Choose a country or area to see content specific to your location
Können wir Ihnen behilflich sein?
-
-
3D Interconnect Designer
3D Interconnect Designer bietet eine flexible Modellierungs- und Optimierungsumgebung für jede Art von fortschrittlicher Verbindungsstruktur, einschließlich Chiplets, gestapelten Chips, Gehäusen und Leiterplatten.

-
Sparen Sie bis zu 50 % beim Kauf eines XR8-Oszilloskops
Profitieren Sie von einer schnelleren digitalen Fahrzeugvalidierung zu geringeren Kosten mit einer Inzahlungnahme.

-
Entdecken Sie den Keysight AI Data Center Builder
Simulieren Sie jeden Teil Ihrer Rechenzentrumsinfrastruktur. Simulieren Sie alles. Optimieren Sie alles.

-
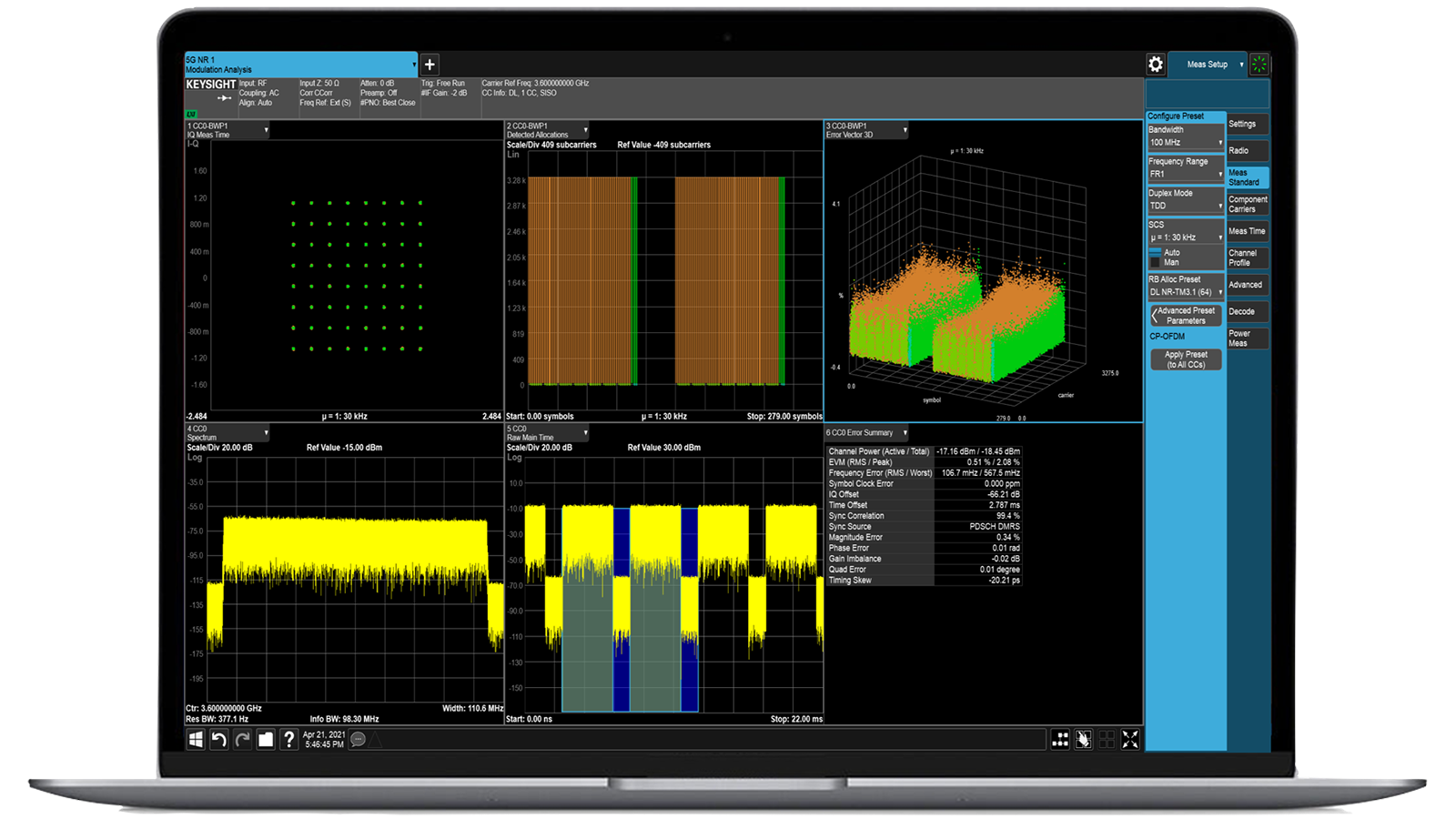
Beschleunigen Sie die Signalanalyse mit den Messanwendungen der X-Serie.
Nutzen Sie mehr als 25 Anwendungen der X-Serie zur Analyse, Demodulation und Fehlerbehebung von Signalen in den Bereichen drahtlose Kommunikation, Luft- und Raumfahrt/Verteidigung, elektromagnetische Störungen und Phasenrauschen.

-
Einführung KI-gestützter Paketbroker
Mit zusätzlichem Speicher und Speicherplatz können diese verbesserten NPBs die KI-Sicherheits- und Leistungsüberwachungssoftware sowie den KI-Stack von Keysight ausführen.

-
Präzisionsprüfung im laufenden Betrieb für die Produktion
Erreichen Sie schnelle und präzise Tests auf Platinenebene mit robusten Inline- und Offline-ICT-Systemen, die für die moderne Fertigung entwickelt wurden.

-
Beschleunigen Sie Ihren Innovationsmotor
Informieren Sie sich über kuratierte Support-Pläne, die nach Prioritäten geordnet sind, um Ihre Innovationsgeschwindigkeit aufrechtzuerhalten.
-
-
Streamen Sie 120-MHz-I/Q-Daten direkt im Feld auf Ihren Laptop.Punktgenaue Störungen mit der Nachbearbeitungssoftware für das Spektrummanagement im Labor.
 Finden Sie die passende ATE-Stromversorgungslösung
Finden Sie die passende ATE-StromversorgungslösungMit diesem Auswahltool können Sie schnell das beste Netzteil für Ihre ATE-Anforderungen im Bereich Luft- und Raumfahrt sowie Verteidigung ermitteln.

-
- Lösungen
-
Entdecken Sie von Ingenieuren verfasste Inhalte und eine umfangreiche Wissensdatenbank mit Tausenden von Lernmöglichkeiten.
AusgewähltKeysight Learn bietet umfassende Inhalte zu interessanten Themen, darunter Lösungen, Blogs, Veranstaltungen und mehr.
Mein Lern-DashboardVerfolgen. Entdecken. Personalisieren.
Alles an einem Ort. -
Schneller Zugriff auf die häufigsten unterstützungsbezogenen Selbsthilfeaufgaben.
Zusätzliche Inhalte zur Unterstützung Ihrer Produktanforderungen.
Mehr erreichen mit Keysight ServicesEntdecken Sie Dienstleistungen, die jeden Schritt Ihrer Innovationsreise beschleunigen.
Cybersicherheit: Digitaler Zwilling für Cybertraining und Bedrohungsmodellierung
Modell: SN100CYLA- Überblick
- Optionen
- Zubehör
- Software
- Unterstützung
EXata Netzwerkmodellierung - Cyber
EXata Cyber gewährleistet die Cybersicherheit von Netzwerken in allen Bereichen, vom kommerziellen IoT bis hin zu militärischen Netzwerksystemen, die vom Meeresboden bis in den Weltraum operieren.

-
Type
Model Library
-
Library
Cyber
-
Form factor
Software
Bereit für ein Angebot?
Erfahren Sie, was alles enthalten ist und welche Upgrade-Optionen von Keysight verfügbar sind.
Highlights
Schutz und Verteidigung kritischer Netzwerke
Die Wahrscheinlichkeit von Cyberangriffen mit dramatischen Folgen macht Cyberresilienz unerlässlich. Von kommerziellen Unternehmen über das Internet der Dinge bis hin zu militärischen Netzwerksystemen, die vom Meeresboden bis ins Weltall operieren, müssen proaktive und präventive Maßnahmen ergriffen werden.
Unsere bewährte Software schützt und verteidigt kritische Netzwerke mithilfe von EXata Network Modeling – Cyber (EXata Cyber). Erfahren Sie, wie sich kritische Kommunikationsnetzwerke bei Cyberangriffen verhalten, und bewerten Sie kontinuierlich Netzwerk-Schwachstellen gegenüber neuen Bedrohungen – kosteneffizient und mit geringem Risiko.

Dienstleistungen und Support
Innovieren Sie im Handumdrehen mit maßgeschneiderten Supportplänen und priorisierten Reaktions- und Bearbeitungszeiten.
Profitieren Sie von planbaren, leasingbasierten Abonnements und umfassenden Lifecycle-Management-Lösungen – damit Sie Ihre Geschäftsziele schneller erreichen.
Als KeysightCare-Abonnent profitieren Sie von einem erweiterten Service mit zuverlässiger technischer Unterstützung und vielem mehr.
Stellen Sie sicher, dass Ihr Testsystem den Spezifikationen entspricht und sowohl lokale als auch globale Standards erfüllt.
Schnelle Messungen dank hauseigener, von Ausbildern geleiteter Schulungen und E-Learning.
Laden Sie die Keysight-Software herunter oder aktualisieren Sie Ihre Software auf die neueste Version.