Choose a country or area to see content specific to your location
Che cosa sta cercando?
-
-
Progettista di interconnessioni 3D
3D Interconnect Designer offre un ambiente flessibile di modellazione e ottimizzazione per qualsiasi struttura di interconnessione avanzata, inclusi chiplet, chip impilati, contenitori e circuiti stampati.

-
Risparmia fino al 50% sull'acquisto di un oscilloscopio XR8
Ottieni una convalida digitale più rapida a un prezzo inferiore grazie alla permuta.

-
Scopri Keysight AI Data Center Builder
Emula ogni parte dell'infrastruttura del tuo data center. Emula qualsiasi cosa. Ottimizza tutto.

-
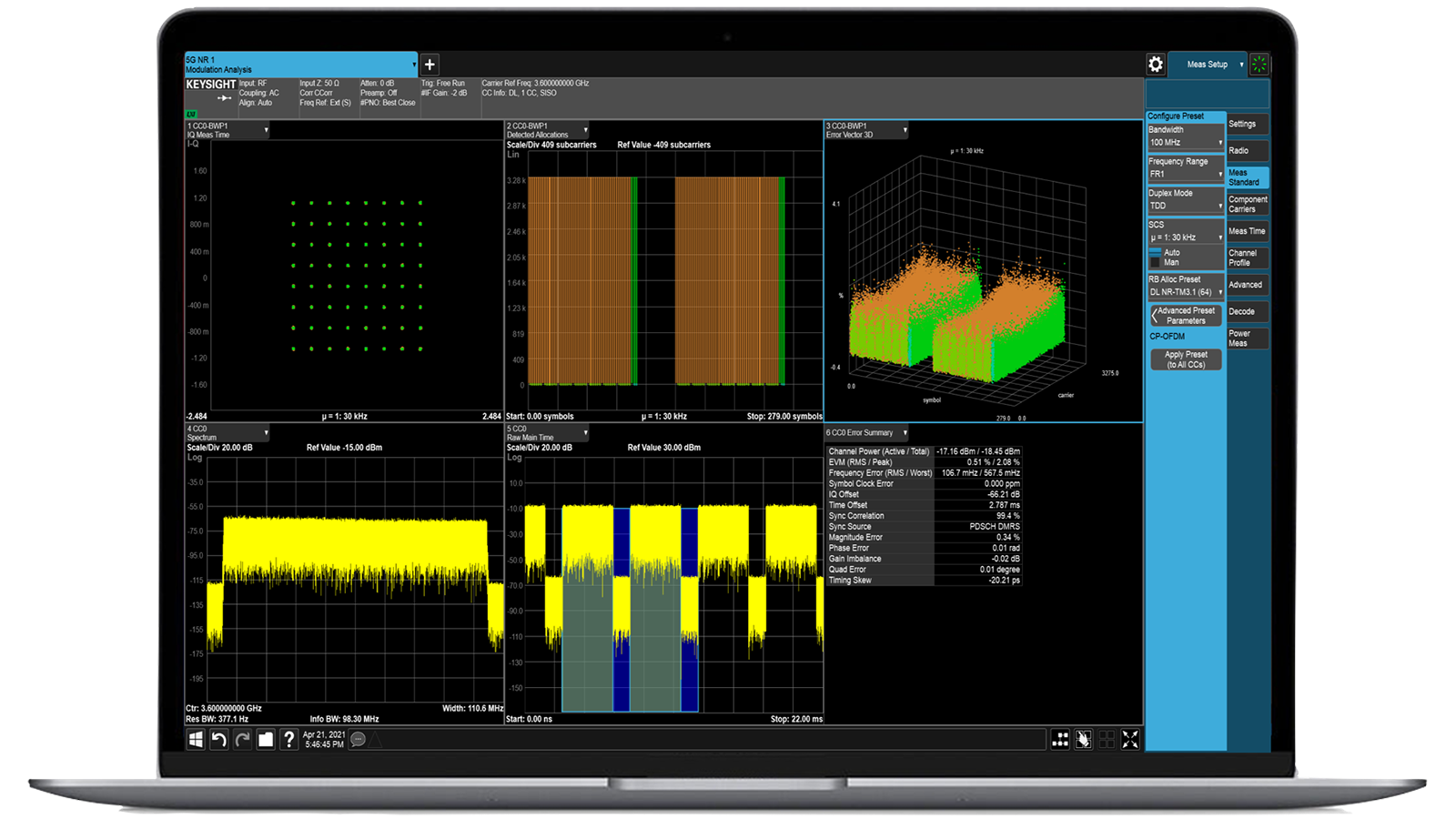
Accelerare l'analisi dei segnali con le applicazioni di misura della serie X
Utilizza oltre 25 applicazioni della serie X per analizzare, demodulare e risolvere i problemi relativi ai segnali nei settori wireless, aerospaziale/difesa, EMI e rumore di fase.

-
Introduzione ai broker di pacchetti potenziati dall'intelligenza artificiale
Grazie alla memoria e allo spazio di archiviazione aggiuntivi, questi NPB potenziati eseguono il software di sicurezza e monitoraggio delle prestazioni AI di Keysight e lo stack AI.

-
Test di precisione in-circuit per la produzione
Ottieni test rapidi e accurati a livello di scheda con un solido ICT in linea e offline progettato per la produzione moderna.

-
Accelerare il motore dell'innovazione
Esplorate i piani di assistenza curati, con priorità per mantenere la velocità dell'innovazione.
-
Generazione di forme d'onda a 448 Gb/s
Raggiungete segnali modulati a più livelli di 200+ Gbaud con AWG ad alta velocità per standard digitali e ottici.

-
Trasmetti dati I/Q a 120 MHz al tuo laptop sul campoIndividuare le interferenze con il software di gestione dello spettro di post-elaborazione in laboratorio.
 Trova la soluzione di alimentazione ATE più adatta alle tue esigenze
Trova la soluzione di alimentazione ATE più adatta alle tue esigenzeUtilizza questo strumento di selezione per individuare rapidamente l'alimentatore più adatto alle tue esigenze in materia di ATE nel settore aerospaziale e della difesa.

-
- Soluzioni
-
Esplorate i contenuti scritti dagli ingegneri e una vasta base di conoscenze con migliaia di opportunità di apprendimento.
In primo pianoKeysight Learn offre contenuti coinvolgenti su argomenti di interesse, tra cui soluzioni, blog, eventi e altro ancora.
Il mio cruscotto di apprendimentoTraccia. Scoprire. Personalizzare.
Tutto in un unico posto. - Acquistare
-
Accesso rapido alle attività di auto-aiuto relative al supporto.
Contenuti aggiuntivi per supportare le vostre esigenze di prodotto.
Fare di più con i servizi KeysightEsplorate i servizi per accelerare ogni fase del vostro percorso di innovazione.
Test di sicurezza IoT Simulazione di minacce IoT reali per una maggiore convalida della sicurezza
- Panoramica
- Tutti i modelli
- Accessori
- Software
- Supporto
Soluzioni robuste per la convalida della sicurezza dei dispositivi connessi
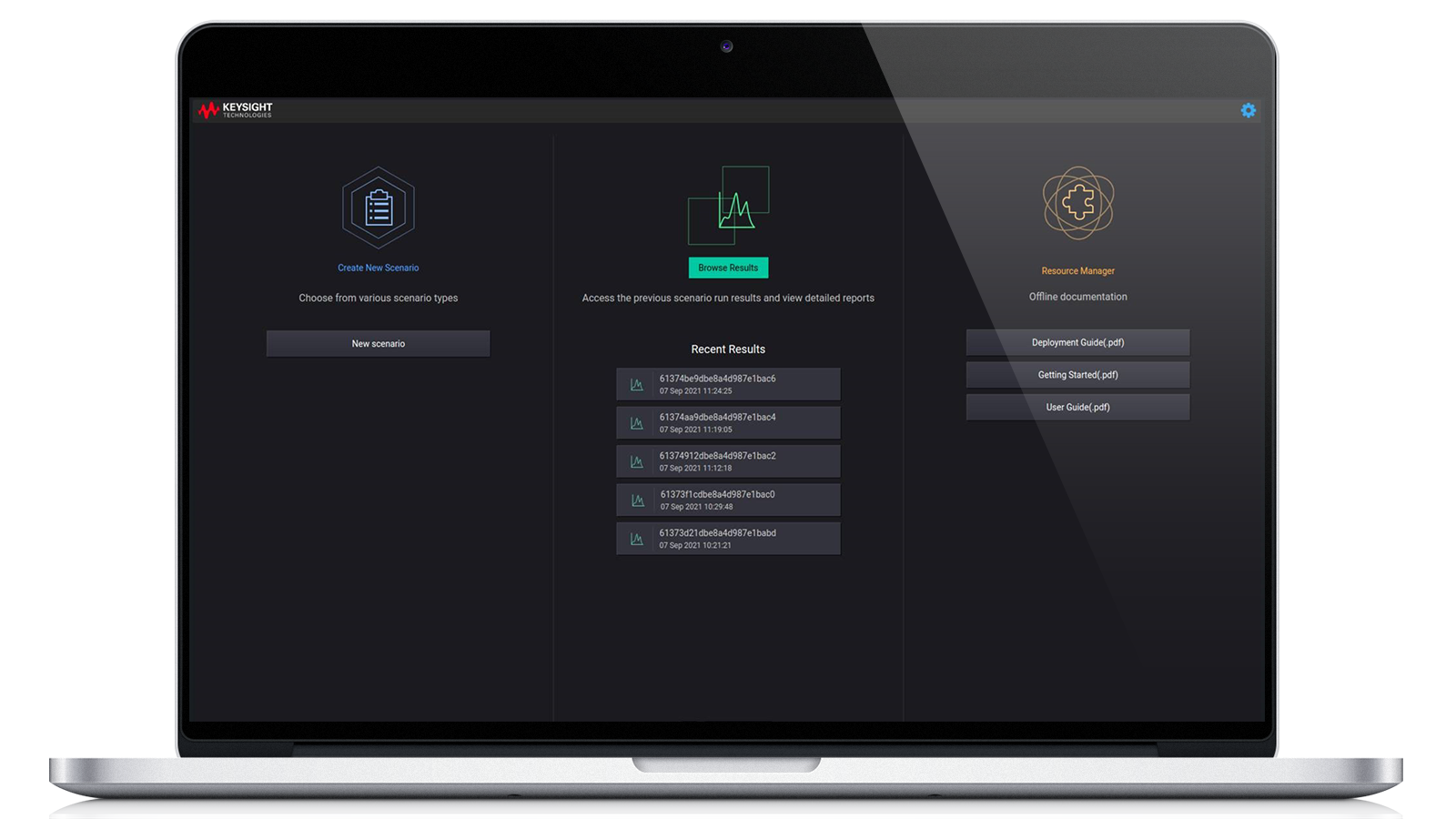
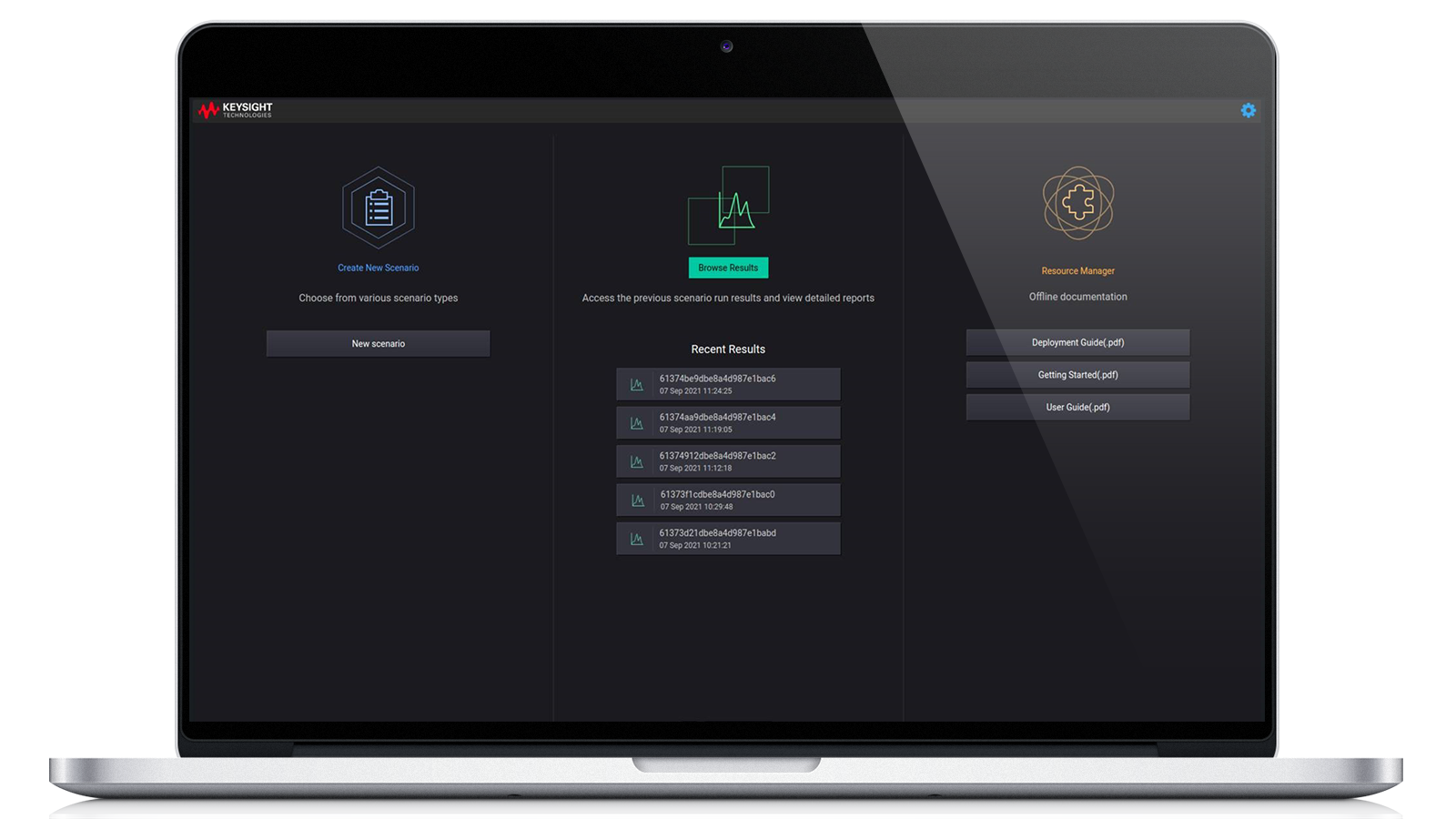
Le soluzioni di test di sicurezza IoT di Keysight combinano automazione intelligente, analisi in tempo reale e copertura delle minacce in continua evoluzione per convalidare la sicurezza dei dispositivi connessi in ogni fase dello sviluppo. Progettate per simulare attacchi informatici reali, consentono di eseguire test altamente affidabili su sistemi integrati, protocolli di comunicazione e sicurezza del firmware per applicazioni IoT consumer e industriali. La piattaforma automatizza la convalida tramite un'interfaccia utente (UI) point-and-click o un'API di automazione. Si tratta di uno strumento chiavi in mano che aiuta a identificare le lacune di sicurezza IoT relative ai requisiti di conformità e di etichettatura. Richiedete oggi stesso un preventivo per una delle nostre configurazioni più popolari. Avete bisogno di aiuto per la scelta? Consultate le risorse riportate di seguito.
Comunicazione sicura
Verifica l'implementazione dei protocolli di crittografia, la gestione dei certificati e i meccanismi di autenticazione. La verifica della sicurezza delle comunicazioni garantisce la riservatezza, l'integrità e l'autenticità dei dati.
Simulazione di minacce
L'emulazione di attacchi reali consente agli sviluppatori di valutare la risposta dei dispositivi IoT ai vettori di minaccia, inclusi attacchi denial-of-service (DoS), spoofing e replay, rafforzando la resilienza dei dispositivi.
Standard e conformità
I casi di test automatizzati sono conformi agli standard di sicurezza chiave, tra cui ETSI EN 303 645, ANSI / CTA 2088-A e OWASP, garantendo l'approvazione normativa e la fiducia dei clienti.
Analisi del comportamento dei dispositivi
Monitora le risposte, le prestazioni e la stabilità dei dispositivi in condizioni di stress e attacco, aiutando gli ingegneri a identificare modelli anomali e a rafforzare la robustezza del sistema.

-
Bundles
Base Controller Software Subscription, IPv4 Attack, WLAN Attack, Bluetooth Attack, IPv6 Attack, Base Controller Software SubscriptionIPv6 AttackIPv4 AttackBluetooth AttackWLAN Attack
-
Type
Software
Configurazioni più popolari
Sicurezza IoT, abbonamento al software del controller di base
Licenza per il modulo di sistema centrale tramite un'interfaccia utente web e API RESTful, che offre un framework per l'automazione, l'integrazione, l'architettura estensibile e la reportistica.
Licenza per il modulo di sistema centrale tramite un'interfaccia utente web e API RESTful, che offre un framework per l'automazione, l'integrazione, l'architettura estensibile e la reportistica.
Sicurezza IoT, abbonamento al software del controller di base
983-1104
Licenza per il modulo di sistema centrale tramite un'interfaccia utente web e API RESTful, che offre un framework per l'automazione, l'integrazione, l'architettura estensibile e la reportistica.
- Fuzzing del protocollo
- Valutazione della vulnerabilità
- Test di conformità
- Baselining comportamentale
La soluzione IoT Security Assessment (IoT SA) di Keysight offre un processo di verifica rapido e semplice per i dispositivi IoT, garantendo la conformità agli standard e risolvendo le vulnerabilità più comuni. Utilizza un fuzzer di protocollo brevettato per fornire una valutazione completa. IoT SA esegue test su vari protocolli, tra cui TCP/IP, Bluetooth® Classic, Bluetooth® Low Energy (BLE), CAN e reti mobili O-RAN tramite IP. Il software riceve aggiornamenti mensili che incorporano nuovi audit e funzionalità per valutare le vulnerabilità attuali. La natura modulare degli aggiornamenti consente di aggiornare separatamente il sistema centrale e i moduli aggiuntivi.
Sicurezza IoT, modulo di attacco Bluetooth® con aggiornamenti ATI
Licenza aggiuntiva opzionale per 983-1104 per attivare il modulo per le valutazioni di sicurezza Bluetooth®.
Licenza aggiuntiva opzionale per 983-1104 per attivare il modulo per le valutazioni di sicurezza Bluetooth®.
Sicurezza IoT, modulo di attacco Bluetooth® con aggiornamenti ATI
983-1107
Licenza aggiuntiva opzionale per 983-1104 per attivare il modulo per le valutazioni di sicurezza Bluetooth®.
- Potenzia gli strumenti basati su WLAN per la valutazione della sicurezza tramite Bluetooth®.
- Incorpora nuovi strumenti sviluppati attraverso la ricerca sulla sicurezza ATI di Keysight negli aggiornamenti basati su abbonamento.
- Fornisce strumenti per il fuzzing dello stack radio, l'individuazione di sistemi/servizi, la gestione delle vulnerabilità e la valutazione delle debolezze note.
- Facilita l'individuazione di nuovi punti deboli o vulnerabilità.
- Richiede una licenza IoT Security Base Controller (983-1104).
La soluzione IoT Security Assessment (IoT SA) di Keysight offre un processo di verifica rapido e semplice per i dispositivi IoT, garantendo la conformità agli standard e risolvendo le vulnerabilità più comuni. Utilizza un fuzzer di protocollo brevettato per fornire una valutazione completa. Il software riceve aggiornamenti mensili che incorporano nuovi audit e funzionalità per valutare le vulnerabilità attuali. La natura modulare degli aggiornamenti consente di aggiornare separatamente il sistema centrale e i moduli aggiuntivi.
Pacchetto sicurezza IoT con aggiornamenti ATI
Pacchetto di valutazione della sicurezza IoT che include licenza controller principale: 983-1104, modulo IPv4: 983-1105, modulo WLAN: 983-1106 e modulo Bluetooth®: 983-1107.
Pacchetto di valutazione della sicurezza IoT che include licenza controller principale: 983-1104, modulo IPv4: 983-1105, modulo WLAN: 983-1106 e modulo Bluetooth®: 983-1107.
Pacchetto sicurezza IoT con aggiornamenti ATI
983-1110
Pacchetto di valutazione della sicurezza IoT che include licenza controller principale: 983-1104, modulo IPv4: 983-1105, modulo WLAN: 983-1106 e modulo Bluetooth®: 983-1107.
- Include controller di base per la sicurezza IoT (983-1104)
- Include modulo di attacco IoT IPv4 (983-1105)
- Include modulo di attacco WLAN IoT (983-1106)
- Include modulo di attacco Bluetooth IoT (983-1107)
- Incorpora nuovi strumenti sviluppati attraverso la ricerca sulla sicurezza ATI di Keysight negli aggiornamenti basati su abbonamento.
La soluzione IoT Security Assessment (IoT SA) di Keysight offre un processo di verifica rapido e semplice per i dispositivi IoT, garantendo la conformità agli standard e risolvendo le vulnerabilità più comuni. Utilizza un fuzzer di protocollo brevettato per fornire una valutazione completa. Il software riceve aggiornamenti mensili che incorporano nuovi audit e funzionalità per valutare le vulnerabilità attuali. La natura modulare degli aggiornamenti consente di aggiornare separatamente il sistema centrale e i moduli aggiuntivi.
Servizi e assistenza
Innova rapidamente grazie a piani di assistenza personalizzati e tempi di risposta e risoluzione prioritari.
Ottieni abbonamenti prevedibili basati su leasing e soluzioni complete per la gestione dell'intero ciclo di vita, in modo da raggiungere più rapidamente i tuoi obiettivi aziendali.
Beneficia di un servizio di alto livello come abbonato KeysightCare per ottenere assistenza tecnica dedicata e molto altro ancora.
Assicurati che il tuo sistema di test funzioni secondo le specifiche e soddisfi gli standard locali e globali.
Effettua misurazioni rapidamente grazie alla formazione interna con istruttore e all'e-learning.
Scarica il software Keysight o aggiorna il tuo software alla versione più recente.
Domande frequenti
Una valutazione della sicurezza IoT è un'analisi multistrato dello stato di sicurezza di un dispositivo connesso, che copre hardware, software, firmware e protocolli di comunicazione. In genere inizia con la modellazione delle minacce per capire quali risorse necessitano di protezione e quali potrebbero essere gli obiettivi potenziali degli aggressori. Da lì, la valutazione passa a test pratici, iniziando dalle interfacce fisiche del dispositivo come porte UART, JTAG o USB, che vengono controllate per verificare la presenza di accessi di debug, fughe di dati o controlli non autorizzati. L'analisi del firmware è una componente importante, che comporta l'estrazione e il reverse engineering dell'immagine binaria per identificare segreti incorporati, configurazioni non sicure o componenti vulnerabili.
La comunicazione di rete viene esaminata attentamente per determinare se la crittografia è implementata correttamente e se i protocolli sono suscettibili ad attacchi di replay, spoofing o iniezione. Se il dispositivo comunica tramite API cloud o app mobili, anche questi componenti vengono analizzati per individuare eventuali problemi quali autenticazione inadeguata, gestione non sicura dei token o endpoint esposti. La valutazione include spesso il fuzzing dei protocolli per testare la robustezza degli stack di comunicazione inviando pacchetti malformati o imprevisti. Infine, il dispositivo viene confrontato con framework di sicurezza noti come ETSI EN 303 645 o NIST 8259 per identificare eventuali lacune di conformità. Gli strumenti utilizzati durante questo processo possono includere analizzatori di codice statico, debugger, proxy di intercettazione, sniffer RF e kit di exploit hardware.
I test a livello di protocollo sono fondamentali per i dispositivi IoT perché utilizzano spesso protocolli di comunicazione leggeri o proprietari che sono più vulnerabili alle falle di sicurezza rispetto agli standard maturi come HTTPS. A differenza delle infrastrutture IT generali, dove i protocolli sono stati rafforzati nel corso di decenni, gli ecosistemi IoT si basano su stack come CoAP, MQTT, Zigbee, BLE o protocolli seriali personalizzati che sono spesso scarsamente documentati o implementati in modo incoerente. Di conseguenza, molti dispositivi elaborano dati malformati o imprevisti in modo non sicuro, causando crash, overflow del buffer o comportamenti indesiderati. I test a livello di protocollo comportano sia il monitoraggio passivo che l'iniezione attiva di pacchetti malformati, fuori sequenza o dannosi per osservare come reagisce il dispositivo.
Ciò è particolarmente importante in ambienti in cui i dispositivi prendono decisioni autonome sulla base di comandi di rete, ad esempio serrature intelligenti, sensori o apparecchiature mediche. Senza un adeguato controllo dei limiti o un'autenticazione, tali dispositivi potrebbero accettare comandi contraffatti o diventare instabili. Inoltre, molti stack IoT presuppongono ambienti affidabili e non applicano standard crittografici rigorosi, lasciandoli esposti a furti di sessione o attacchi di replay. Eseguendo test di fuzzing e interazione sensibili al protocollo, gli ingegneri possono scoprire queste vulnerabilità sottili ma critiche che spesso sfuggono alle revisioni statiche del codice o ai test di penetrazione generici.
I test di sicurezza IoT dovrebbero essere un processo continuo integrato in ogni fase del ciclo di vita del dispositivo, non solo una convalida una tantum prima del lancio del prodotto. Nella fase di progettazione, è fondamentale condurre una modellazione delle minacce e stabilire i requisiti di sicurezza sin dalle prime fasi, quando le decisioni architetturali hanno la maggiore influenza sulla sicurezza a lungo termine. Durante lo sviluppo, le attività di test dovrebbero concentrarsi sull'identificazione delle vulnerabilità a livello di codice, sulla verifica della sicurezza delle librerie di terze parti e sull'esecuzione di analisi statiche e dinamiche nella fase iniziale. Prima del rilascio, è essenziale effettuare una valutazione completa, che includa la convalida del firmware, l'analisi del protocollo di comunicazione, il test dell'interfaccia hardware e la valutazione della sicurezza del backend, per garantire che il dispositivo sia protetto dalle minacce conosciute.
Tuttavia, i test di sicurezza devono continuare anche dopo l'immissione sul mercato del dispositivo. Le valutazioni post-implementazione sono fondamentali, soprattutto quando vengono rilasciati aggiornamenti del firmware, vengono integrate nuove funzionalità o vengono scoperte nuove vulnerabilità che interessano lo stack software o i servizi esterni. Data la lunga durata operativa e gli ambienti di implementazione spesso incustoditi dei dispositivi IoT, questi ultimi sono costantemente esposti a minacce informatiche in continua evoluzione. Rivalutazioni periodiche, idealmente condotte ogni anno o dopo ogni cambiamento significativo, aiutano a mantenere la conformità agli standard di sicurezza del settore e proteggono il dispositivo dai rischi emergenti. Il rafforzamento della sicurezza attraverso il monitoraggio continuo, l'automazione dei test remoti e framework di aggiornamento over-the-air (OTA) sicuri garantisce la resilienza a lungo termine durante l'intero ciclo di vita del dispositivo.