Per saperne di più
segmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testingsegmentation:business-unit/EISG,segmentation:campaign/Software_Test,segmentation:product-category/Test_Automation_Software,keysight:product-lines/eg,keysight:dtx/solutions/facets/development-area/software,keysight:dtx/solutions/facets/workflow-stage/qa,keysight:dtx/solutions/facets/design-and-test-product/software-test,segmentation:software-type/Test_Automation,keysight:dtx/solutions/facets/industry/enterprise-it,keysight:dtx/solutions/facets/industry/aerospace-and-defense,keysight:dtx/solutions/facets/industry/healthcare,segmentation:funnel/bofu,segmentation:product-category/Test_Automation_Software/Software_Application_Testing
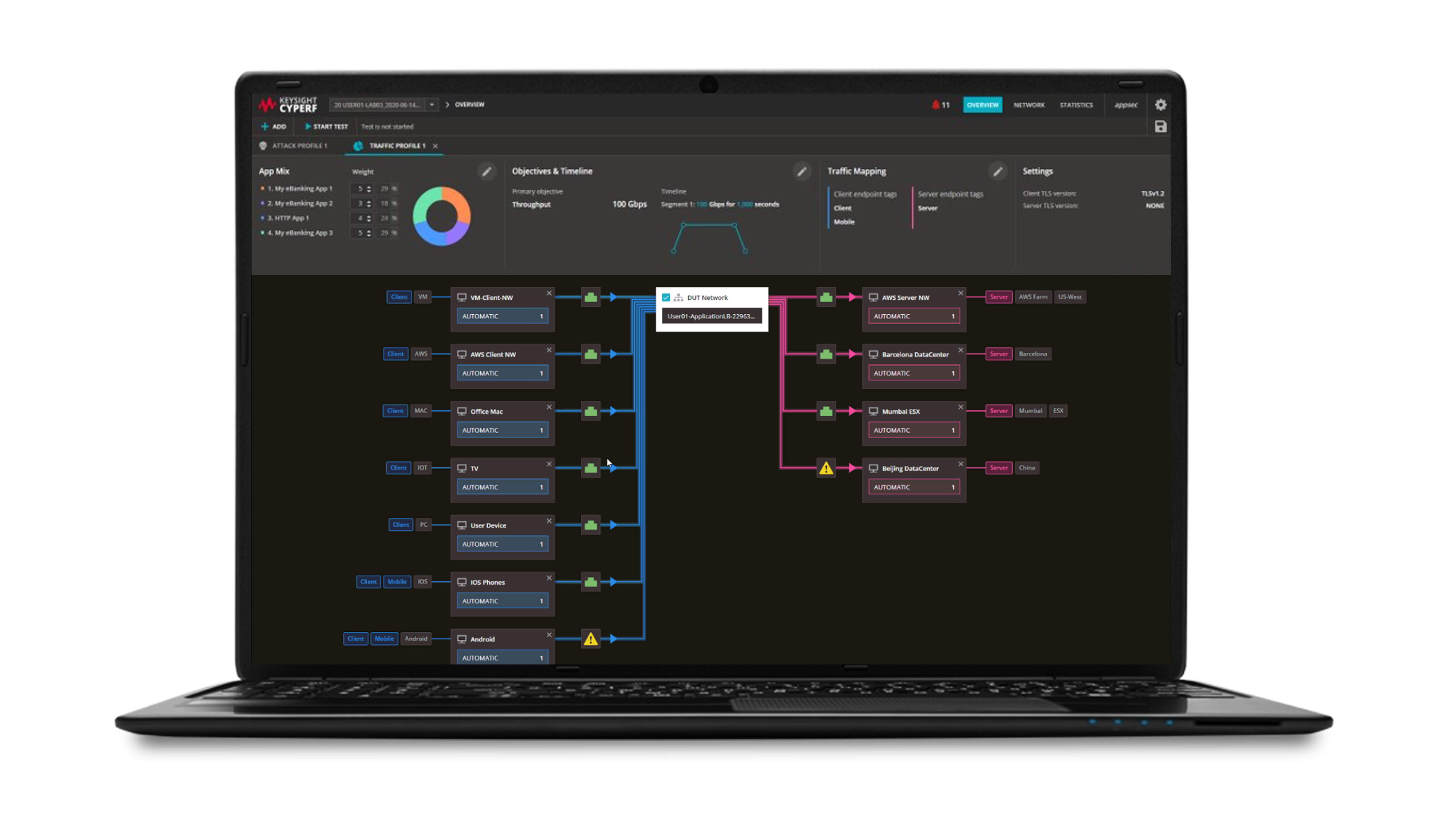
Come scalare il monitoraggio delle prestazioni delle applicazioni
L'ottimizzazione dell'esperienza del cliente e delle conversioni richiede il monitoraggio dinamico delle prestazioni di siti web e applicazioni. Scoprite come ottenere risultati con il software di monitoraggio delle prestazioni delle applicazioni.
Per saperne di più