Per saperne di più
keysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-testkeysight:dtx/solutions/facets/development-area/power,keysight:dtx/solutions/facets/industry/automotive,keysight:dtx/solutions/facets/industry/semiconductor,keysight:dtx/solutions/facets/design-and-test-product/power-analyzer,segmentation:campaign/Automotive_Energy,segmentation:product-category/Automotive_Testing,segmentation:product-category/Automotive_Testing/Automotive_Power,segmentation:business-unit/EISG,keysight:product-lines/sp,segmentation:funnel/bofu,keysight:dtx/solutions/facets/workflow-stage/functional-test
Come testare i moduli di potenza a semiconduttore ad ampio bandgap
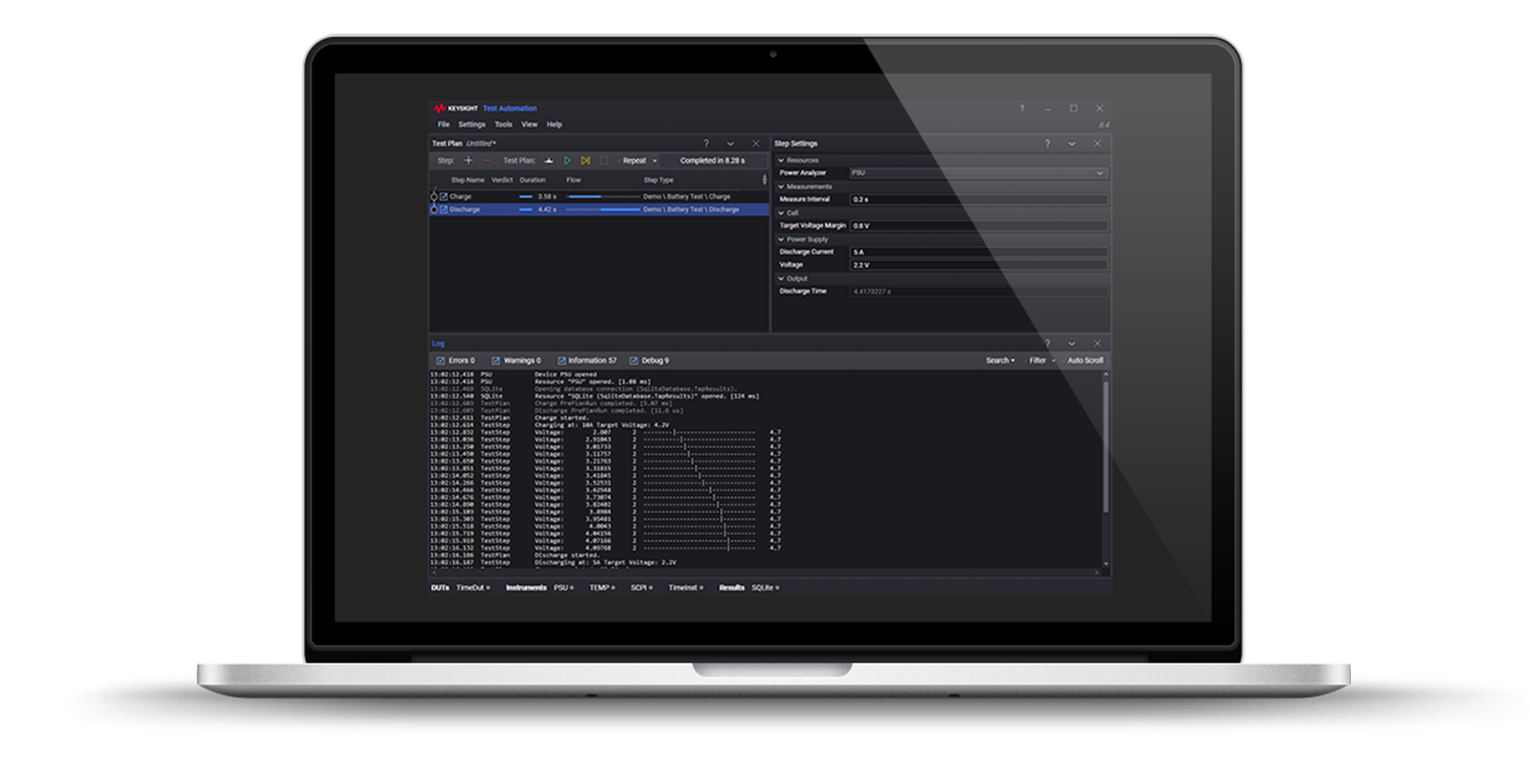
Il collaudo dei moduli di potenza a semiconduttore WBG che operano a correnti e larghezze di banda più elevate richiede il collaudo a doppio impulso con una sonda isolata dagli impulsi. Scoprite come caratterizzare i moduli di potenza in modo affidabile utilizzando il test a doppio impulso per risolvere le sfide di misura high-side.
Per saperne di più