Choose a country or area to see content specific to your location
What are you looking for?
-
-
3D Interconnect Designer
3D Interconnect Designer provides a flexible modeling and optimization environment for any advanced interconnect structure, including chiplets, stacked die, packages, and PCBs.

-
Save up to 50% on an XR8 Oscilloscope
Get faster digital validation for less with a trade-in.

-
Discover Keysight AI Data Center Builder
Emulate every part of your data center infrastructure. Emulate Anything. Optimize Everything.

-
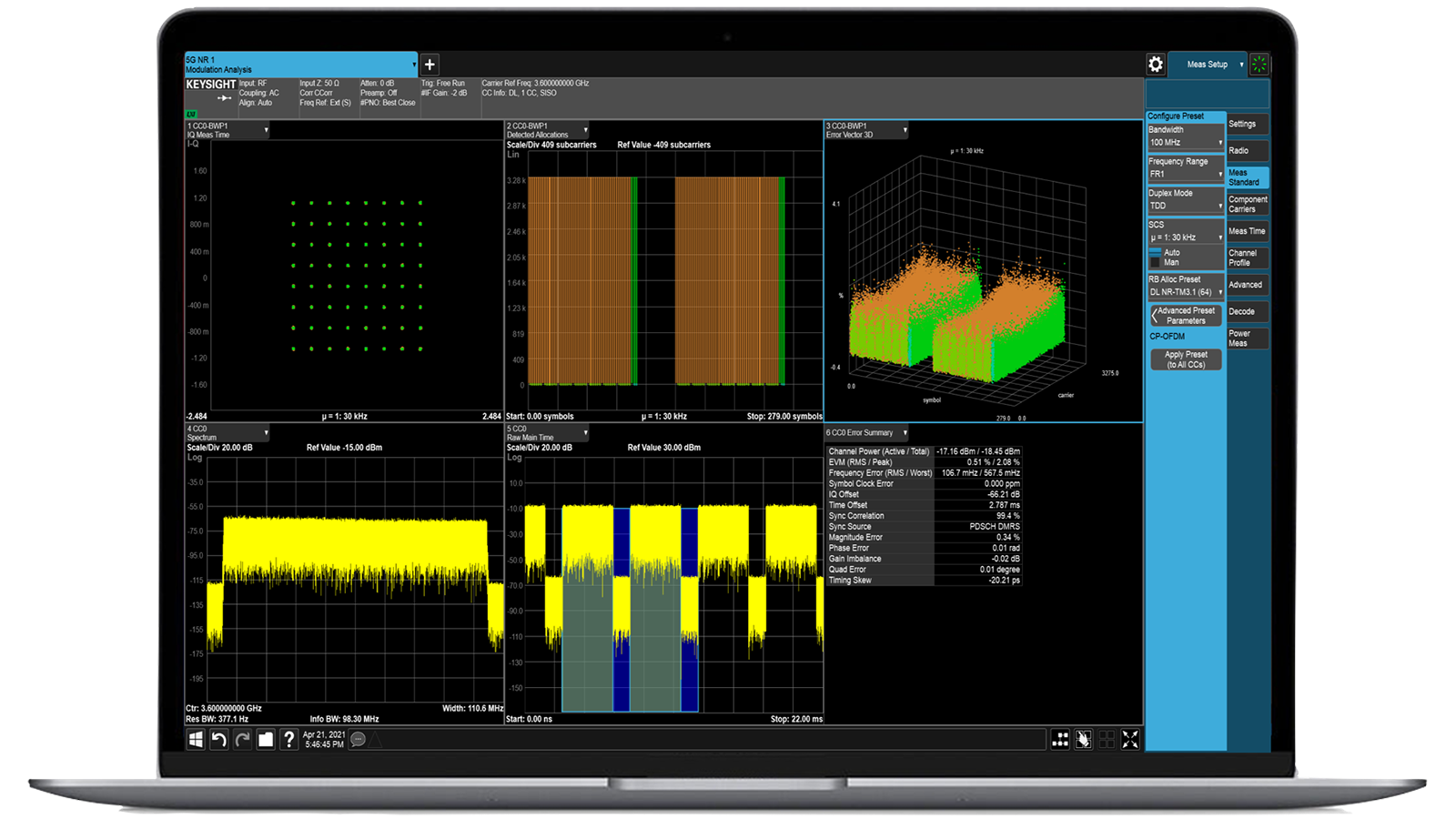
Accelerate Signal Analysis with X-Series Measurement Applications
Use 25+ X-Series applications to analyze, demodulate, and troubleshoot signals across wireless, aerospace/defense, EMI, and phase noise.

-
Introducing AI-Enhanced Packet Brokers
With extra memory and storage, these enhanced NPBs run Keysight's AI security and performance monitoring software and AI stack.

-
Precision In-Circuit Testing for Production
Achieve fast, accurate board-level testing with robust inline and offline ICT designed for modern manufacturing.

-
Accelerate Your Innovation Engine
Explore curated support plans, prioritized to keep you innovating at speed.
-
448 Gb/s Waveform Generation
Achieve 200+ Gbaud multi-level modulated signals with high-speed AWGs for digital and optical standards.

-
Stream 120 MHz I/Q Data to Your Laptop in the FieldPinpoint interference with post-processing spectrum management software in the lab.
 Find the Right ATE Power Solution
Find the Right ATE Power SolutionUse this selector tool to quickly identify the best power supply for your aerospace and defense ATE requirements.

-
- Solutions
-
Explore engineer-authored content and a vast knowledge base with thousands of learning opportunities.
FeaturedKeysight Learn offers immersive content on topics of interest, including solutions, blogs, events, and more.
-
Quick access to support related self-help tasks.
Additional content to support your product needs.
Do more with Keysight ServicesExplore services to accelerate every step of your innovation journey.
Security Attack Emulation
Dynamic security intelligence to stay one step ahead of attacks

-
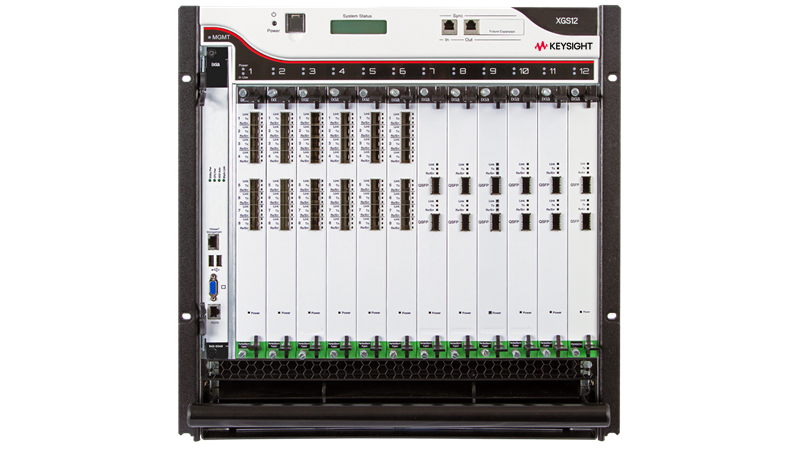
Hardware Accelerators for Security Test
Enterprise-wide application and security testing from anywhere

-
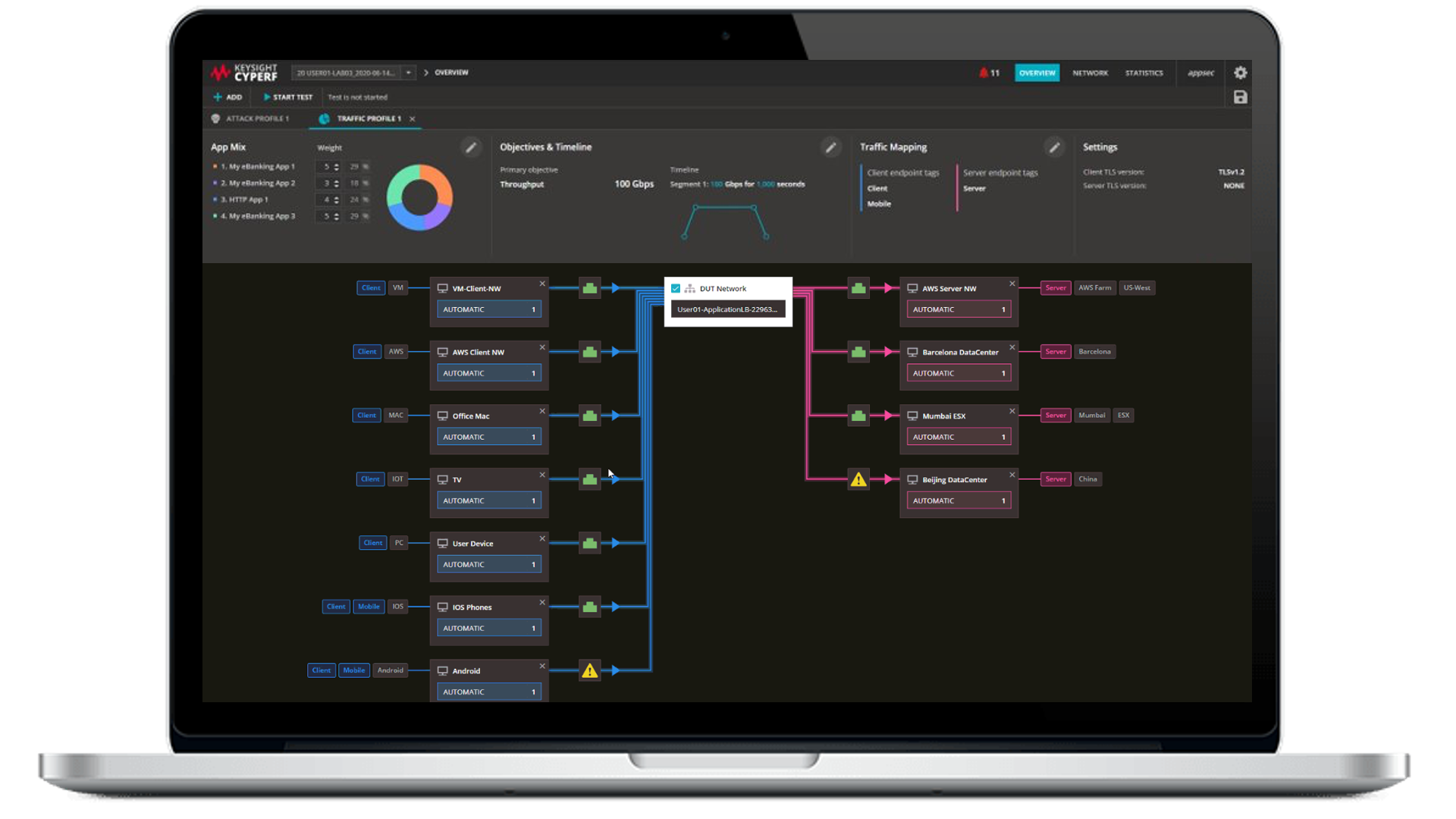
Security Attack Emulation Software
Simulate sophisticated attacks, validate controls, and ensure cyber readiness

Hardware Accelerators for Security Test
Keysight hardware accelerators for security test deliver realistic, high-stress validation of network infrastructure, from simulating millions of users to reproducing encrypted traffic and malicious threats. Built for speed, scalability, and precision, they help teams uncover performance and security gaps before deployment. Ideal for enterprise, telecom, and cloud providers, these platforms ensure firewalls, traffic systems, and ultra-low latency networks meet real-world demands. With unmatched realism and control, the hardware accelerators enable meaningful results you can trust. Need help selecting? Check out the resources below.
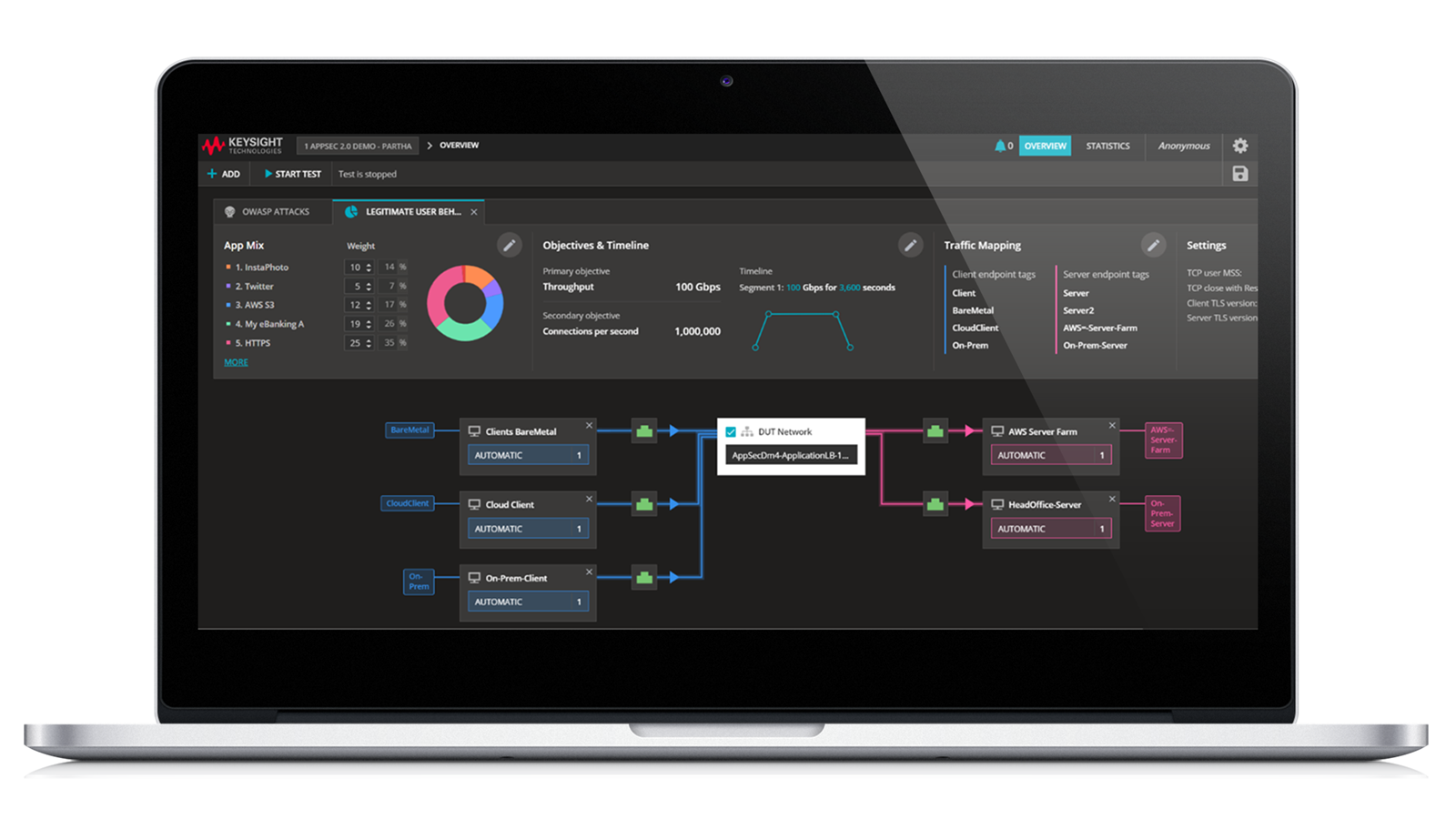
Security Attack Emulation Software
Keysight security attack emulation software enables organizations to continuously assess and improve their cyber resilience. Whether deployed in cloud-native pipelines, virtual environments, or production networks, these solutions offer realistic traffic, up-to-date threat intelligence, and full-stack validation. Use these solutions to validate Zero Trust architectures, test enforcement points, or expose gaps in detection and response workflows. Our emulation software empowers security, DevOps, and compliance teams to test with confidence, without risking production environments. Need help selecting? Check out the resources below.
Hardware Accelerators for Security Test
Keysight hardware accelerators for security test deliver realistic, high-stress validation of network infrastructure, from simulating millions of users to reproducing encrypted traffic and malicious threats. Built for speed, scalability, and precision, they help teams uncover performance and security gaps before deployment. Ideal for enterprise, telecom, and cloud providers, these platforms ensure firewalls, traffic systems, and ultra-low latency networks meet real-world demands. With unmatched realism and control, the hardware accelerators enable meaningful results you can trust. Need help selecting? Check out the resources below.
Hardware Accelerators for Security Test
Keysight hardware accelerators for security test deliver realistic, high-stress validation of network infrastructure, from simulating millions of users to reproducing encrypted traffic and malicious threats. Built for speed, scalability, and precision, they help teams uncover performance and security gaps before deployment. Ideal for enterprise, telecom, and cloud providers, these platforms ensure firewalls, traffic systems, and ultra-low latency networks meet real-world demands. With unmatched realism and control, the hardware accelerators enable meaningful results you can trust. Need help selecting? Check out the resources below.
Security Attack Emulation Software
Keysight security attack emulation software enables organizations to continuously assess and improve their cyber resilience. Whether deployed in cloud-native pipelines, virtual environments, or production networks, these solutions offer realistic traffic, up-to-date threat intelligence, and full-stack validation. Use these solutions to validate Zero Trust architectures, test enforcement points, or expose gaps in detection and response workflows. Our emulation software empowers security, DevOps, and compliance teams to test with confidence, without risking production environments. Need help selecting? Check out the resources below.
Security Attack Emulation Software
Keysight security attack emulation software enables organizations to continuously assess and improve their cyber resilience. Whether deployed in cloud-native pipelines, virtual environments, or production networks, these solutions offer realistic traffic, up-to-date threat intelligence, and full-stack validation. Use these solutions to validate Zero Trust architectures, test enforcement points, or expose gaps in detection and response workflows. Our emulation software empowers security, DevOps, and compliance teams to test with confidence, without risking production environments. Need help selecting? Check out the resources below.

Validate Zero Trust in distributed cloud environments
Protecting modern distributed cloud environments requires solutions that combine realism, scalability, and confidence. Keysight security attack emulation platform enables you to validate Zero Trust architectures against real-world traffic, encrypted workloads, and advanced attack scenarios at hyperscale speeds up to 400GE. With comprehensive performance and security validation, you can uncover weaknesses early, optimize defenses, and stay ahead of evolving cyber threats with confidence.
Find Compatible Software and Accessories for Your Security Attack Emulation Solution
Choose from a wide variety of security, control, and application-specific software or accessories like cables, high-performance network interface cards, timing modules, rack mount kits, and more.
Explore Security Attack Emulation Use Cases
Support for a wide-range of applications across various industries, discover them all.
Wired Communication
Validating zero-trust networks with real-world traffic and attack emulation.
Enterprise IT
Securing critical IoT deployments with device security testing and breach and attack simulation.

Wireless Communication
Conformance testing for IoT devices with automated security assessment.

Enterprise IT
Validating voice and video quality of service with synthetic monitoring.

Enterprise IT
Testing VPN access and performance with synthetic monitoring.

Services and support
Innovate at speed with curated support plans and prioritized response and turn-around times.
Get predictable, lease-based subscriptions and full lifecycle management solutions—so you reach your business goals faster.
Experience elevated service as a KeysightCare subscriber to get committed technical response and more.
Ensure your test system performs to specification and meets local and global standards.
Make measurements quickly with in-house, instructor-led training, and eLearning.
Download Keysight software or update your software to the newest version.
Frequently Asked Questions
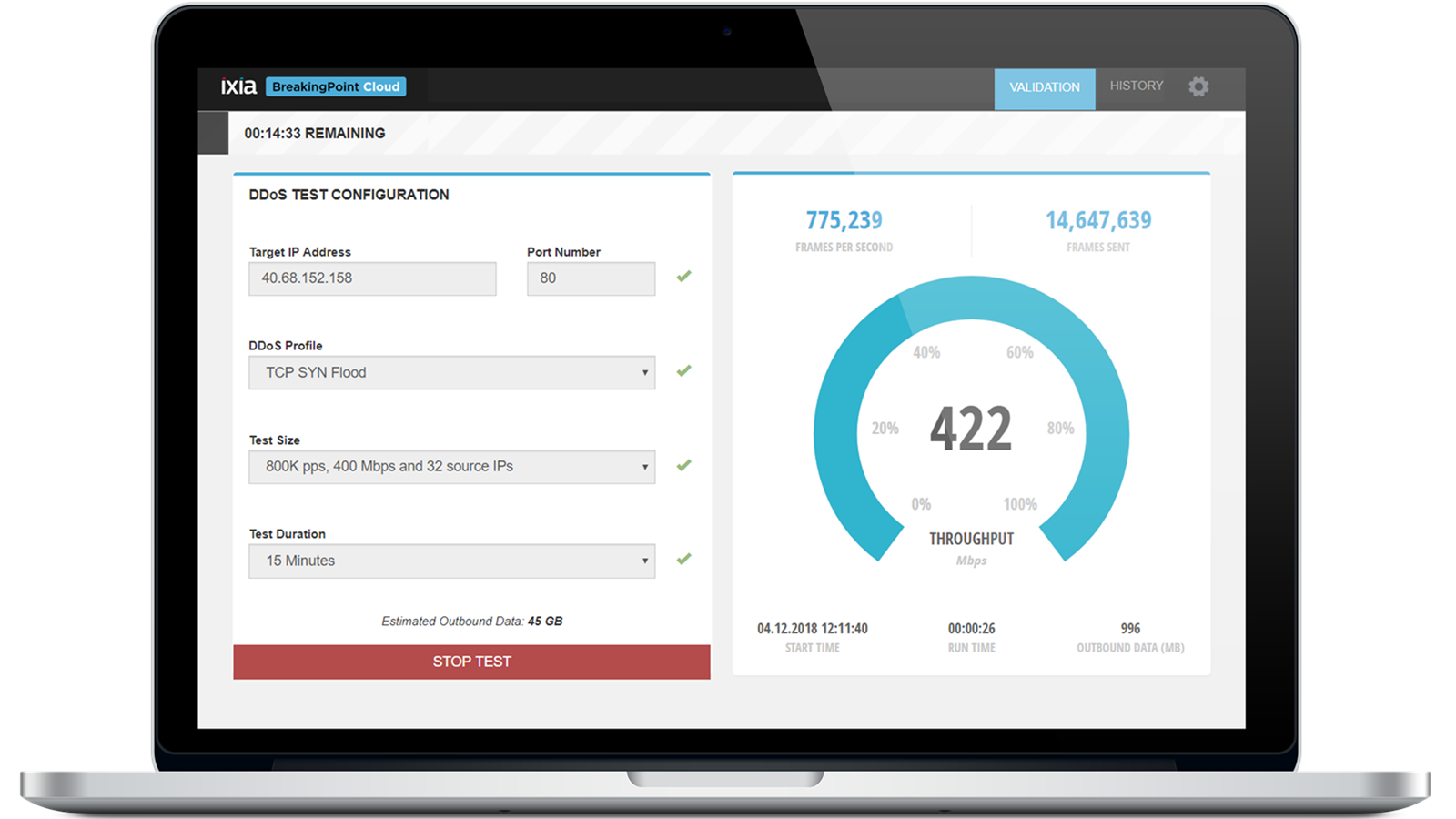
Security attack emulation is the controlled reproduction of realistic threats and legitimate traffic to validate whether security controls perform as intended in a target environment.
The right solution should align to the deployment model, network scale, traffic realism, and validation objective across enterprise, cloud, or telecom use cases, while supporting relevant security validation frameworks and measurable outcomes. Key outcomes include attack detection rates, false positive reduction, latency impact, throughput under load, and control stability during mixed traffic conditions. Keysight supports these validation needs across production networks, virtual environments, and cloud-native pipelines.
A security attack emulation solution is a system that reproduces realistic threats and application traffic to validate security controls under realistic conditions.
Key capabilities include threat intelligence, traffic realism, scalability, automation, and full-stack validation across security enforcement points. These capabilities matter because security validation depends on measurable outcomes such as blocked attack rates, detection coverage, latency, throughput, encrypted traffic handling, and repeatability across test cycles. Keysight enables these validation workflows across production networks, virtual environments, and cloud-native environments.
Security attack emulation reproduces realistic threats and legitimate traffic in a controlled, repeatable environment to measure how defenses perform under load.
Key outcomes include detection effectiveness, latency, throughput, and resilience under realistic conditions. Penetration testing is an expert-led effort focused on identifying exploitable weaknesses within a defined scope. Breach and attack simulation (BAS) is typically an automated approach used to continuously validate whether security controls detect and respond to known attacker behaviors. In practice, attack emulation emphasizes realistic validation outcomes for enterprise, cloud, and telecom security environments, while penetration testing emphasizes findings and BAS emphasizes continuous control validation. Keysight supports these security validation workflows across modern enterprise environments.
Security attack emulation integrates into DevSecOps, CI/CD pipelines, and continuous security validation workflows by providing repeatable, automated threat and traffic scenarios that can run throughout the release cycle.
This supports measurable outcomes such as detection efficacy, latency impact, throughput degradation, policy enforcement consistency, and regression tracking after code, configuration, or infrastructure updates. Keysight applies security attack emulation to continuous validation across cloud-native pipelines, virtual environments, and production networks.
Attack emulation validates how security controls and systems respond to realistic threats, legitimate traffic, encrypted workloads, and mixed operating conditions. This includes firewalls, intrusion prevention systems, Zero Trust architectures, enforcement points, and detection and response workflows across enterprise, cloud, and telecom environments.
Measurable outcomes include block rates, detection coverage, latency under inspection, throughput under attack, and service continuity during high-stress conditions. Keysight supports attack emulation for these security validation workflows.
Security attack emulation effectiveness and ROI are measured by how validation results demonstrate improvements in security posture over time.
Useful measures include detection rates, blocked threat volume, reduced configuration gaps, lower false positives, stable latency and throughput under attack, faster remediation cycles, and fewer control failures during enterprise validation exercises. Detailed analytics, structured reporting, and repeatable audit-ready scenarios also support continuous improvement and compliance reporting. Keysight supports ongoing security validation that helps strengthen cybersecurity posture.
Security attack emulation evaluates how firewalls, intrusion prevention systems, and other security appliances respond to realistic threats, legitimate traffic, encrypted workloads, and mixed operating conditions. Key outcomes include block rates, detection coverage, latency under inspection, throughput under attack, and service continuity.
This form of security validation helps identify blind spots, misconfigurations, and performance bottlenecks that may not appear in isolated testing. Keysight supports attack emulation for validating modern security controls across enterprise, cloud, and telecom environments.
Security attack emulation is the controlled reproduction of realistic threats and legitimate traffic to validate how security controls perform under real operating conditions. Important outcomes include detection effectiveness, latency impact, throughput under load, policy resilience, and service continuity during mixed traffic scenarios.
It is important for modern cybersecurity validation because static or isolated testing often misses how controls behave under encrypted traffic, application traffic, and concurrent attacks. Keysight supports security attack emulation for validation across production networks, virtual environments, and cloud-native infrastructures.