What are you looking for?
Build Your Own Device Security Test Lab
Design your lab based on your needs, target, and security goals, using a modular combination of hardware, software, and expert training for embedded systems, chips, and secure elements
Hardware Attacks Are A Growing Concern
Embedded systems are becoming more powerful, more connected, and more exposed. At the same time, attacks on hardware evolve rapidly, expanding beyond software exploits into physical techniques such as side‑channel analysis (SCA) and fault injection (FI).
Fixing hardware weaknesses late in development is costly and often impractical, and in some cases impossible once devices ship. A tightening regulatory landscape, including the Cyber Resilience Act (CRA), RED, and EU Common Criteria, now demands stronger and more demonstrable security assurance.
Combined with rising time‑to‑market pressure, organizations need early, effective, and repeatable device security testing. As more industries depend on secure embedded systems, teams require not only tools, but a clear and scalable architecture for building in‑house device security capability.
Why Build A Device Security Test Lab?
Architecture Of A Device Security Lab
Every device security lab, regardless of industry or maturity, is built on the same four foundational elements. Together, they form a flexible architecture that can scale from first experiments to high‑assurance validation.
How It Works
There is no single “correct” device security lab. Each setup depends on what you are testing, how much insight you have into the target, and which threats you need to address. The lab is built by combining the right target preparation, hardware capabilities, software analysis, and expert operation.
Device Under Test (DUT)
When we refer to embedded security testing, these are the primary types of targets:
- SoCs (System on Chip).
- FPGAs (Field‑Programmable Gate Arrays).
- ASICs (Application‑Specific Integrated Circuits).
- Smart cards and secure microcontrollers.
This is where everything begins, the DUT is mounted, powered, and prepared for stable, repeatable measurements.


Hardware
At the core of every lab is the PXI Embedded Security Testbench, the heart and brain of the setup. Operating in headless mode, it functions as your oscilloscope, timing controller, synchronization engine, and workstation.
From there, you add one or more attack and observation capabilities:
- Power: Measure and manipulate power consumption.
- Clock: Inject precise timed anomalies in the clock signal.
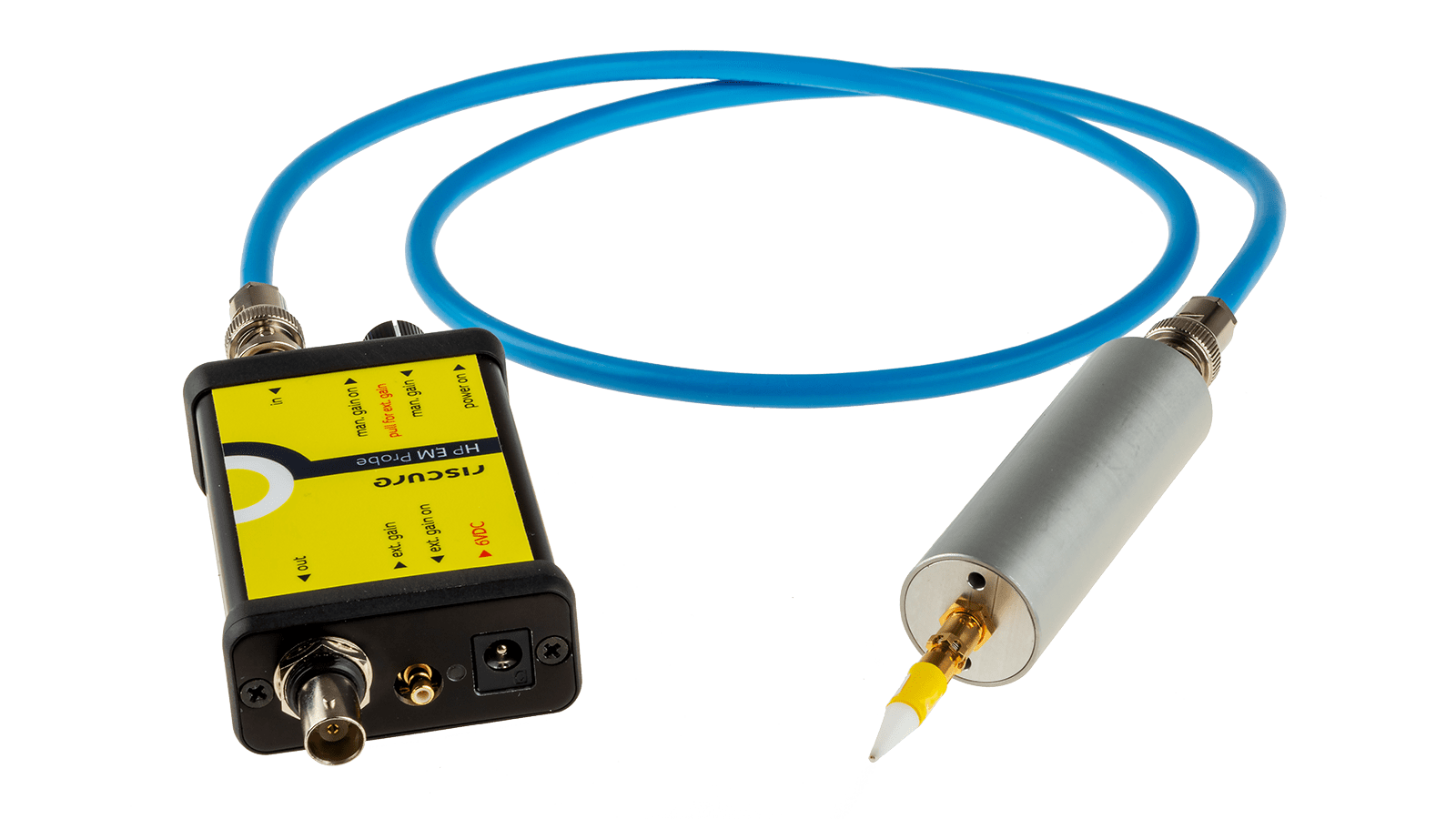
- Electromagnetic (EM): Observe EM leakage or inject EM faults.
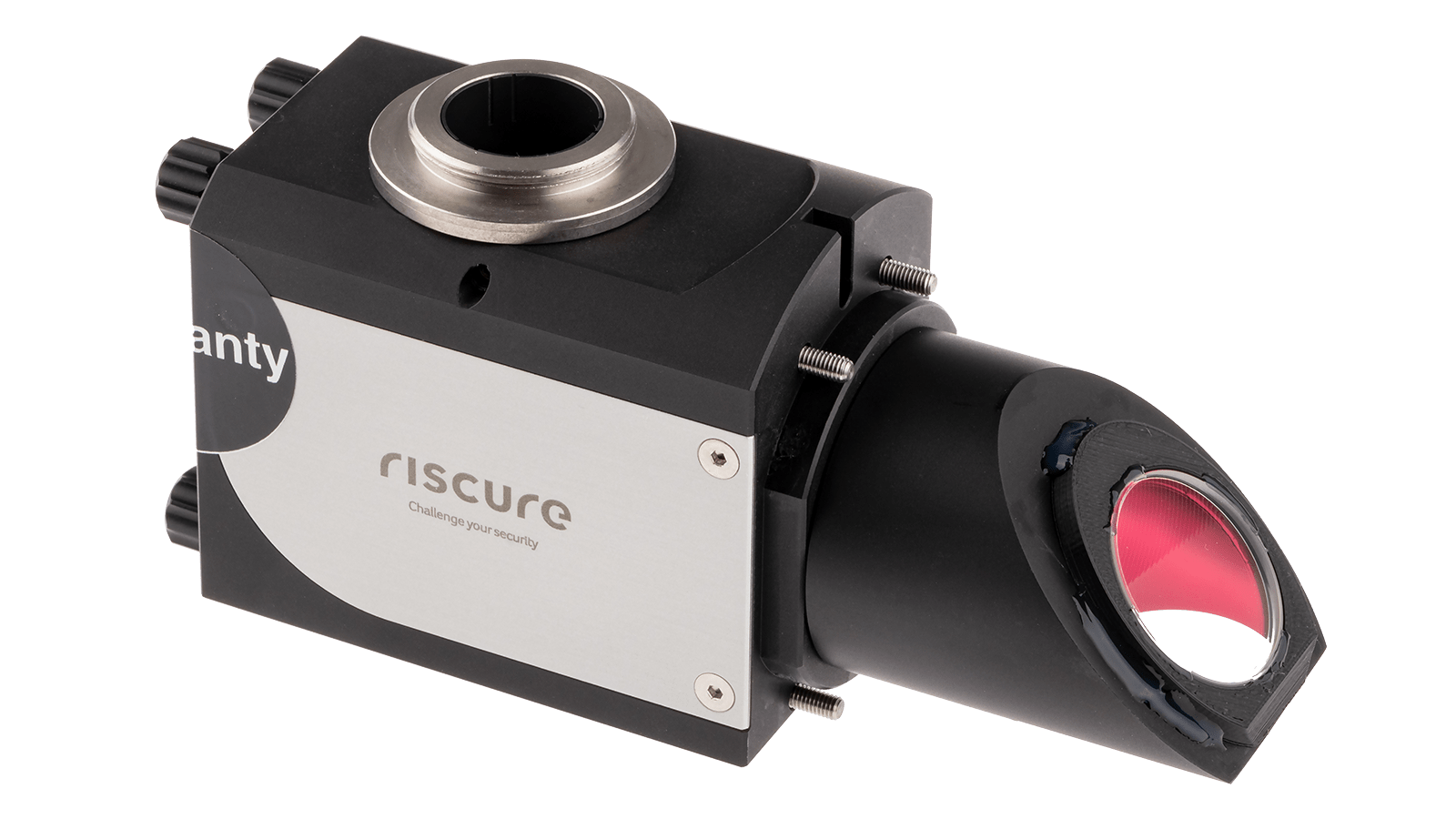
- Laser (Optical): Perform precise optical fault injection.
These capabilities may be used individually or combined depending on the device architecture and testing goals.
Inspector Software Suite
The Inspector Software Suite is the unified platform for complete Side‑Channel Analysis (SCA) and Fault Injection (FI) campaigns, supporting the journey from data acquisition to security insight.
Inspector enables a consistent end‑to‑end workflow, allowing teams to acquire measurements, process and analyze signals, and evaluate device behavior under fault conditions within a single environment.
- Side‑Channel Analysis (SCA): Identifying and quantifying information leakage through power, electromagnetic, or optical behavior.
- Fault Injection (FI): Actively disrupting execution to expose weaknesses and assess countermeasures.
By combining SCA and FI in one platform, Inspector allows teams to move seamlessly from observing leakage to actively validating device security, using consistent workflows and shared timing and measurement infrastructure.
Built on more than two decades of device security expertise, Inspector is modular and extensible, supporting a wide range of devices, algorithms, and assurance levels.


Training & Lifecycle Support
A successful lab needs more than tools, it requires expert operators. New attacks, countermeasures, and regulations appear each year.
Keysight supports teams with:
- Essential training for SCA and FI.
- Continuous software updates.
- New hardware capabilities.
- Expert support throughout your security lifecycle.
Choosing the Right Lab Setup
The choices you make while building a device security lab depend on your goals, available expertise, target complexity, and regulatory obligations. To support this, Keysight offers four modular lab levels, all built on the same architecture
Essential Testing Lab
Entry‑level professional SCA and FI
The first step that brings you above hobbyist systems towards a professional setup, ideal for organizations transitioning from open‑source solutions to a professional, repeatable, and high‑performance device security environment. This lab provides everything needed to begin SCA and FI testing.
Black Box Lab
Solution: Power and Electromagnetic Side‑Channel Analysis & Fault Injection
White Box Lab
Solution: Power, Electromagnetic, and Laser Side‑Channel Analysis & Fault Injection
The White Box Lab is built for organizations that develop their own products and need to validate them against high‑assurance security requirements, including advanced optical (laser) fault injections. This setup combines full‑spectrum SCA/FI capabilities, enabling deep analysis of custom silicon, secure microcontrollers, and products requiring certification
Ultimate Lab
Solution: Complete Power, EM, and Laser SCA/FI – Multi‑Workstation, Full‑Scale Hardware Security Lab
The Ultimate Lab Experience is designed for organizations that require the highest possible testing capability, combining everything in the Side‑Channel Analysis and Fault Injection domain. This multi‑bench, multi‑operator environment supports both black‑box and white‑box testing, allowing continuous parallel investigations across all known hardware attack vectors.
Built for teams that perform large‑scale evaluations, certification testing, red‑teaming, and advanced research, this lab represents the top tier of professional device security infrastructure.
Core Building Blocks
A device security lab is built from modular hardware components that work together to observe, measure, and influence a device’s physical behavior. While lab configurations vary by goal and assurance level, they all rely on the same core building blocks, from PXI‑based instrumentation to power, electromagnetic, and optical attack capabilities.
Which Industries Need Device Security Testing Labs
Even though industries differ in their products, regulations, or assurance levels, the underlying embedded systems and attack surfaces remain similar. Device security labs therefore share common building blocks, while the depth of testing and required capabilities vary per market.
FAQs
No. The lab is designed to support teams at different experience levels. Guided workflows, Inspector software, and structured training programs help teams become productive quickly, even if they are new to SCA or FI techniques.
Side‑Channel Analysis and Fault Injection address different aspects of the same security problem and are most effective when used together.
SCA reveals what information a device may unintentionally leak through its physical behavior, such as power consumption or electromagnetic emissions. FI, on the other hand, is used to actively disrupt execution to expose weaknesses and validate whether security mechanisms behave as expected under fault conditions.
By combining SCA and FI within a single lab environment, teams can move seamlessly from observing leakage to actively challenging countermeasures, using the same target setup, timing infrastructure, and measurement chain. This integrated approach provides a more realistic and complete assessment of a device’s security posture.
The Core PXI Embedded Security Testbench is designed to support both SCA and FI natively, enabling consistent, repeatable testing workflows without treating them as separate or isolated disciplines.
Yes. All lab levels are modular and built on the same underlying architecture. You can start with a basic configuration and expand over time by adding new hardware capabilities, software modules, or additional workstations as your testing needs evolve.
The lab scales naturally with your organization. Starting from a single PXI‑based testbench, you can grow to multi‑operator or multi‑capability environments without replacing your initial investment. Hardware modules, probes, and Inspector software licenses can be added incrementally as your maturity increases.
Yes. The same lab architecture can be used throughout the product lifecycle from pre-silicon, early firmware validation and silicon characterization to countermeasure evaluation and high‑assurance testing. The methodology aligns with practices commonly used in EU Common Criteria (CC), CRA, and similar evaluation schemes.
Entry‑level configurations, such as My First Lab, can be operational within days. More advanced setups involving EM or laser capabilities may require additional installation and setup time. In all cases, training and onboarding are available to accelerate time‑to‑value.
Yes. Keysight offers continuous software updates, global calibration services, preventive maintenance, and a broad portfolio of training programs for SCA, FI, and advanced methodologies. This ensures your lab remains effective as devices, threats, and standards evolve.
All lab levels share the same PXI‑based foundation, meaning you can start with a single bench and expand to multi‑operator or multi‑capability setups without replacing your initial investment. Hardware modules, probes, and Inspector software licenses scale naturally as your maturity increases.
Want help or have questions?








































/hands-on-keyboard-2.jpg)
/keysight-inspector-fj2-fault-injection-system-power-bundle.jpeg)



