Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
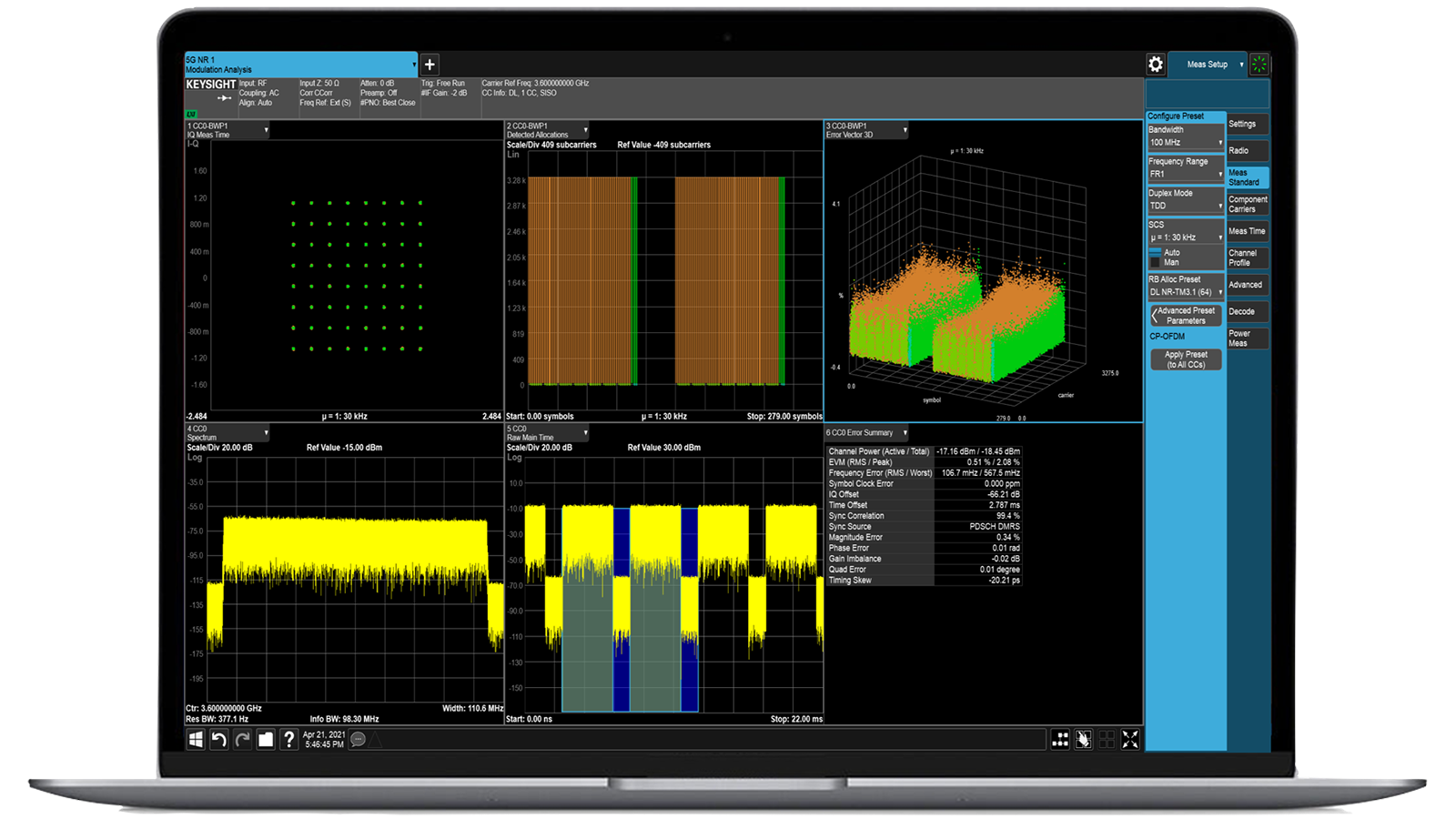
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
- Buy
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
CyPerf Cloud-native tool for realistic traffic and security testing
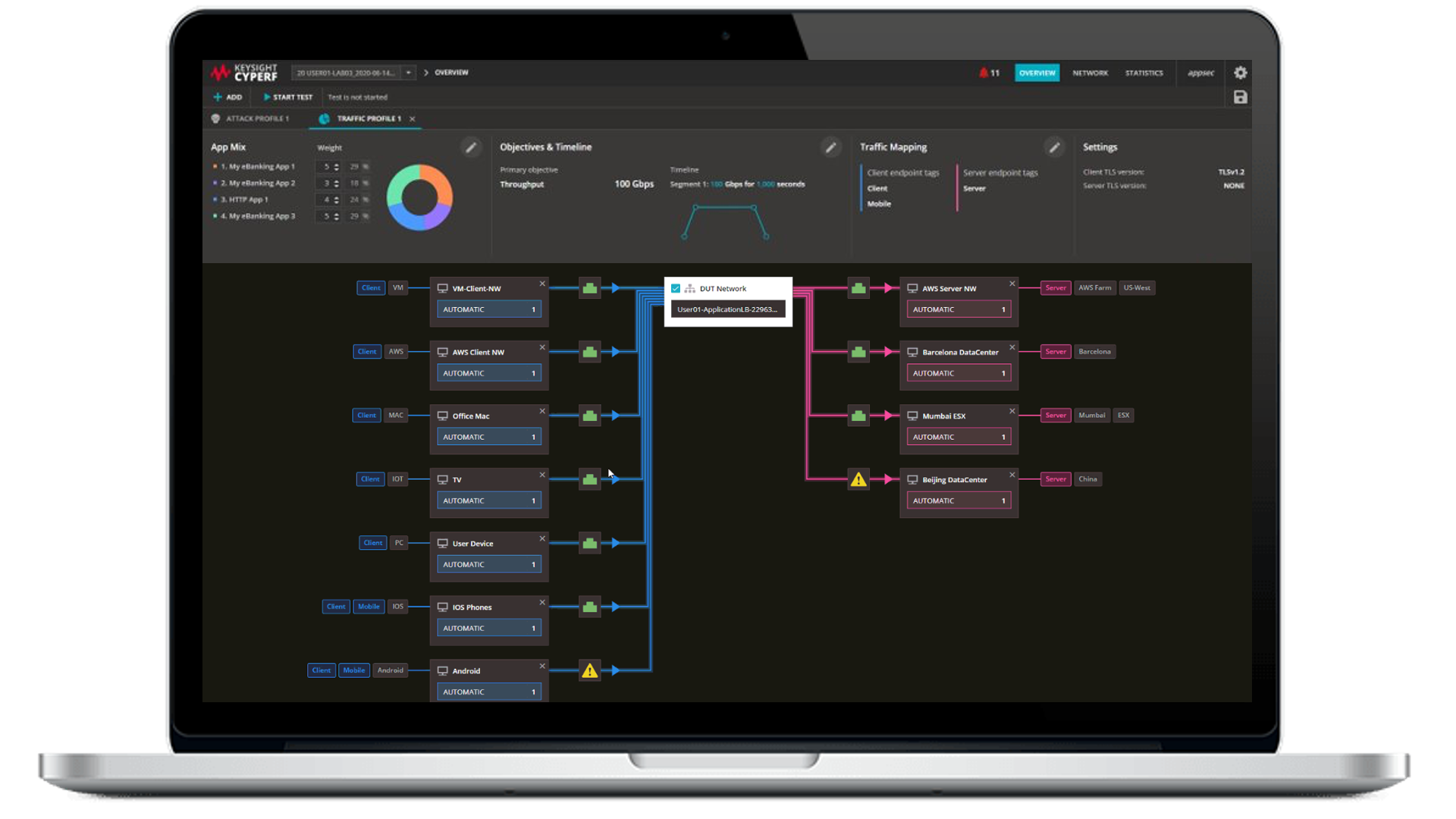
- Overview
- All Models
- Support
Scalable network testing for Zero Trust in distributed cloud environments
Keysight CyPerf software is a true cloud-native testing solution for applications and security, capable of recreating realistic user and network workloads across both physical and cloud-based environments. It scales elastically—supporting millions of users and connections per second—and enables validation of performance and security in modern distributed infrastructures like Secure Access Service Edge (SASE), Zero Trust Network Access (ZTNA), and hybrid architectures. CyPerf supports emulation of encrypted traffic, VPNs, and real-world application behaviors, delivering meaningful insights under scale. Request a quote for one of our popular configurations today. Need help selecting? Check out the resources below.
Realistic encrypted traffic testing
Simulates SSL, TLS, and IPsec traffic at scale to validate security controls and visibility into encrypted environments.
Cloud-native deployment
Runs natively in public, private, or hybrid clouds, allowing performance and security validation across distributed architectures.
Comprehensive use case coverage
Supports testing for SASE, Zero Trust, SD-WAN, and VPN scenarios to ensure resilience under real-world conditions.
Scalable and repeatable validation
Delivers elastic performance testing that scales with network growth, enabling consistent validation from lab to production.
Most popular configurations
CyPerf 2 Agents, 2 Gbps, 30-Days Subscription
CyPerf 2 Agents, 2 Gbps, 30-Days Subscription
938-1101
CyPerf Starter Bundle with 2 Agents and up to 2 Gbps (30-days subscription).
Distributed, Elastic Performance and Security Testing
- Realism
- Create digital twin of users, applications, and attacks to replicate and test QoE in real-world network environments.
- Native authentication
- Send application and security traffic over authenticated sessions at high scale.
- Highly scalable
- Supports millions of concurrent users and millions of connections per second that elastically scale up and down, enabling both resiliency and chaos testing.
- Containerized agents
- Deploy lightweight traffic agents as containerized pods on-prem, VMs, managed Kubernetes deployments, private or public cloud (AWS, GCP, Azure).
- Lab and live network testing
- Test performance and security both pre-deployment in a lab or safely in live production networks.
- Flexible
- Portable subscription-based software solution with a robust and intuitive cloud-native GUI management dashboard.
CyPerf 2 Agents, 10 Gbps, 30-Days Subscription
CyPerf 2 Agents, 10 Gbps, 30-Days Subscription
938-1100
CyPerf Starter Bundle with 2 Agents and up to 10 Gbps (30-days subscription).
Distributed, Elastic Performance, and Security Testing
- Realism
- Create a digital twin of users, applications, and attacks to replicate and test QoE in real-world network environments.
- Native authentication
- Send application and security traffic over authenticated sessions at high scale.
- Highly scalable
- Supports millions of concurrent users and millions of connections per second that elastically scale up and down, enabling both resiliency and chaos testing.
- Containerized agents
- deploy lightweight traffic agents as containerized pods on-prem, VMs, managed Kubernetes deployments, private or public cloud (AWS, GCP, Azure)
- Lab and live network testing
- test performance and security both pre-deployment in a lab or safely in live production networks
- Flexible
- portable subscription-based software solution with a robust and intuitive cloud-native GUI management dashboard
Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently asked questions
Emulating real user behavior requires generating traffic that mirrors not only protocol-level activity but also application-layer actions—such as accessing SaaS services, downloading files, or initiating video calls. Tools like CyPerf offer a rich library of application flows (HTTP/S, DNS, VoIP, Office 365, Zoom, etc.) and allow you to configure traffic patterns with customizable rates, session durations, payload sizes, and encryption protocols. Furthermore, traffic can be distributed across geographically dispersed test endpoints to simulate users in different locations accessing cloud-hosted applications. This emulation helps assess how the network handles concurrent sessions, latency-sensitive tasks, and encrypted traffic, all under real-world load conditions.
Validating Zero Trust requires demonstrating that least-privilege access, segmentation, and inspection policies are consistently enforced across all users, devices, and applications. Zero Trust test solutions supports this by placing agents on both sides of a trust boundary, such as between branches and cloud zones, or users and microservices, and attempting various access scenarios. It emulates allowed and denied traffic, uses encrypted protocols (TLS 1.2/1.3), and includes role-based traffic flows to test authentication and policy enforcement. Reports then detail if and where policies fail, whether packets were dropped or encrypted improperly, and how long it took to establish secure sessions. This allows teams to pinpoint misconfigurations or blind spots in their Zero Trust architecture.
To measure the performance cost of security enforcement, you need to generate controlled traffic through the network path and compare baseline metrics with and without security devices in place. Zero Trust test solutions does this by creating highly repeatable flows at L2–L7, including encrypted sessions, to stress firewalls, secure web gateways, IDS/IPS, and cloud-native security services. It records granular metrics such as throughput, latency, jitter, packet loss, and session setup time. Engineers can then analyze how SSL inspection, application filtering, or deep packet inspection impacts end-user experience under a realistic load. This enables data-driven tuning of security policies without sacrificing performance targets.
SASE and SD-WAN architectures rely heavily on policy-driven routing, encrypted tunnels, dynamic path selection, and cloud-based inspection, all of which must be validated under varying network conditions. Effective simulation tools like CyPerf support distributed agent deployment, allowing you to place traffic generators at branches, cloud gateways, and core nodes. These agents can initiate application-specific traffic flows while measuring performance across tunnels (e.g., IPSec, GRE, SSL VPN) and under failover or degradation conditions. They also emulate security scenarios, such as access from unmanaged devices or attempts to reach restricted SaaS apps, helping teams verify if dynamic policy enforcement, identity-based segmentation, and performance SLAs are met consistently across the SASE or SD-WAN fabric.