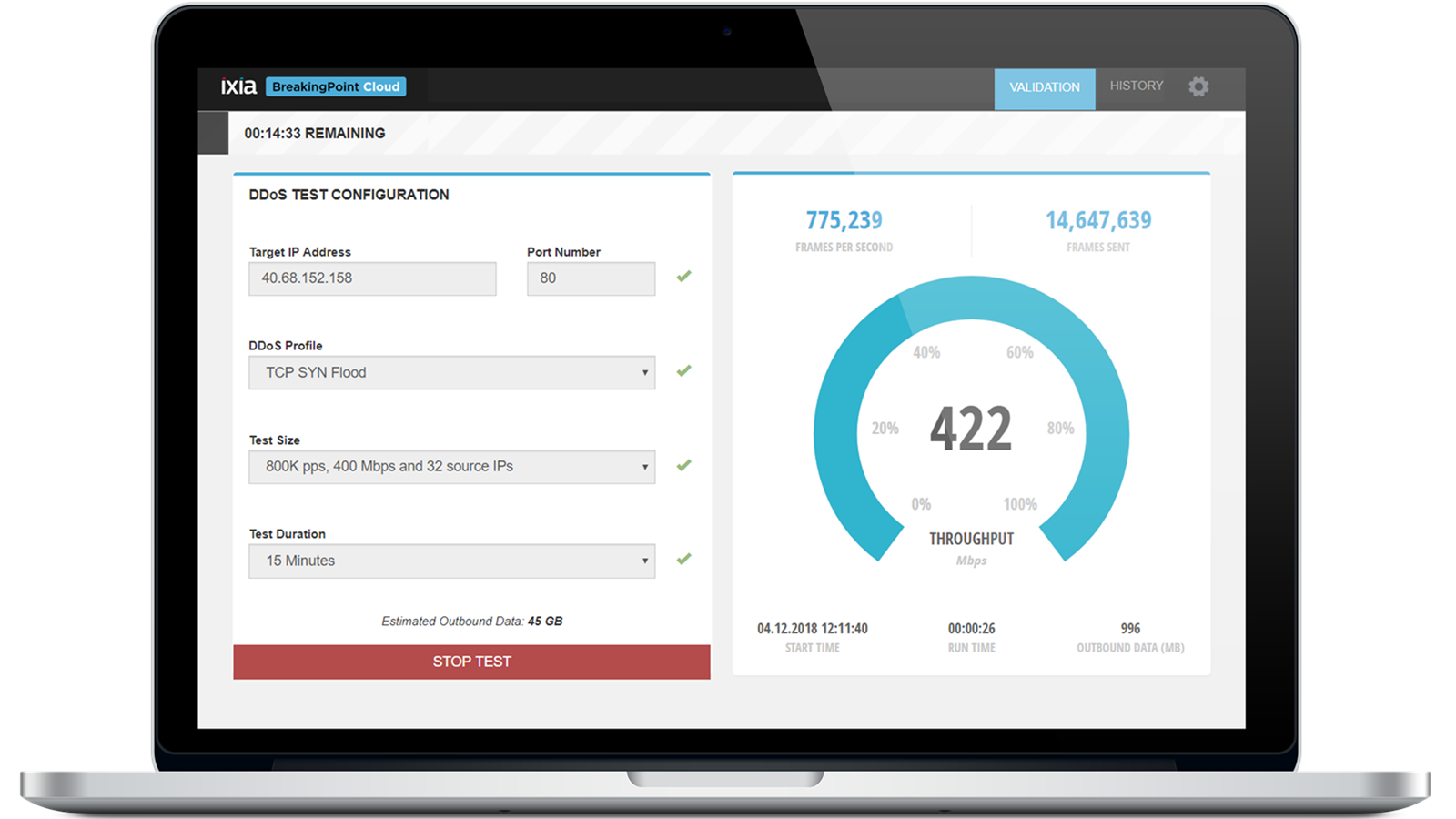
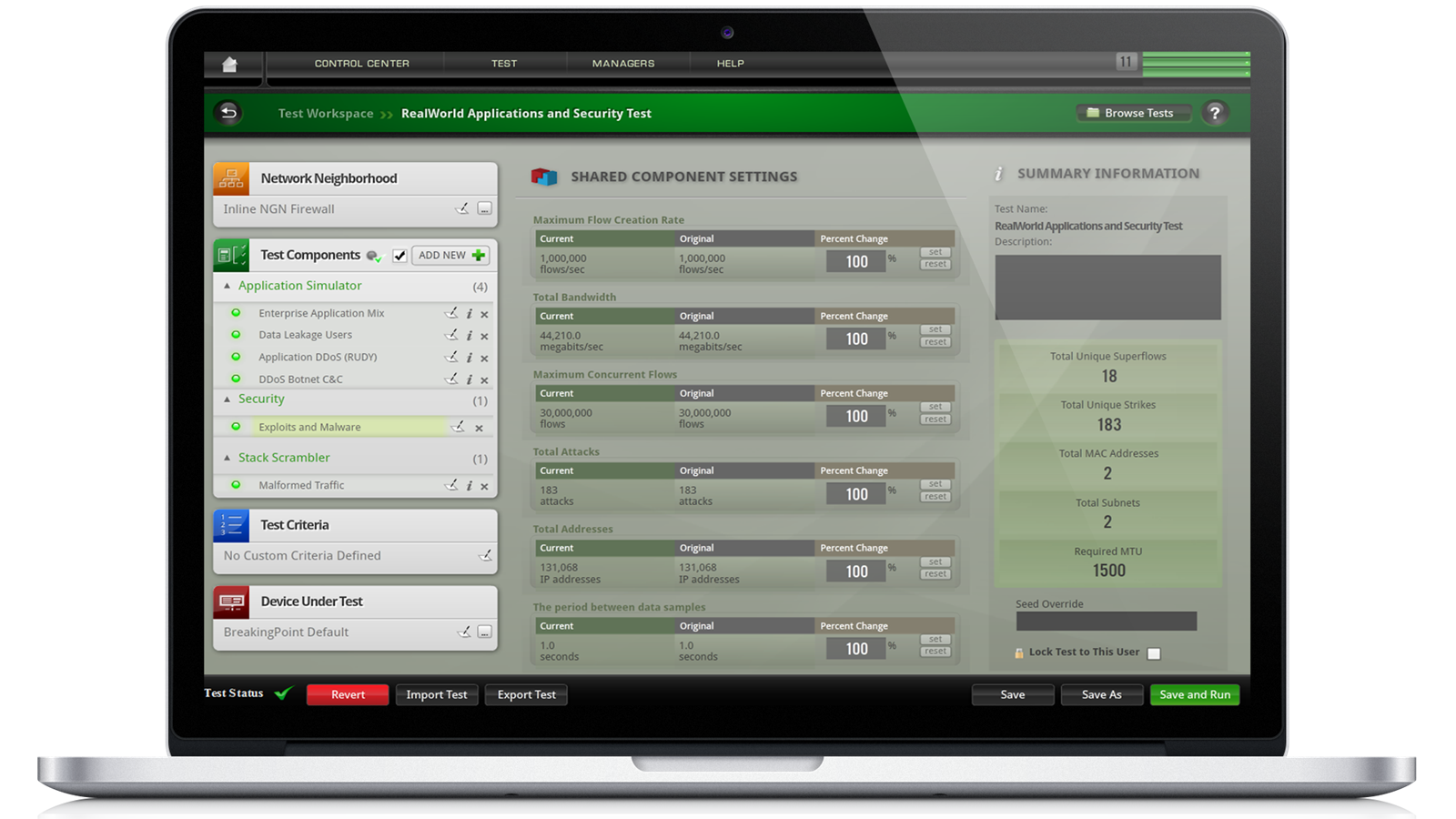
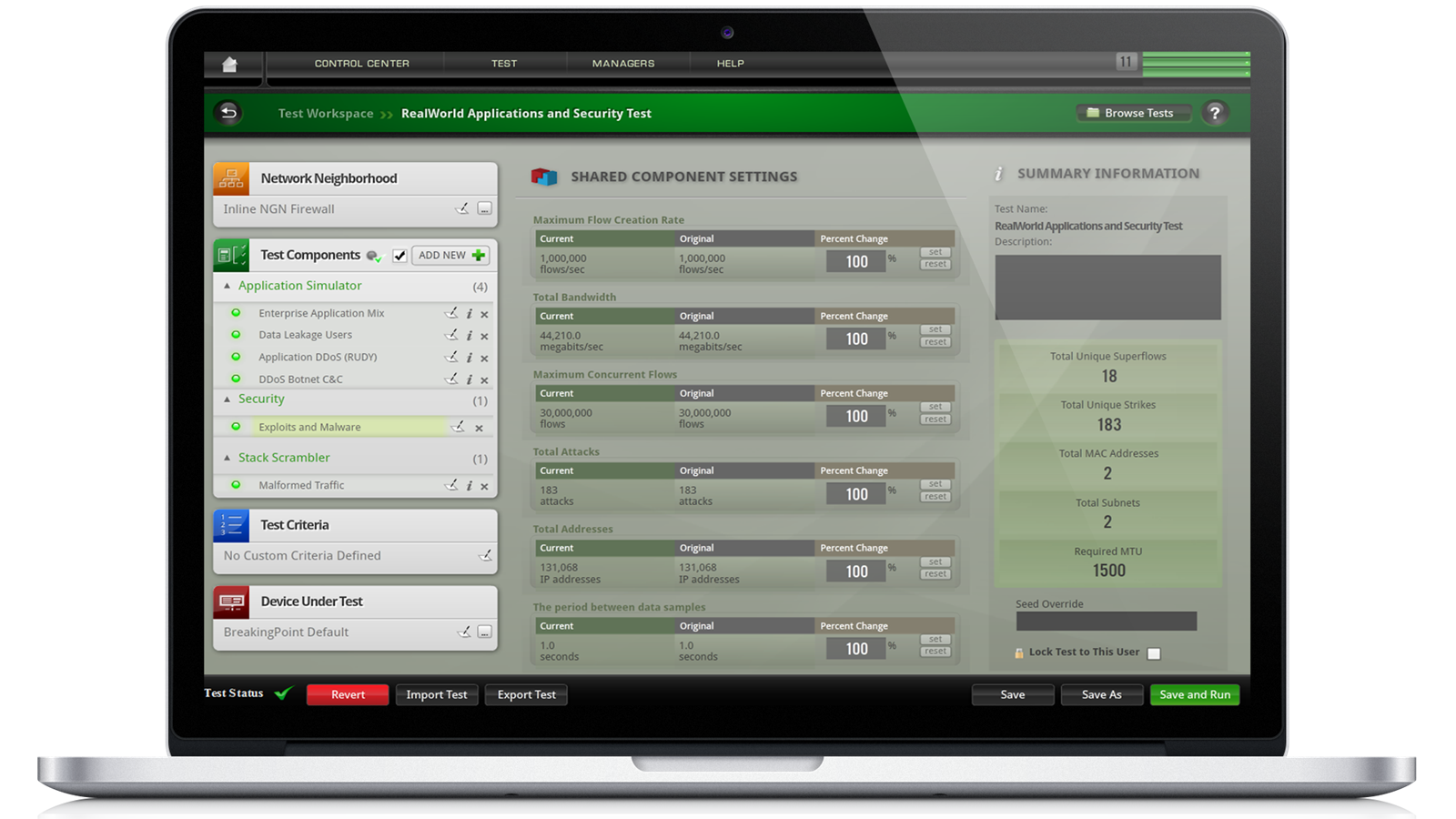
Virtualized security resilience testing for enterprise-wide networks
Keysight BreakingPoint VE software brings proven security capabilities to virtualized and cloud-native test environments. It enables comprehensive security validation for virtual firewalls, cloud-based security controls, and software-defined networks. Integrated into CI/CD pipelines, BreakingPoint VE provides automated, realistic attack emulation to ensure code and configurations are secure before deployment. Request a quote for one of our popular configurations today. Need help selecting? Check out the resources below.
Cloud-native deployment
Launch as a virtual machine across public, private, and hybrid cloud platforms for flexible, on-demand testing.
CI/CD security integration
Seamlessly integrate security testing into DevOps pipelines to validate virtual firewalls, SD-WAN, and VNFs during development.
Elastic test scaling
Scale attack traffic generation across multiple test nodes to simulate real-world volume and behavior.
Threat intelligence
Threat and application library for consistent validation across physical and virtual environments.
Most popular configurations
BreakingPoint Virtual Edition (VE) 10G Floating Perpetual License
BreakingPoint Virtual Edition (VE) 10G Floating Perpetual License
939-9619
The Keysight BreakingPoint virtual edition (VE) 10G includes a floating worldwide perpetual license.
- Test the most critical components of virtual and physical application-aware devices and networks; validate various attacks and distributed denial-of-service defenses.
- Optimize the configuration of virtual or physical network security devices, such as IDS, IPS, DLP, UTM, NGFW, WAF, and web proxy.
- Keep up with the ever-evolving threat landscape by updating your applications, attacks, and malware through daily application and threat intelligence updates.
- Assess how virtual machine mobility impacts application reliability and scalability. Run the tests during live migration to ensure minimal network downtime.
- Validate next-generation 5G / NFV networks by testing in private clouds / telco clouds powered by OpenStack or VMware vCenter orchestration.
- Understand how deployment in different public clouds, such as Alibaba Cloud, Amazon AWS, Google Cloud, and Microsoft Azure, affects network applications.
- Leverage subscription-based licensing that enables the flexibility of a pay-as-you-grow operating expense model with different licenses available in multiple performance levels, such as 1G / 10G / 100G.
BreakingPoint Virtual Edition (VE) 100G 1-Year Subscription License
BreakingPoint Virtual Edition (VE) 100G 1-Year Subscription License
939-9640
The Keysight BreakingPoint virtual edition (VE) 100G includes a 12-month floating worldwide license and a Keysight software support subscription.
- Test the most critical components of virtual and physical application-aware devices and networks; validate various attacks and distributed denial-of-service defenses.
- Optimize the configuration of virtual or physical network security devices, such as IDS, IPS, DLP, UTM, NGFW, WAF, and web proxy.
- Keep up with the ever-evolving threat landscape by updating your applications, attacks, and malware through daily application and threat intelligence updates.
- Assess how virtual machine mobility impacts application reliability and scalability. Run the tests during live migration to ensure minimal network downtime.
- Validate next-generation 5G / NFV networks by testing in private clouds / telco clouds powered by OpenStack or VMware vCenter orchestration.
- Understand how deployment in different public clouds, such as Alibaba Cloud, Amazon AWS, Google Cloud, and Microsoft Azure, affects network applications.
- Leverage subscription-based licensing that enables the flexibility of a pay-as-you-grow operating expense model with different licenses available in multiple performance levels, such as 1G / 10G / 100G.
BreakingPoint Virtual Edition (VE) 1GE Floating Subscription License
BreakingPoint Virtual Edition (VE) 1GE Floating Subscription License
939-9600
The Keysight BreakingPoint virtual edition (VE) 1GE includes a 12-month floating worldwide license and a Keysight software support subscription.
- Test the most critical components of virtual and physical application-aware devices and networks; validate various attacks and distributed denial-of-service defenses.
- Optimize the configuration of virtual or physical network security devices, such as IDS, IPS, DLP, UTM, NGFW, WAF, and web proxy.
- Keep up with the ever-evolving threat landscape by updating your applications, attacks, and malware through daily application and threat intelligence updates.
- Assess how virtual machine mobility impacts application reliability and scalability. Run the tests during live migration to ensure minimal network downtime.
- Validate next-generation 5G / NFV networks by testing in private clouds / telco clouds powered by OpenStack or VMware vCenter orchestration.
- Understand how deployment in different public clouds, such as Alibaba Cloud, Amazon AWS, Google Cloud, and Microsoft Azure, affects network applications.
- Leverage subscription-based licensing that enables the flexibility of a pay-as-you-grow operating expense model with different licenses available in multiple performance levels, such as 1G / 10G / 100G.
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
Virtualized security test platforms provide unique advantages over hardware appliances, especially in environments that are increasingly cloud-centric and software-defined. While physical test hardware is effective for dedicated on-premises labs, it is often expensive, less flexible, and constrained by physical deployment. Virtual solutions, on the other hand, can be deployed rapidly in virtual machines or cloud instances, enabling organizations to test at the same scale and complexity without requiring specialized hardware. They are particularly well-suited for organizations adopting cloud-first strategies, hybrid infrastructures, or continuous integration and continuous delivery pipelines, where tests need to be spun up and torn down on demand. This elasticity helps reduce costs, align with DevOps workflows, and ensure that security validation is embedded seamlessly into agile development processes.
A virtual attack emulation platform enables testing across the full spectrum of network and application security controls. This includes traditional perimeter defenses such as firewalls and intrusion prevention systems, as well as newer cloud-native technologies like secure access service edge (SASE), zero trust network access (ZTNA), and virtualized network functions. Beyond security appliances, these platforms can test endpoint protection tools, content filters, application-layer defenses, and even emerging cloud security services offered by major providers. Because the solution operates in software, it integrates easily into distributed environments, making it possible to test both legacy systems in data centers and modern workloads deployed in public or private clouds. In essence, it ensures that every layer of security, from the edge to the core to the cloud, can be validated under realistic conditions.
Realism is achieved by emulating both benign and malicious traffic patterns at scale. On the application side, platforms can replicate how real users interact with services such as web browsing, email, video streaming, and file sharing, often across encrypted connections. On the threat side, they generate attack campaigns that mirror tactics used by adversaries in the wild, including malware payloads, denial-of-service floods, and protocol exploits. This dual focus creates a testing environment that challenges security controls to distinguish between legitimate traffic and malicious attempts, just as they would need to in production. Furthermore, virtualized platforms often allow customization of traffic profiles, attack intensities, and encryption parameters, giving testers the ability to mirror their unique operational environment. The result is a highly realistic validation process that produces actionable insights about system resilience, scalability, and potential blind spots.
One of the most significant advantages of a virtualized security test platform is the flexible licensing and scaling model it enables. Instead of being limited by the throughput of a physical appliance, organizations can start with modest capacity, perhaps testing a single firewall, virtual private network, or secure web gateway, and then expand seamlessly to validate large-scale distributed systems. Licensing models are typically consumption-based or subscription-based, allowing enterprises to align investment with usage. For instance, a team may run intensive tests only during specific development cycles or compliance audits, and scale back during quiet periods, optimizing cost efficiency. In addition, because the solution is virtual, scaling can occur horizontally across cloud or virtualized infrastructure, leveraging additional compute resources rather than requiring new hardware purchases. This model supports both small labs and global enterprises with complex, multi-site deployments.
Modern security test platforms rely on continuously updated threat intelligence feeds to remain relevant. These updates typically cover new application behaviors, emerging attack vectors, malware campaigns, and advanced evasion techniques observed in the real world. Updates are delivered directly into the emulation library, ensuring that testing reflects the current threat landscape without requiring manual scripting or configuration by the end user. This process is particularly critical given how rapidly cyber threats evolve; an outdated test library would provide a false sense of security. By staying aligned with the latest vulnerabilities and exploits, organizations can validate whether their defenses can withstand current and future attack methods. Beyond simple updates, some platforms also offer the ability to customize and build new attack profiles, giving advanced users the flexibility to model unique threats relevant to their industry or environment. This ensures that testing not only covers known risks but also anticipates potential future attack strategies.