Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
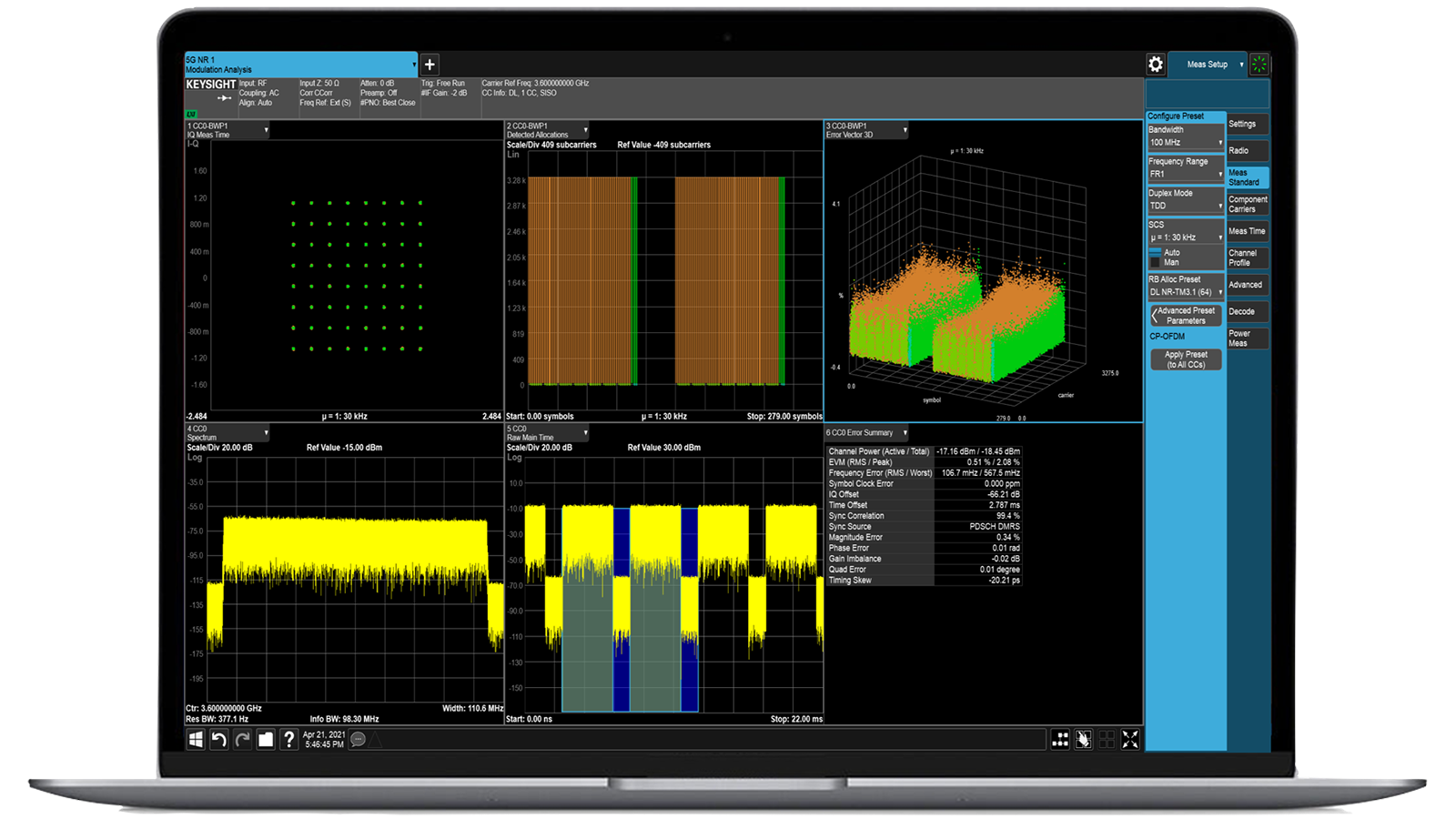
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
- Buy
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
Cyber Security Operations Platform Train Cyber Warriors to Fight Threats in a Real-World Environment

- Overview
- All Models
- Support
Improve Your Cyber Resilience with Simulated Attacks
Rich scenarios library
With practice using a variety of simulated threat scenarios, your security team gains hands-on cybersecurity skills. We can also help you build customized cyber exercises using products in your network, so you can test your team under the actual conditions they’ll face. Our platform also allows you to create your own scenarios from scratch or to change any of the default as-built scenarios.
Simulations of common or unusual cyberattacks
Our cyber range scenarios emulate a network security breach exactly, by performing the attack using real live payloads detonated in a secure isolated environment. This gives you a true test of how your security staff will respond as individuals and as a team in the case of a live cyberattack.
Real-world traffic generator
The BreakingPoint traffic generator, an optional component of Keysight cyber range solution, is capable of simulating more than 490 real-world application protocols and sending strikes using a combination of over 60,000 attacks or malware. Your security pros will experience unfamiliar and hard-to-identify, as well as realistic and random traffic — just as they would on the front lines, during a live cyberattack.
Neverending threats or just for training
Your team needs continuous training to keep their skills sharp, collaborate effectively, and maintain your organization’s protection level.
Most popular configurations

TAA Compliant, Cyber Security Operations Platform (CySOP) Promotional Bundle with 10 tenants and a Floating Subscription License (1-year)
TAA Compliant, Cyber Security Operations Platform (CySOP) Promotional Bundle with 10 tenants and a Floating Subscription License (1-year)
983-4101
The bundle includes licensing to support the execution of user administration, learning, orchestration, threat scenarios, and Capture the Flag (CTF) within a cyber range solution. It also supports 10 tenants per deployment.
- Easy-to-use solution for cyber security assessment.
- Multi-tenant architecture.
- Security tool agnostic.
- Predefined and customizable threat scenarios.
- Real-world simulations using Keysight tools (optional).
- Capture the Flag events promote increased team collaboration.

TAA Compliant, Cyber Security Operations Platform (CySOP) Promotion optional add-on to add five additional tenants and a Floating Subscription License (1-year)
TAA Compliant, Cyber Security Operations Platform (CySOP) Promotion optional add-on to add five additional tenants and a Floating Subscription License (1-year)
983-4102
The bundle includes an additional five tenants for threat scenarios and capture the flag (CTF). It can be used cumulatively, up to the system supported by a maximum of 120 tenants per installation.
- Easy-to-use solution for cyber security assessment.
- Multi-tenant architecture.
- Security tool agnostic.
- Predefined and customizable threat scenarios.
- Real-world simulations using Keysight tools (optional).
- Capture the Flag events promote increased team collaboration.

TAA Compliant, Cyber Security Operations Platform (CySOP) with a Perpetual Floating License
TAA Compliant, Cyber Security Operations Platform (CySOP) with a Perpetual Floating License
972-5921
The bundle includes licensing to support the execution of user administration, learning, orchestration, and threat scenarios within a cyber range solution. It also supports full complement of 120 tenants.
- Easy-to-use solution for cyber security assessment.
- Multi-tenant architecture.
- Security tool agnostic.
- Predefined and customizable threat scenarios.
- Real-world simulations using Keysight tools (optional).
- Capture the Flag events promote increased team collaboration.
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
Cybersecurity validation is the process of rigorously testing and measuring the effectiveness of an organization’s security tools, processes, and policies under realistic attack conditions. Rather than assuming that firewalls, intrusion prevention systems, endpoint protections, and monitoring solutions are functioning as intended, validation ensures they are continuously challenged against the latest threats. This involves safely simulating adversarial behavior, such as malware delivery, lateral movement, privilege escalation, or data exfiltration, to reveal how defenses perform in real-world scenarios.
The importance of cybersecurity validation lies in its ability to provide clear, evidence-based insights into whether security investments are truly mitigating risk. In many organizations, security teams face the challenge of managing multiple technologies from different vendors, each generating alerts and telemetry. Without validation, it is difficult to know if these tools are correctly tuned, integrated, and capable of stopping advanced or blended threats. Regular validation bridges this gap by offering measurable results that highlight strengths, uncover misconfigurations, and pinpoint vulnerabilities before attackers can exploit them.
Beyond improving defenses, validation plays a key role in strategic decision-making. Security leaders can use the outcomes to prioritize remediation based on the most critical risks, allocate resources more effectively, and demonstrate resilience to executive stakeholders, regulators, and customers. It also enhances security team readiness by training staff in responding to realistic attack chains, ultimately building confidence that defenses are not only deployed but also operating at the level required to protect the organization.
A digital twin in cybersecurity is a virtual replica of your actual network environment, including routers, switches, applications, endpoints, and even control systems like SCADA or industrial protocols. By mirroring the structure and behavior of a real network, this model allows you to run sophisticated attack simulations that mimic adversary behavior such as lateral movement, zero-day exploitation, or insider threats without any risk to production systems. In platforms like Keysight cyber security software, the digital twin responds in real time to changes in traffic, bandwidth, latency, and attack scenarios, enabling users to observe how malware propagates, how defenses trigger, and how network resilience degrades under sustained attack. This capability is critical for understanding cascading failure points, validating contingency plans, and building organizational muscle memory before an actual incident occurs.
While both serve to evaluate cybersecurity posture, a cyber range offers a far more comprehensive, interactive, and scalable environment than a traditional penetration test lab. A penetration test is often a scoped, manual assessment aimed at identifying exploitable vulnerabilities over a short time frame. In contrast, a cyber range like the one enabled by Keysight cyber security software emulates the full lifecycle of cyber operations across realistic network conditions and system interactions. It supports offensive (red team) and defensive (blue team) exercises, allowing simultaneous attack/defense training, response drills, and malware behavior analysis. A cyber range can simulate the impact of multi-stage attacks, failed security responses, or infrastructure outages in a way that’s not feasible in a controlled pen test. Moreover, it supports continuous training, policy evaluation, and decision-making practice under stress, key capabilities for national defense, critical infrastructure, or enterprise SOC readiness.
Yes. One of Keysight Cyber Security platform's strengths is its ability to model hybrid environments that include both traditional IT networks and operational technology systems, such as industrial control systems (ICS), SCADA, and smart grid components. These systems often have unique protocols (e.g., Modbus, DNP3, IEC 61850), timing constraints, and topology designs that differ significantly from enterprise networks. With Keysight cyber security software, users can accurately emulate the behavior of both domains and examine how cyberattacks might cross between them; for instance, how an infected workstation might manipulate programmable logic controllers (PLCs) or disrupt telemetry in a utility grid. This dual-domain simulation helps security teams assess cross-domain risks, validate segmentation and anomaly detection strategies, and train for scenarios like cyber-physical sabotage or ransomware targeting infrastructure.
Mission-critical training requires more than just static labs; it demands realistic, time-bound, adversary-aware scenarios that reflect real-world complexity. Keysight Cyber Security platform enables this by offering an immersive environment where red and blue teams can engage in offensive and defensive cyber campaigns. The platform includes customizable attack templates, response injects, and scenario progression logic that adapts based on user actions. Participants can simulate supply chain attacks, reconnaissance missions, or coordinated insider threats, while defenders respond with monitoring, containment, and forensic analysis, all under live network conditions. Real-time scoring, debrief reporting, and behavior analysis help commanders or training coordinators assess readiness, identify decision bottlenecks, and improve response strategies. For government, military, and critical sectors, this form of hands-on, consequence-free training is essential for developing resilient, coordinated cyber response teams.