Choose a country or area to see content specific to your location
Che cosa sta cercando?
-
-
Progettista di interconnessioni 3D
3D Interconnect Designer offre un ambiente flessibile di modellazione e ottimizzazione per qualsiasi struttura di interconnessione avanzata, inclusi chiplet, chip impilati, contenitori e circuiti stampati.

-
Risparmia fino al 50% sull'acquisto di un oscilloscopio XR8
Ottieni una convalida digitale più rapida a un prezzo inferiore grazie alla permuta.

-
Scopri Keysight AI Data Center Builder
Emula ogni parte dell'infrastruttura del tuo data center. Emula qualsiasi cosa. Ottimizza tutto.

-
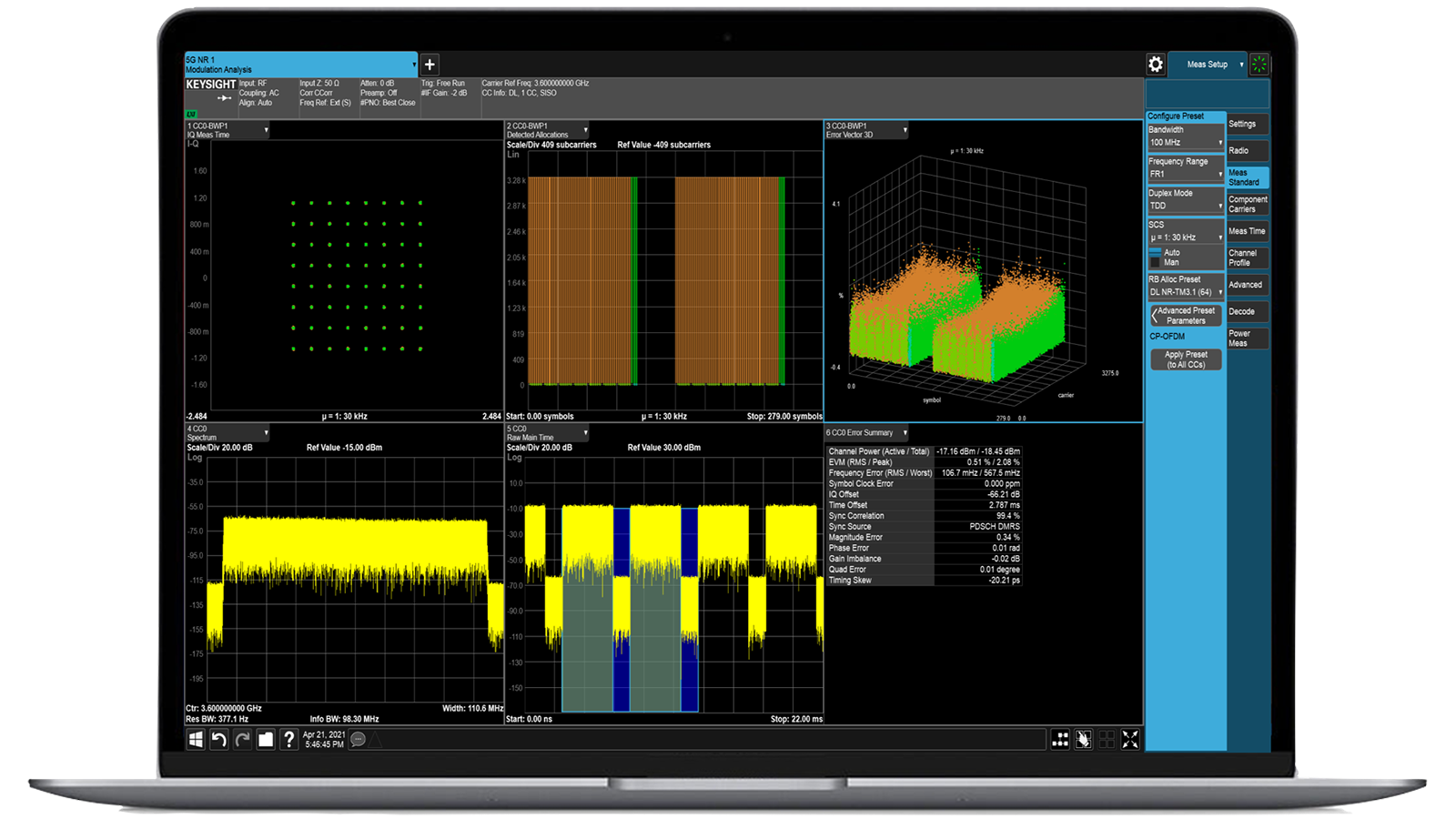
Accelerare l'analisi dei segnali con le applicazioni di misura della serie X
Utilizza oltre 25 applicazioni della serie X per analizzare, demodulare e risolvere i problemi relativi ai segnali nei settori wireless, aerospaziale/difesa, EMI e rumore di fase.

-
Introduzione ai broker di pacchetti potenziati dall'intelligenza artificiale
Grazie alla memoria e allo spazio di archiviazione aggiuntivi, questi NPB potenziati eseguono il software di sicurezza e monitoraggio delle prestazioni AI di Keysight e lo stack AI.

-
Test di precisione in-circuit per la produzione
Ottieni test rapidi e accurati a livello di scheda con un solido ICT in linea e offline progettato per la produzione moderna.

-
Accelerare il motore dell'innovazione
Esplorate i piani di assistenza curati, con priorità per mantenere la velocità dell'innovazione.
-
Generazione di forme d'onda a 448 Gb/s
Raggiungete segnali modulati a più livelli di 200+ Gbaud con AWG ad alta velocità per standard digitali e ottici.

-
Trasmetti dati I/Q a 120 MHz al tuo laptop sul campoIndividuare le interferenze con il software di gestione dello spettro di post-elaborazione in laboratorio.
 Trova la soluzione di alimentazione ATE più adatta alle tue esigenze
Trova la soluzione di alimentazione ATE più adatta alle tue esigenzeUtilizza questo strumento di selezione per individuare rapidamente l'alimentatore più adatto alle tue esigenze in materia di ATE nel settore aerospaziale e della difesa.

-
- Soluzioni
-
Esplorate i contenuti scritti dagli ingegneri e una vasta base di conoscenze con migliaia di opportunità di apprendimento.
In primo pianoKeysight Learn offre contenuti coinvolgenti su argomenti di interesse, tra cui soluzioni, blog, eventi e altro ancora.
Il mio cruscotto di apprendimentoTraccia. Scoprire. Personalizzare.
Tutto in un unico posto. - Acquistare
-
Accesso rapido alle attività di auto-aiuto relative al supporto.
Contenuti aggiuntivi per supportare le vostre esigenze di prodotto.
Fare di più con i servizi KeysightEsplorate i servizi per accelerare ogni fase del vostro percorso di innovazione.
BreakingPoint VE Emulatore virtuale per test di resilienza al traffico e alle minacce
- Panoramica
- Tutti i modelli
- Supporto
Test di resilienza della sicurezza virtualizzati per le reti aziendali
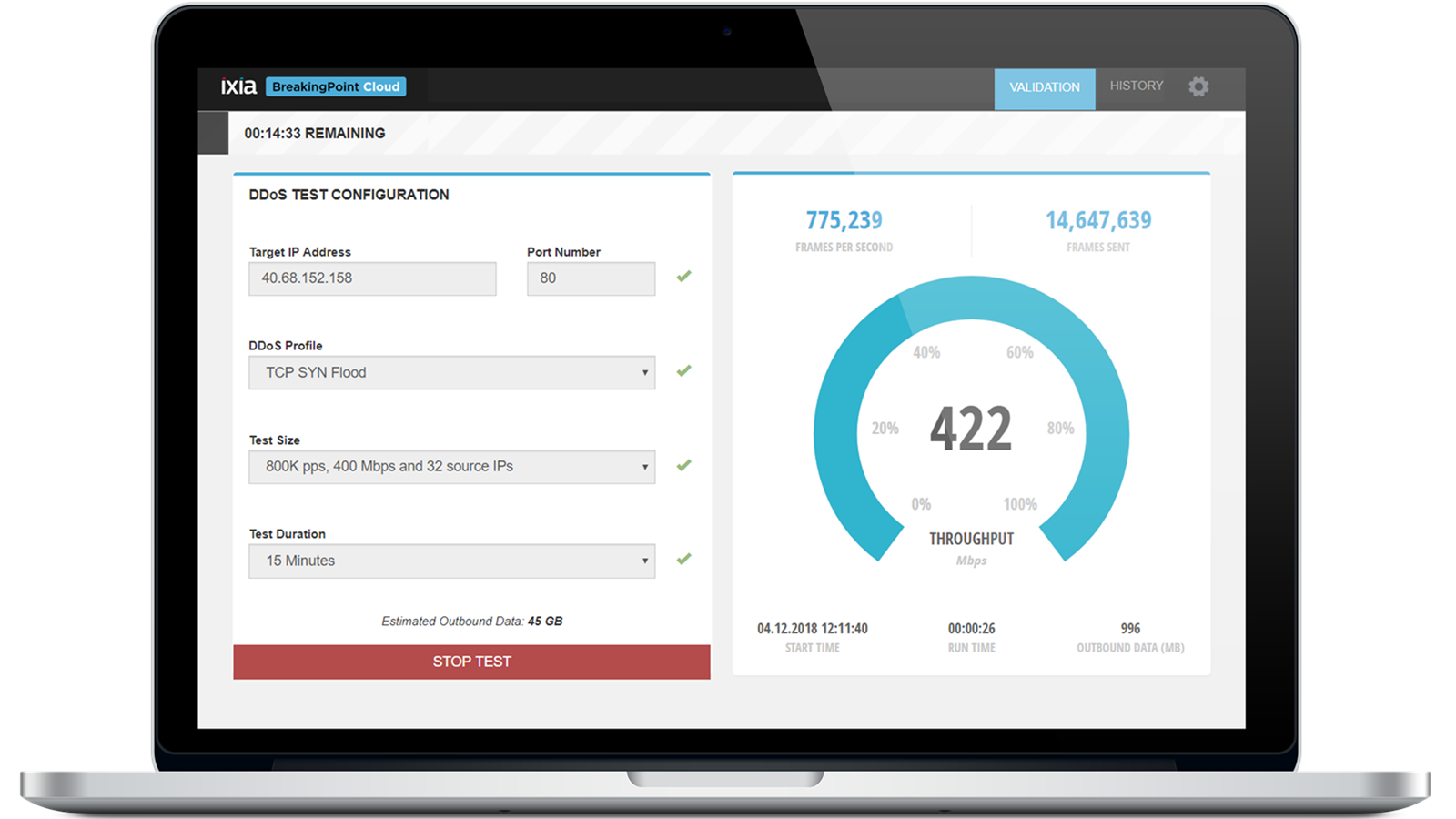
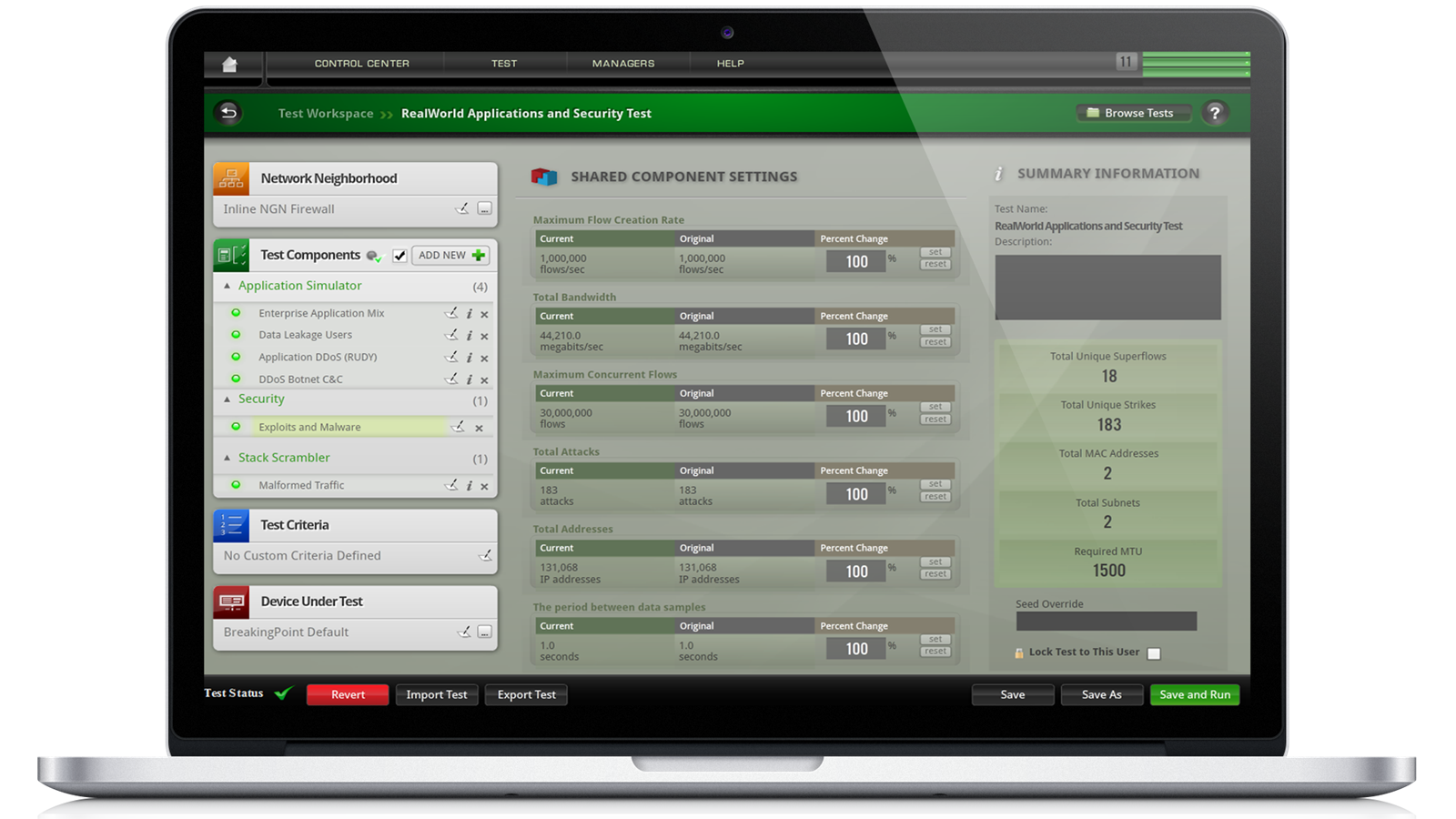
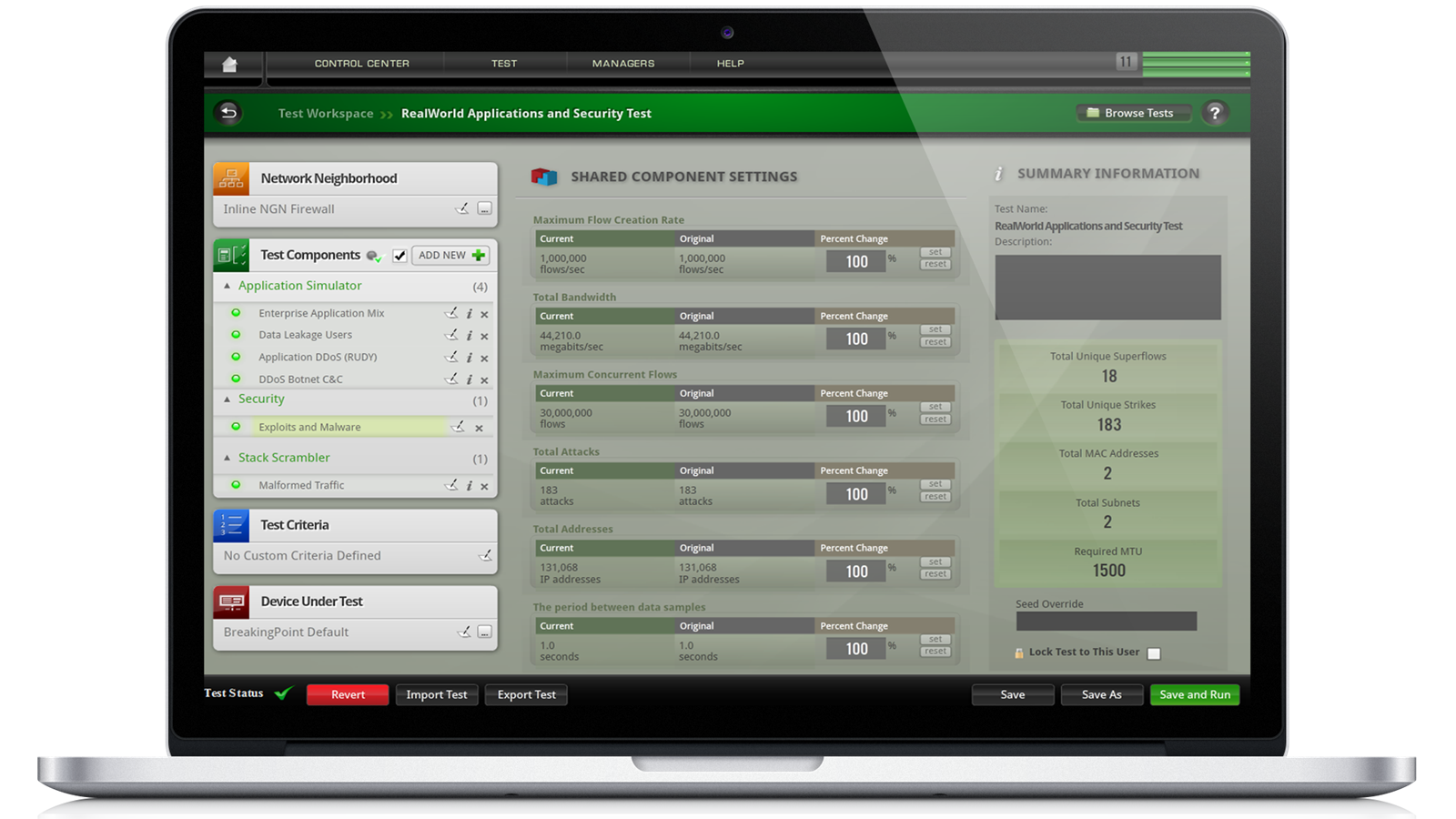
Il software Keysight BreakingPoint VE offre funzionalità di sicurezza comprovate per ambienti di test virtualizzati e cloud-native. Consente una validazione completa della sicurezza per firewall virtuali, controlli di sicurezza basati su cloud e reti definite dal software. Integrato nelle pipeline CI/CD, BreakingPoint VE fornisce un'emulazione automatizzata e realistica degli attacchi per garantire la sicurezza del codice e delle configurazioni prima della distribuzione. Richiedete oggi stesso un preventivo per una delle nostre configurazioni più richieste.Avete bisogno di aiuto per scegliere? Consultate le risorse riportate di seguito.
Implementazione cloud-native
Avvia come macchina virtuale su piattaforme cloud pubbliche, private e ibride per eseguire test flessibili e su richiesta.
Integrazione della sicurezza CI/CD
Integra perfettamente i test di sicurezza nelle pipeline DevOps per convalidare firewall virtuali, SD-WAN e VNF durante lo sviluppo.
Scalabilità dei test elastici
Scala la generazione del traffico di attacco su più nodi di test per simulare il volume e il comportamento reali.
Informazioni sulle minacce
Libreria di minacce e applicazioni per una convalida coerente in ambienti fisici e virtuali.
Configurazioni più popolari
BreakingPoint Virtual Edition (VE) 10G Licenza perpetua flottante
BreakingPoint Virtual Edition (VE) 10G Licenza perpetua flottante
939-9619
L'edizione virtuale (VE) 10G di Keysight BreakingPoint include una licenza perpetua flottante valida in tutto il mondo.
- Testare i componenti più critici dei dispositivi e delle reti virtuali e fisici sensibili alle applicazioni; convalidare vari attacchi e difese contro gli attacchi distribuiti di tipo denial-of-service.
- Ottimizza la configurazione dei dispositivi di sicurezza di rete virtuali o fisici, quali IDS, IPS, DLP, UTM, NGFW, WAF e proxy web.
- Resta al passo con il panorama delle minacce in continua evoluzione aggiornando le tue applicazioni, gli attacchi e il malware tramite aggiornamenti quotidiani delle informazioni sulle applicazioni e sulle minacce.
- Valuta l'impatto della mobilità delle macchine virtuali sull'affidabilità e la scalabilità delle applicazioni. Esegui i test durante la migrazione live per garantire tempi di inattività della rete minimi.
- Convalida le reti 5G / NFV di nuova generazione eseguendo test su cloud privati / cloud di telecomunicazioni basati su OpenStack o VMware vCenter Orchestration.
- Comprendere in che modo l'implementazione in diversi cloud pubblici, come Alibaba Cloud, Amazon AWS, Google Cloud e Microsoft Azure, influisce sulle applicazioni di rete.
- Sfrutta le licenze basate su abbonamento che consentono la flessibilità di un modello di spese operative pay-as-you-grow con diverse licenze disponibili in più livelli di prestazioni, come 1G / 10G / 100G.
BreakingPoint Virtual Edition (VE) 100G Licenza di abbonamento annuale
BreakingPoint Virtual Edition (VE) 100G Licenza di abbonamento annuale
939-9640
L'edizione virtuale (VE) 100G di Keysight BreakingPoint include una licenza flottante mondiale della durata di 12 mesi e un abbonamento al supporto software Keysight.
- Testare i componenti più critici dei dispositivi e delle reti virtuali e fisici sensibili alle applicazioni; convalidare vari attacchi e difese contro gli attacchi distribuiti di tipo denial-of-service.
- Ottimizza la configurazione dei dispositivi di sicurezza di rete virtuali o fisici, quali IDS, IPS, DLP, UTM, NGFW, WAF e proxy web.
- Resta al passo con il panorama delle minacce in continua evoluzione aggiornando le tue applicazioni, gli attacchi e il malware tramite aggiornamenti quotidiani delle informazioni sulle applicazioni e sulle minacce.
- Valuta l'impatto della mobilità delle macchine virtuali sull'affidabilità e la scalabilità delle applicazioni. Esegui i test durante la migrazione live per garantire tempi di inattività della rete minimi.
- Convalida le reti 5G / NFV di nuova generazione eseguendo test su cloud privati / cloud di telecomunicazioni basati su OpenStack o VMware vCenter Orchestration.
- Comprendere in che modo l'implementazione in diversi cloud pubblici, come Alibaba Cloud, Amazon AWS, Google Cloud e Microsoft Azure, influisce sulle applicazioni di rete.
- Sfrutta le licenze basate su abbonamento che consentono la flessibilità di un modello di spese operative pay-as-you-grow con diverse licenze disponibili in più livelli di prestazioni, come 1G / 10G / 100G.
BreakingPoint Virtual Edition (VE) Licenza di abbonamento flottante 1GE
BreakingPoint Virtual Edition (VE) Licenza di abbonamento flottante 1GE
939-9600
L'edizione virtuale (VE) 1GE di Keysight BreakingPoint include una licenza flottante mondiale della durata di 12 mesi e un abbonamento al supporto software Keysight.
- Testare i componenti più critici dei dispositivi e delle reti virtuali e fisici sensibili alle applicazioni; convalidare vari attacchi e difese contro gli attacchi distribuiti di tipo denial-of-service.
- Ottimizza la configurazione dei dispositivi di sicurezza di rete virtuali o fisici, quali IDS, IPS, DLP, UTM, NGFW, WAF e proxy web.
- Resta al passo con il panorama delle minacce in continua evoluzione aggiornando le tue applicazioni, gli attacchi e il malware tramite aggiornamenti quotidiani delle informazioni sulle applicazioni e sulle minacce.
- Valuta l'impatto della mobilità delle macchine virtuali sull'affidabilità e la scalabilità delle applicazioni. Esegui i test durante la migrazione live per garantire tempi di inattività della rete minimi.
- Convalida le reti 5G / NFV di nuova generazione eseguendo test su cloud privati / cloud di telecomunicazioni basati su OpenStack o VMware vCenter Orchestration.
- Comprendere in che modo l'implementazione in diversi cloud pubblici, come Alibaba Cloud, Amazon AWS, Google Cloud e Microsoft Azure, influisce sulle applicazioni di rete.
- Sfrutta le licenze basate su abbonamento che consentono la flessibilità di un modello di spese operative pay-as-you-grow con diverse licenze disponibili in più livelli di prestazioni, come 1G / 10G / 100G.
Servizi e assistenza
Innova rapidamente grazie a piani di assistenza personalizzati e tempi di risposta e risoluzione prioritari.
Ottieni abbonamenti prevedibili basati su leasing e soluzioni complete per la gestione dell'intero ciclo di vita, in modo da raggiungere più rapidamente i tuoi obiettivi aziendali.
Beneficia di un servizio di alto livello come abbonato KeysightCare per ottenere assistenza tecnica dedicata e molto altro ancora.
Assicurati che il tuo sistema di test funzioni secondo le specifiche e soddisfi gli standard locali e globali.
Effettua misurazioni rapidamente grazie alla formazione interna con istruttore e all'e-learning.
Scarica il software Keysight o aggiorna il tuo software alla versione più recente.
Domande frequenti
Le piattaforme di test di sicurezza virtualizzate offrono vantaggi esclusivi rispetto alle apparecchiature hardware, specialmente in ambienti sempre più incentrati sul cloud e definiti dal software. Sebbene l'hardware di test fisico sia efficace per i laboratori dedicati in loco, spesso è costoso, meno flessibile e limitato dall'implementazione fisica. Le soluzioni virtuali, invece, possono essere implementate rapidamente in macchine virtuali o istanze cloud, consentendo alle organizzazioni di eseguire test della stessa portata e complessità senza richiedere hardware specializzato. Sono particolarmente adatte alle organizzazioni che adottano strategie cloud-first, infrastrutture ibride o pipeline di integrazione continua e consegna continua, dove i test devono essere avviati e interrotti su richiesta. Questa elasticità aiuta a ridurre i costi, ad allinearsi ai flussi di lavoro DevOps e a garantire che la convalida della sicurezza sia integrata senza soluzione di continuità nei processi di sviluppo agile.
Una piattaforma di emulazione di attacchi virtuali consente di eseguire test su tutta la gamma dei controlli di sicurezza di rete e delle applicazioni. Ciò include le tradizionali difese perimetrali come firewall e sistemi di prevenzione delle intrusioni, nonché le più recenti tecnologie cloud native come Secure Access Service Edge (SASE), Zero Trust Network Access (ZTNA) e funzioni di rete virtualizzate. Oltre ai dispositivi di sicurezza, queste piattaforme possono testare strumenti di protezione degli endpoint, filtri dei contenuti, difese a livello di applicazione e persino i servizi di sicurezza cloud emergenti offerti dai principali provider. Poiché la soluzione opera a livello software, si integra facilmente in ambienti distribuiti, rendendo possibile testare sia i sistemi legacy nei data center che i moderni carichi di lavoro distribuiti in cloud pubblici o privati. In sostanza, garantisce che ogni livello di sicurezza, dall'edge al core al cloud, possa essere convalidato in condizioni realistiche.
Il realismo si ottiene emulando modelli di traffico sia benigni che dannosi su larga scala. Dal punto di vista delle applicazioni, le piattaforme possono replicare il modo in cui gli utenti reali interagiscono con servizi quali la navigazione web, la posta elettronica, lo streaming video e la condivisione di file, spesso attraverso connessioni crittografate. Dal punto di vista delle minacce, generano campagne di attacco che rispecchiano le tattiche utilizzate dagli avversari nel mondo reale, inclusi payload di malware, attacchi denial-of-service e exploit di protocollo. Questo duplice approccio crea un ambiente di test che mette alla prova i controlli di sicurezza per distinguere tra traffico legittimo e tentativi dannosi, proprio come dovrebbero fare in produzione. Inoltre, le piattaforme virtualizzate spesso consentono la personalizzazione dei profili di traffico, dell'intensità degli attacchi e dei parametri di crittografia, offrendo ai tester la possibilità di rispecchiare il loro ambiente operativo unico. Il risultato è un processo di convalida altamente realistico che produce informazioni utili sulla resilienza del sistema, la scalabilità e i potenziali punti ciechi.
Uno dei vantaggi più significativi di una piattaforma di test di sicurezza virtualizzata è il modello flessibile di licenza e scalabilità che consente. Anziché essere limitate dalla capacità di un dispositivo fisico, le organizzazioni possono iniziare con una capacità modesta, magari testando un singolo firewall, una rete privata virtuale o un gateway web sicuro, per poi espandersi senza soluzione di continuità fino a convalidare sistemi distribuiti su larga scala. I modelli di licenza sono in genere basati sul consumo o sull'abbonamento, consentendo alle aziende di allineare gli investimenti all'utilizzo. Ad esempio, un team può eseguire test intensivi solo durante specifici cicli di sviluppo o audit di conformità e ridimensionare durante i periodi di calma, ottimizzando l'efficienza dei costi. Inoltre, poiché la soluzione è virtuale, il ridimensionamento può avvenire orizzontalmente attraverso il cloud o l'infrastruttura virtualizzata, sfruttando risorse di calcolo aggiuntive piuttosto che richiedere l'acquisto di nuovo hardware. Questo modello supporta sia i piccoli laboratori che le imprese globali con implementazioni complesse e multisito.
Le moderne piattaforme di test di sicurezza si basano su feed di intelligence sulle minacce continuamente aggiornati per rimanere rilevanti. Questi aggiornamenti coprono in genere nuovi comportamenti delle applicazioni, vettori di attacco emergenti, campagne di malware e tecniche di evasione avanzate osservate nel mondo reale. Gli aggiornamenti vengono forniti direttamente nella libreria di emulazione, garantendo che i test riflettano l'attuale panorama delle minacce senza richiedere scripting o configurazioni manuali da parte dell'utente finale. Questo processo è particolarmente critico data la rapidità con cui si evolvono le minacce informatiche; una libreria di test obsoleta fornirebbe un falso senso di sicurezza. Rimanendo allineate con le ultime vulnerabilità ed exploit, le organizzazioni possono verificare se le loro difese sono in grado di resistere ai metodi di attacco attuali e futuri. Oltre ai semplici aggiornamenti, alcune piattaforme offrono anche la possibilità di personalizzare e creare nuovi profili di attacco, offrendo agli utenti avanzati la flessibilità di modellare minacce uniche rilevanti per il loro settore o ambiente. Ciò garantisce che i test non solo coprano i rischi noti, ma anticipino anche potenziali strategie di attacco future.