Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
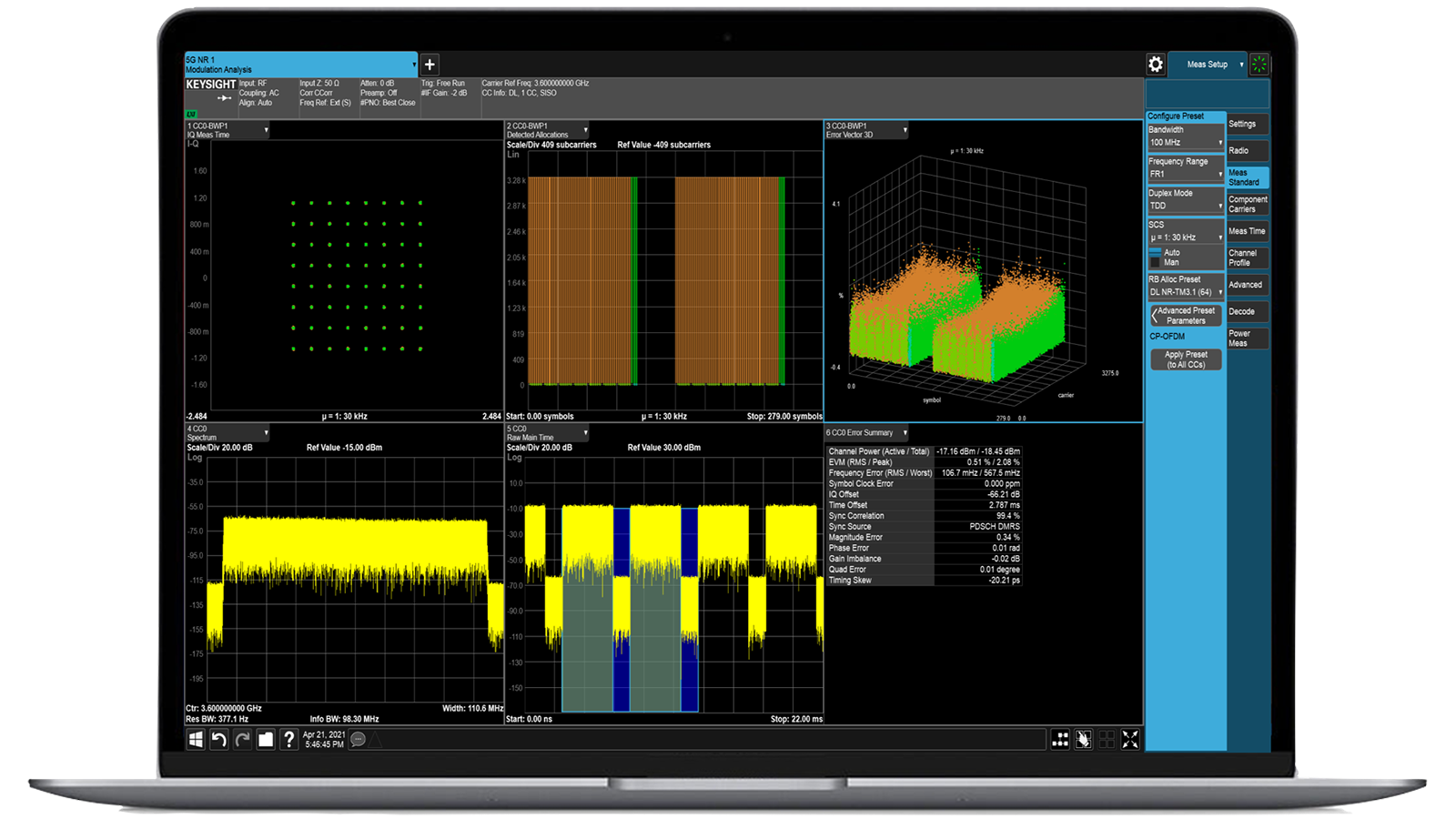
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
Threat Simulator Automated BAS platform for continuous security validation

- Overview
- All Models
- Support
Replicate adversary behaviors across endpoint, network, and cloud layers
Keysight Threat Simulator software provides continuous breach and attack simulation (BAS) to validate the effectiveness of your existing cybersecurity controls. By replicating real adversary behaviors across endpoint, network, and cloud layers, it helps you proactively uncover weaknesses and reduce risk exposure. Threat Simulator operates safely in production environments and delivers actionable remediation insights mapped to frameworks like MITRE ATT&CK. Request a quote for one of our popular configurations today. Need help selecting? Check out the resources below.
TTP-based simulation engine
Emulate attacker tactics, techniques, and procedures (TTPs) using scenarios aligned with frameworks like MITRE ATT&CK.
End-to-end security stack validation
Test detection and response across endpoint, network, and cloud security controls with unified visibility.
Remediation guidance and reporting
Receive prioritized recommendations and risk metrics to help your team close gaps before attackers exploit them.
SIEM and SOAR integration
Automate test orchestration and results analysis by integrating directly with your existing security operations platforms.
Most popular configurations

Threat Simulator Base Bundle, 5 Agents, 1-Year SaaS Subscription TAA
Threat Simulator Base Bundle, 5 Agents, 1-Year SaaS Subscription TAA
983-2010
Keysight Threat Simulator includes the base bundle containing five agents and a one-year SaaS subscription.
- Validate all phases of the attack life cycle.
- Reduce compliance audit time with data-driven evidence.
- Prove that you have properly identified and reported security attacks.
- Justify current and future IT spending.
- Refresh the content at regular intervals, including the provision of everyday malware feeds.

Threat Simulator Basic Bundle, 10 Agents, 1-Year SaaS Subscription TAA
Threat Simulator Basic Bundle, 10 Agents, 1-Year SaaS Subscription TAA
983-2011
Keysight Threat Simulator includes the basic bundle for 10 agents and a one-year SaaS subscription.
- Validate all phases of the attack life cycle.
- Reduce compliance audit time with data-driven evidence.
- Prove that you have properly identified and reported security attacks.
- Justify current and future IT spending.
- Refresh the content at regular intervals, including the provision of everyday malware feeds.

Threat Simulator Standard Bundle, 25 Agents, 1-Year SaaS Subscription TAA
Threat Simulator Standard Bundle, 25 Agents, 1-Year SaaS Subscription TAA
983-2012
Keysight Threat Simulator includes the standard bundle for 25 agents and a one-year SaaS subscription.
- Validate all phases of the attack life cycle.
- Reduce compliance audit time with data-driven evidence.
- Prove that you have properly identified and reported security attacks.
- Justify current and future IT spending.
- Refresh the content at regular intervals, including the provision of everyday malware feeds.
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
Breach and attack simulation is the practice of continuously testing and validating the effectiveness of security defenses by safely emulating real-world attacker behavior in a controlled environment. Instead of waiting for an actual breach to reveal weaknesses, organizations can proactively simulate the same tactics, techniques, and procedures that malicious actors use, ranging from credential theft and lateral movement to phishing and data exfiltration. These simulations are not theoretical or static checklists; they mirror the constantly evolving strategies of cyber adversaries and are updated to reflect the latest threat intelligence.
This approach is critical for modern security teams because today’s IT environments are distributed across on-premises data centers, public and private clouds, and remote endpoints. Traditional, point-in-time penetration testing or red teaming exercises may provide valuable insights, but they are often limited in scope and frequency. Breach and attack simulation, by contrast, offers ongoing validation, ensuring that defenses are effective even as networks, applications, and threat landscapes change.
The benefits go beyond simply finding gaps. Security teams gain measurable, repeatable evidence of how their defenses perform against specific attack vectors. They can prioritize remediation based on business risk, improve incident response readiness, and demonstrate compliance with regulatory or industry standards. Most importantly, this proactive strategy enables organizations to shift from a reactive posture, responding only after a breach occurs, to a preventive one, where weaknesses are identified and addressed before they can be exploited.
Verifying endpoint detection involves simulating real-world adversarial techniques directly on or near the endpoint device without causing harm or system disruption. BAS tools like Threat Simulator install a secure test agent that runs controlled attack scripts mimicking common techniques such as credential harvesting, process injection, or fileless malware execution. These simulations use known techniques from adversary groups (e.g., APTs), ensuring they reflect actual threats your organization might face.
Once a simulation is run, Threat Simulator collects telemetry from the agent and checks whether your EDR/XDR, antivirus, or SIEM recorded the event, blocked it, or raised alerts. You get a detailed breakdown of what was detected, what was missed, and where the gaps are, enabling targeted improvements in detection rules, logging configurations, or agent deployments. This turns endpoint security from a black box into a measurable, tunable defense layer.
Proper network segmentation is critical for limiting the lateral spread of threats, but misconfigurations are common and often go unnoticed. With a BAS platform, you can validate segmentation enforcement by simulating intra-network attack paths. For example, agents can be deployed on different VLANs, subnetworks, or cloud VPCs to simulate port scans, lateral movement, or credential-based access attempts.
Threat Simulator mimics the behavior of attackers trying to traverse segments, testing firewall rules, NAC policies, and routing ACLs. It then reports on whether the access attempt was blocked or allowed, and whether any monitoring system flagged the behavior. Engineers can see in real time if the segmentation controls match their intent, and adjust policies accordingly. This is especially useful in complex environments like hybrid cloud, SD-WAN, or microsegmented data centers, where manual validation is nearly impossible.
Yes, BAS platforms are highly effective for validating the real-world efficacy of your SOC’s alerting and triage systems. Threat Simulator can trigger emulated attack sequences that should, in theory, be detected by your SIEM, IDS/IPS, firewall, and other controls. For example, it may simulate command-and-control beaconing, lateral movement attempts, or privilege abuse, all of which your detection logic is expected to catch.
Once these simulations run, your SOC team can review whether the appropriate alerts were generated, if they were escalated properly, and how fast the incident response process was initiated. This not only tests the tooling but also the people and processes behind your detection strategy. By running these simulations regularly, you create a feedback loop that sharpens detection rules, reduces alert fatigue (by tuning noisy signatures), and improves SOC response times, all while proving coverage against critical attack techniques.
Traditional penetration testing is typically manual, point-in-time, and scoped, conducted once or twice a year, often focusing on discovering vulnerabilities rather than validating existing defenses. While valuable, it cannot provide the continuous assurance needed to keep pace with today’s fast-changing threat landscape. Breach and Attack Simulation, by contrast, is automated, repeatable, and safe for production environments.
Threat Simulator can be scheduled to run daily, weekly, or on-demand across multiple vectors—endpoint, network, cloud—emulating real-world threats and verifying that your security stack responds as intended. Unlike pentesters who may only test a few paths due to time constraints, a BAS tool can execute hundreds of attack variations, simulate known adversary techniques (e.g., APT29, FIN7), and provide consistent, comparative reporting. This allows organizations to move from reactive, occasional testing to continuous, data-driven validation that feeds directly into SOC operations and risk management workflows.