Choose a country or area to see content specific to your location
Können wir Ihnen behilflich sein?
-
-
3D Interconnect Designer
3D Interconnect Designer bietet eine flexible Modellierungs- und Optimierungsumgebung für jede Art von fortschrittlicher Verbindungsstruktur, einschließlich Chiplets, gestapelten Chips, Gehäusen und Leiterplatten.

-
Sparen Sie bis zu 50 % beim Kauf eines XR8-Oszilloskops
Profitieren Sie von einer schnelleren digitalen Fahrzeugvalidierung zu geringeren Kosten mit einer Inzahlungnahme.

-
Entdecken Sie den Keysight AI Data Center Builder
Simulieren Sie jeden Teil Ihrer Rechenzentrumsinfrastruktur. Simulieren Sie alles. Optimieren Sie alles.

-
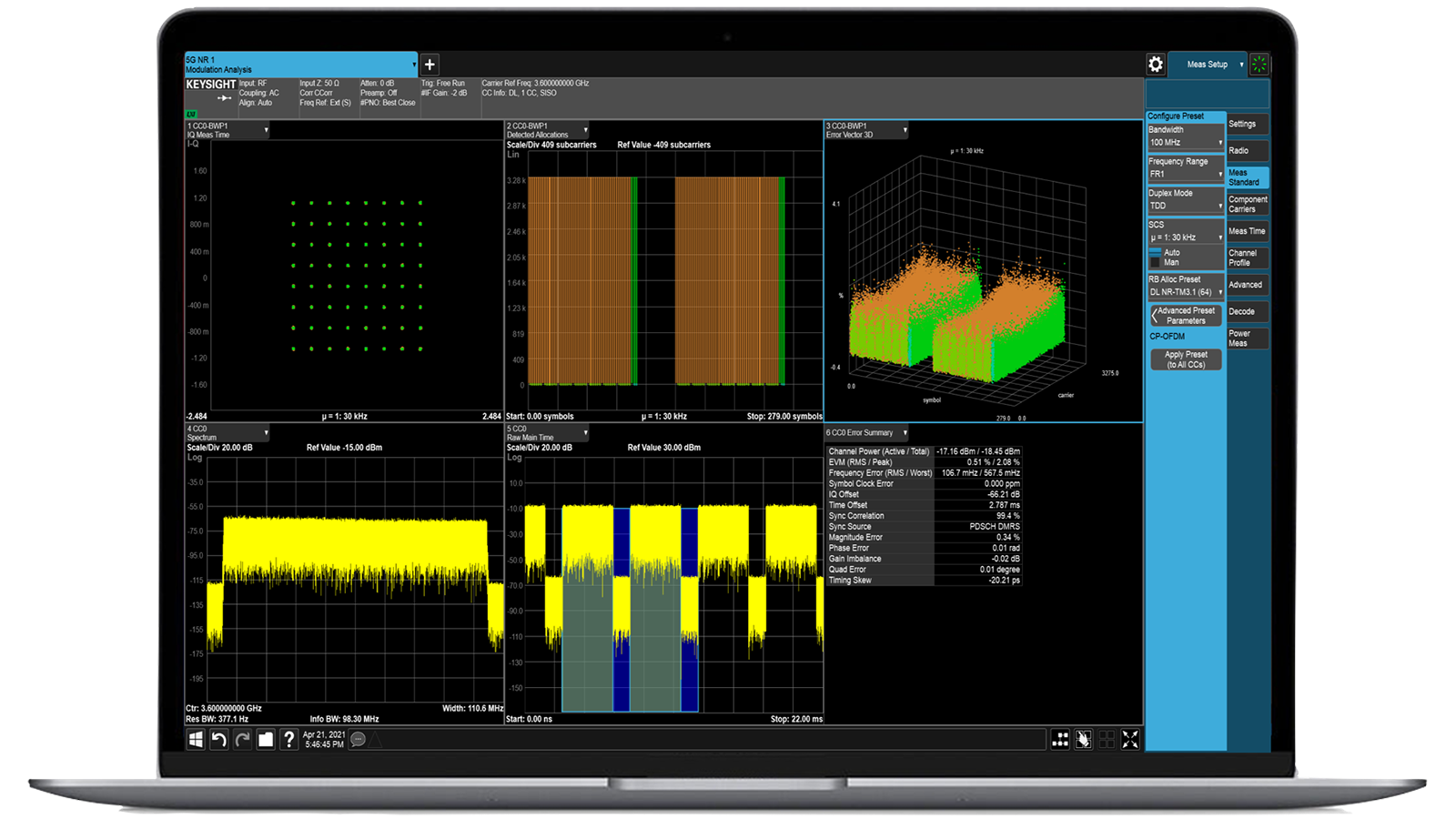
Beschleunigen Sie die Signalanalyse mit den Messanwendungen der X-Serie.
Nutzen Sie mehr als 25 Anwendungen der X-Serie zur Analyse, Demodulation und Fehlerbehebung von Signalen in den Bereichen drahtlose Kommunikation, Luft- und Raumfahrt/Verteidigung, elektromagnetische Störungen und Phasenrauschen.

-
Einführung KI-gestützter Paketbroker
Mit zusätzlichem Speicher und Speicherplatz können diese verbesserten NPBs die KI-Sicherheits- und Leistungsüberwachungssoftware sowie den KI-Stack von Keysight ausführen.

-
Präzisionsprüfung im laufenden Betrieb für die Produktion
Erreichen Sie schnelle und präzise Tests auf Platinenebene mit robusten Inline- und Offline-ICT-Systemen, die für die moderne Fertigung entwickelt wurden.

-
Beschleunigen Sie Ihren Innovationsmotor
Informieren Sie sich über kuratierte Support-Pläne, die nach Prioritäten geordnet sind, um Ihre Innovationsgeschwindigkeit aufrechtzuerhalten.
-
-
Streamen Sie 120-MHz-I/Q-Daten direkt im Feld auf Ihren Laptop.Punktgenaue Störungen mit der Nachbearbeitungssoftware für das Spektrummanagement im Labor.
 Finden Sie die passende ATE-Stromversorgungslösung
Finden Sie die passende ATE-StromversorgungslösungMit diesem Auswahltool können Sie schnell das beste Netzteil für Ihre ATE-Anforderungen im Bereich Luft- und Raumfahrt sowie Verteidigung ermitteln.

-
- Lösungen
-
Entdecken Sie von Ingenieuren verfasste Inhalte und eine umfangreiche Wissensdatenbank mit Tausenden von Lernmöglichkeiten.
AusgewähltKeysight Learn bietet umfassende Inhalte zu interessanten Themen, darunter Lösungen, Blogs, Veranstaltungen und mehr.
Mein Lern-DashboardVerfolgen. Entdecken. Personalisieren.
Alles an einem Ort. -
Schneller Zugriff auf die häufigsten unterstützungsbezogenen Selbsthilfeaufgaben.
Zusätzliche Inhalte zur Unterstützung Ihrer Produktanforderungen.
Mehr erreichen mit Keysight ServicesEntdecken Sie Dienstleistungen, die jeden Schritt Ihrer Innovationsreise beschleunigen.
Bedrohungssimulator: Automatisierte BAS-Plattform zur kontinuierlichen Sicherheitsvalidierung

- Überblick
- Alle Modelle
- Unterstützung
Nachbildung des Angreiferverhaltens über Endpunkt-, Netzwerk- und Cloud-Schichten hinweg
Die Keysight Threat Simulator Software bietet kontinuierliche Breach and Attack Simulation (BAS), um die Wirksamkeit Ihrer bestehenden Cybersicherheitskontrollen zu validieren. Durch die Replikation realer Angreiferverhaltensweisen über Endpunkt-, Netzwerk- und Cloud-Ebenen hinweg hilft sie Ihnen, Schwachstellen proaktiv aufzudecken und das Risiko zu reduzieren. Threat Simulator arbeitet sicher in Produktionsumgebungen und liefert umsetzbare Erkenntnisse zur Behebung, die auf Frameworks wie MITRE ATT&CK abgestimmt sind. Fordern Sie noch heute ein Angebot für eine unserer beliebten Konfigurationen an. Benötigen Sie Hilfe bei der Auswahl? Sehen Sie sich die untenstehenden Ressourcen an.
TTP-basierte Simulations-Engine
Simulieren Sie die Taktiken, Techniken und Vorgehensweisen (TTPs) von Angreifern mithilfe von Szenarien, die auf Frameworks wie MITRE ATT&CK abgestimmt sind.
Validierung des gesamten Sicherheits-Stacks
Testen Sie Erkennung und Reaktion über Endpunkt-, Netzwerk- und Cloud-Sicherheitskontrollen hinweg mit einheitlicher Transparenz.
Leitlinien und Berichterstattung zur Behebung von Mängeln
Erhalten Sie priorisierte Empfehlungen und Risikokennzahlen, die Ihrem Team helfen, Sicherheitslücken zu schließen, bevor Angreifer sie ausnutzen.
SIEM- und SOAR-Integration
Automatisieren Sie die Testorchestrierung und Ergebnisanalyse durch die direkte Integration in Ihre bestehenden Sicherheitsbetriebsplattformen.
Beliebteste Konfigurationen

Threat Simulator Basispaket, 5 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
Threat Simulator Basispaket, 5 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
983-2010
Keysight Threat Simulator beinhaltet das Basispaket mit fünf Agenten und ein einjähriges SaaS-Abonnement.
- Validieren Sie alle Phasen des Angriffslebenszyklus.
- Verkürzen Sie die Zeit für Compliance-Audits durch datengestützte Nachweise.
- Weisen Sie nach, dass Sie Sicherheitsangriffe ordnungsgemäß identifiziert und gemeldet haben.
- Begründen Sie die aktuellen und zukünftigen IT-Ausgaben.
- Aktualisieren Sie die Inhalte in regelmäßigen Abständen, einschließlich der Bereitstellung täglicher Malware-Updates.

Threat Simulator Basic Bundle, 10 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
Threat Simulator Basic Bundle, 10 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
983-2011
Keysight Threat Simulator beinhaltet das Basispaket für 10 Agenten und ein einjähriges SaaS-Abonnement.
- Validieren Sie alle Phasen des Angriffslebenszyklus.
- Verkürzen Sie die Zeit für Compliance-Audits durch datengestützte Nachweise.
- Weisen Sie nach, dass Sie Sicherheitsangriffe ordnungsgemäß identifiziert und gemeldet haben.
- Begründen Sie die aktuellen und zukünftigen IT-Ausgaben.
- Aktualisieren Sie die Inhalte in regelmäßigen Abständen, einschließlich der Bereitstellung täglicher Malware-Updates.

Threat Simulator Standard Bundle, 25 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
Threat Simulator Standard Bundle, 25 Agenten, 1-Jahres-SaaS-Abonnement (TAA)
983-2012
Keysight Threat Simulator beinhaltet das Standardpaket für 25 Agenten und ein einjähriges SaaS-Abonnement.
- Validieren Sie alle Phasen des Angriffslebenszyklus.
- Verkürzen Sie die Zeit für Compliance-Audits durch datengestützte Nachweise.
- Weisen Sie nach, dass Sie Sicherheitsangriffe ordnungsgemäß identifiziert und gemeldet haben.
- Begründen Sie die aktuellen und zukünftigen IT-Ausgaben.
- Aktualisieren Sie die Inhalte in regelmäßigen Abständen, einschließlich der Bereitstellung täglicher Malware-Updates.
Dienstleistungen und Support
Innovieren Sie im Handumdrehen mit maßgeschneiderten Supportplänen und priorisierten Reaktions- und Bearbeitungszeiten.
Profitieren Sie von planbaren, leasingbasierten Abonnements und umfassenden Lifecycle-Management-Lösungen – damit Sie Ihre Geschäftsziele schneller erreichen.
Als KeysightCare-Abonnent profitieren Sie von einem erweiterten Service mit zuverlässiger technischer Unterstützung und vielem mehr.
Stellen Sie sicher, dass Ihr Testsystem den Spezifikationen entspricht und sowohl lokale als auch globale Standards erfüllt.
Schnelle Messungen dank hauseigener, von Ausbildern geleiteter Schulungen und E-Learning.
Laden Sie die Keysight-Software herunter oder aktualisieren Sie Ihre Software auf die neueste Version.
Häufig gestellte Fragen
Die Simulation von Sicherheitsvorfällen und Angriffen dient der kontinuierlichen Überprüfung und Validierung der Wirksamkeit von Sicherheitsmaßnahmen. Dies geschieht durch die sichere Nachbildung realen Angreiferverhaltens in einer kontrollierten Umgebung. Anstatt auf einen tatsächlichen Sicherheitsvorfall zu warten, der Schwachstellen aufdeckt, können Unternehmen proaktiv dieselben Taktiken, Techniken und Vorgehensweisen simulieren, die Angreifer nutzen – von Zugangsdatendiebstahl und lateraler Bewegung bis hin zu Phishing und Datenexfiltration. Diese Simulationen sind keine theoretischen oder statischen Checklisten; sie spiegeln die sich ständig weiterentwickelnden Strategien von Cyberkriminellen wider und werden laufend aktualisiert, um die neuesten Erkenntnisse über Bedrohungen zu berücksichtigen.
Dieser Ansatz ist für moderne Sicherheitsteams unerlässlich, da die heutigen IT-Umgebungen über lokale Rechenzentren, öffentliche und private Clouds sowie Remote-Endpunkte verteilt sind. Traditionelle, punktuelle Penetrationstests oder Red-Teaming-Übungen liefern zwar wertvolle Erkenntnisse, sind aber oft in Umfang und Häufigkeit begrenzt. Die Simulation von Sicherheitsvorfällen und Angriffen hingegen ermöglicht eine kontinuierliche Validierung und stellt sicher, dass die Abwehrmaßnahmen auch bei sich ändernden Netzwerken, Anwendungen und Bedrohungslandschaften wirksam bleiben.
Die Vorteile gehen weit über das bloße Aufdecken von Sicherheitslücken hinaus. Sicherheitsteams erhalten messbare und reproduzierbare Belege für die Wirksamkeit ihrer Abwehrmaßnahmen gegen spezifische Angriffsvektoren. Sie können die Behebung von Schwachstellen anhand des Geschäftsrisikos priorisieren, ihre Reaktionsfähigkeit bei Sicherheitsvorfällen verbessern und die Einhaltung regulatorischer oder branchenspezifischer Standards nachweisen. Vor allem aber ermöglicht diese proaktive Strategie Unternehmen, von einer reaktiven Haltung – bei der erst nach einem Sicherheitsvorfall reagiert wird – zu einer präventiven Haltung überzugehen, bei der Schwachstellen identifiziert und behoben werden, bevor sie ausgenutzt werden können.
Die Überprüfung der Endpunkterkennung umfasst die Simulation realer Angriffstechniken direkt auf oder in der Nähe des Endgeräts, ohne Schaden oder Systemunterbrechungen zu verursachen. BAS-Tools wie Threat Simulator installieren einen sicheren Testagenten, der kontrollierte Angriffsskripte ausführt. Diese Skripte ahmen gängige Techniken wie das Abgreifen von Anmeldeinformationen, das Einschleusen in Prozesse oder die Ausführung dateiloser Malware nach. Die Simulationen nutzen bekannte Techniken von Angreifergruppen (z. B. APTs) und stellen so sicher, dass sie die tatsächlichen Bedrohungen widerspiegeln, denen Ihr Unternehmen ausgesetzt sein könnte.
Sobald eine Simulation ausgeführt wurde, erfasst der Threat Simulator Telemetriedaten vom Agenten und prüft, ob Ihr EDR/XDR-, Antiviren- oder SIEM-System das Ereignis protokolliert, blockiert oder Warnungen ausgelöst hat. Sie erhalten eine detaillierte Aufschlüsselung der erkannten und übersehenen Ereignisse sowie der bestehenden Sicherheitslücken. Dies ermöglicht gezielte Verbesserungen der Erkennungsregeln, Protokollierungskonfigurationen oder Agentenbereitstellungen. Dadurch wird die Endpunktsicherheit von einer Blackbox zu einer messbaren und anpassbaren Verteidigungsebene.
Eine korrekte Netzwerksegmentierung ist entscheidend, um die laterale Ausbreitung von Bedrohungen einzudämmen. Fehlkonfigurationen sind jedoch häufig und bleiben oft unbemerkt. Mit einer BAS-Plattform können Sie die Durchsetzung der Segmentierung überprüfen, indem Sie Angriffspfade innerhalb des Netzwerks simulieren. Beispielsweise können Agenten in verschiedenen VLANs, Subnetzen oder Cloud-VPCs eingesetzt werden, um Portscans, laterale Bewegungen oder Zugriffsversuche mittels Anmeldeinformationen zu simulieren.
Der Bedrohungssimulator simuliert das Verhalten von Angreifern beim Versuch, Netzwerksegmente zu durchdringen, und testet Firewall-Regeln, NAC-Richtlinien und Routing-ACLs. Anschließend meldet er, ob der Zugriffsversuch blockiert oder zugelassen wurde und ob ein Überwachungssystem das Verhalten gemeldet hat. Techniker können in Echtzeit sehen, ob die Segmentierungskontrollen ihren Anforderungen entsprechen und die Richtlinien entsprechend anpassen. Dies ist besonders in komplexen Umgebungen wie Hybrid-Cloud, SD-WAN oder mikrosegmentierten Rechenzentren hilfreich, wo eine manuelle Validierung nahezu unmöglich ist.
Ja, BAS-Plattformen eignen sich hervorragend zur Validierung der praktischen Wirksamkeit Ihrer SOC-Alarmierungs- und Triage-Systeme. Der Threat Simulator kann simulierte Angriffssequenzen auslösen, die theoretisch von Ihrem SIEM, IDS/IPS, Ihrer Firewall und anderen Kontrollmechanismen erkannt werden sollten. Beispielsweise kann er Command-and-Control-Beaconing, laterale Bewegungsversuche oder Privilegienmissbrauch simulieren – allesamt Angriffe, die Ihre Erkennungslogik erfassen sollte.
Nach Abschluss dieser Simulationen kann Ihr SOC-Team überprüfen, ob die entsprechenden Warnmeldungen generiert, korrekt eskaliert und wie schnell die Reaktion auf Sicherheitsvorfälle eingeleitet wurde. Dies testet nicht nur die Tools, sondern auch die Personen und Prozesse hinter Ihrer Erkennungsstrategie. Durch die regelmäßige Durchführung dieser Simulationen schaffen Sie einen Feedback-Kreislauf, der die Erkennungsregeln optimiert, die Warnmeldungsflut reduziert (durch die Optimierung von Fehlalarmen) und die Reaktionszeiten des SOC verbessert – und gleichzeitig die Abdeckung kritischer Angriffstechniken nachweist.
Herkömmliche Penetrationstests sind typischerweise manuell, punktuell und auf einen bestimmten Umfang beschränkt. Sie werden ein- bis zweimal jährlich durchgeführt und konzentrieren sich oft auf das Aufdecken von Schwachstellen anstatt auf die Validierung bestehender Abwehrmechanismen. Obwohl sie wertvoll sind, können sie nicht die kontinuierliche Sicherheit bieten, die erforderlich ist, um mit der sich schnell verändernden Bedrohungslandschaft von heute Schritt zu halten. Breach- und Attack-Simulationen hingegen sind automatisiert, wiederholbar und sicher für Produktionsumgebungen.
Der Bedrohungssimulator kann täglich, wöchentlich oder bedarfsgesteuert über verschiedene Vektoren – Endpunkte, Netzwerk, Cloud – ausgeführt werden. Er simuliert reale Bedrohungen und überprüft, ob Ihre Sicherheitsarchitektur wie vorgesehen reagiert. Im Gegensatz zu Penetrationstestern, die aus Zeitgründen oft nur wenige Angriffspfade testen, kann ein BAS-Tool Hunderte von Angriffsvarianten ausführen, bekannte Angreifertechniken (z. B. APT29, FIN7) simulieren und konsistente, vergleichende Berichte erstellen. So können Unternehmen von reaktiven, sporadischen Tests zu einer kontinuierlichen, datengestützten Validierung übergehen, deren Ergebnisse direkt in den SOC-Betrieb und die Risikomanagement-Workflows einfließen.